Hey Folks, in this tutorial we are going to discuss about a well-known brute forcing tool called “Ncrack“. About Ncrack : Ncrack is a high-speed network authentication cracking tool. It was built to help companies secure their networks by proactively testing all their hosts and networking devices for poor passwords. Ncrack’s features include a very flexible interface granting the user full control of network operations, allowing for very sophisticated brute forcing attacks, timing templates for ease of use, runtime interaction similar to Nmap’s and many more. It support various protocol such as SSH, RDP, FTP, Telnet, HTTP(S), WordPress etc.
Lets take a look 🙂 !!
Installation
Its not possible that you have kali linux operating system at all time, that is why we have given a command to install this tool in any operating system. If you use any android application, you can still use the “pkg” command.
apt-get install ncrack
or
pkg install ncrack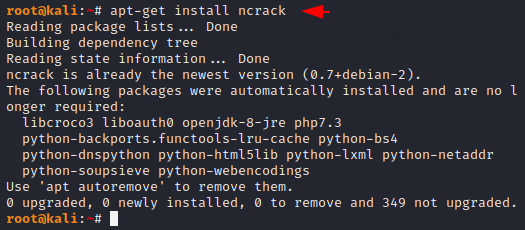
Usage ( help )
We can use the following command to check the options available in this tool.
ncrack -h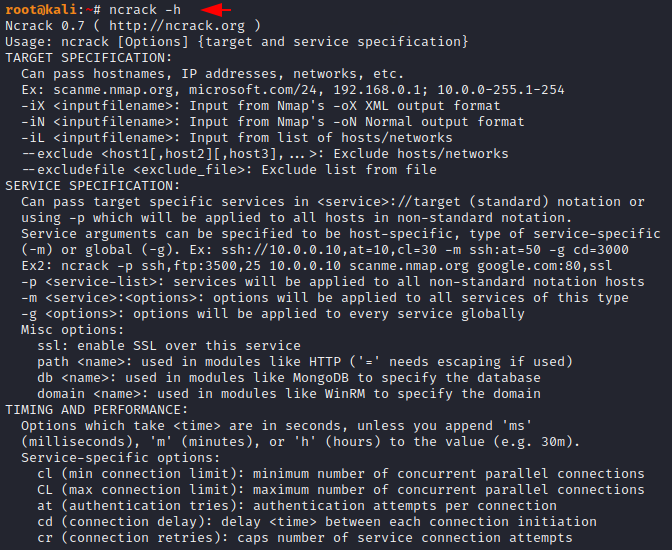
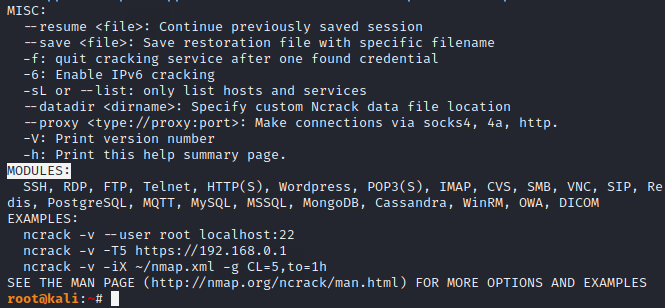
Modules
Also, you can see all available modules in this tool.
Anonymous Login
The FTP service has an anonymous login feature that is often enabled but we are unable to access it due to not having password. But through the following command you can get exact credentials to login into the service.
ncrack ftp://192.168.1.11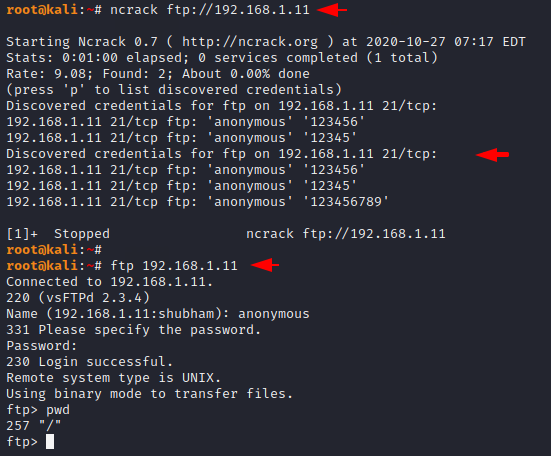
Crack Login
Just you can use the following command to crack the login of FTP service. Both commands will do the same thing, so you can choose according to yourself. See below to understand the command.
Usage 🙂 !! ncrack -U < username list > -P < password list > ftp://<host>
- -U : list of usernames
- -P : list of passwords
ncrack -U username.txt -P password.txt ftp://192.168.1.11
ncrack -U username.txt -P password.txt 192.168.1.11:21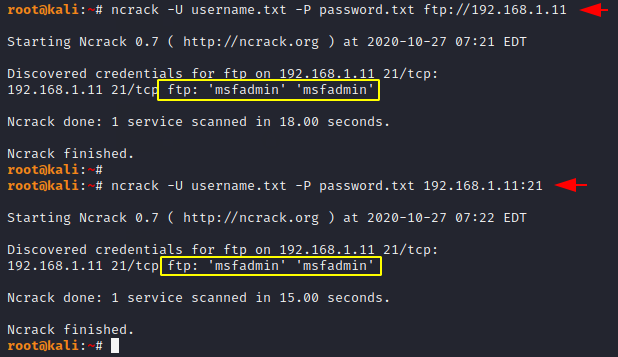
Guessing Password for Specific User
If the username is confirmed but the password has to be found then you can use the following command.
Usage 🙂 !! ncrack –user < username > -P < password list > ftp://<host>
ncrack --user shubham -P password.txt 192.168.1.11:21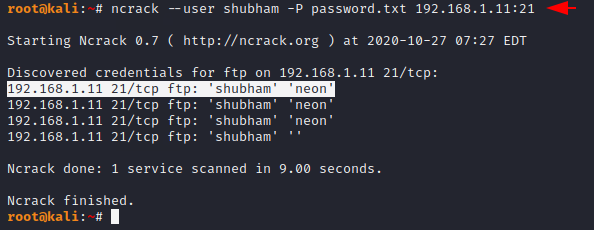
Guessing Username
Suppose if you have a user’s password, but you do not know the username, then you should use the following command to find the correct user.
Usage 🙂 !! ncrack -U < username list > –pass < password > ftp://<host>
ncrack -U username.txt --pass neon 192.168.1.11:21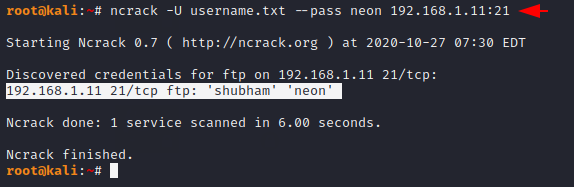
Verbose Mode
By using verbose mode we can get some additional information such as you can see in the image below.
ncrack -U username.txt --pass neon 192.168.1.11:21 -v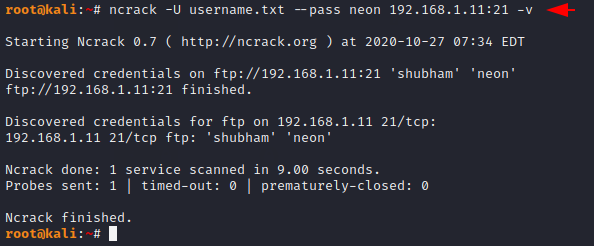
Save Output ( TXT )
We can save the result in a text file with the help of given below command. Just you need to add “-oN” option to the command.
ncrack -U username.txt -P password.txt ftp://192.168.1.11 -oN res.txt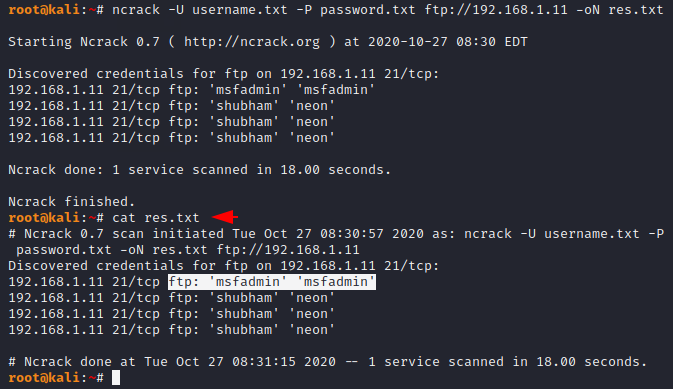
Save Output ( XML )
We can save the entire result in XML format using the “-oX” option.
ncrack -U username.txt -P password.txt ftp://192.168.1.11 -oX res.xml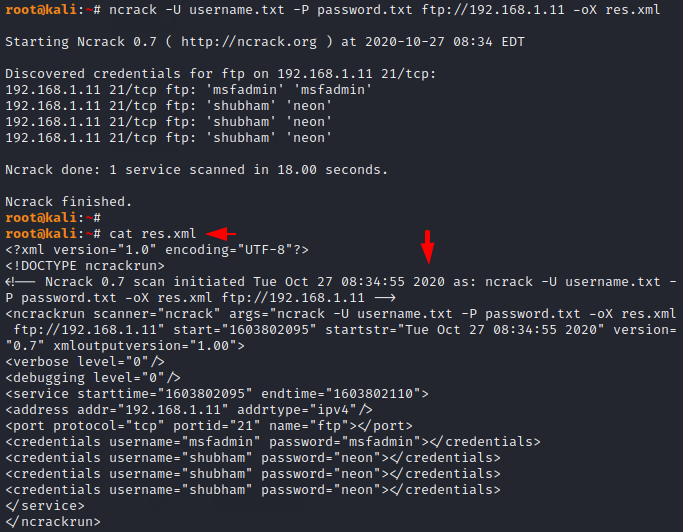
Save Results in All Format
If you want to store the entire ncrack results in all formats such as XML, TXT, Ncrack etc then you can use the following command.
ncrack -U username.txt -P password.txt ftp://192.168.1.11 -oA sec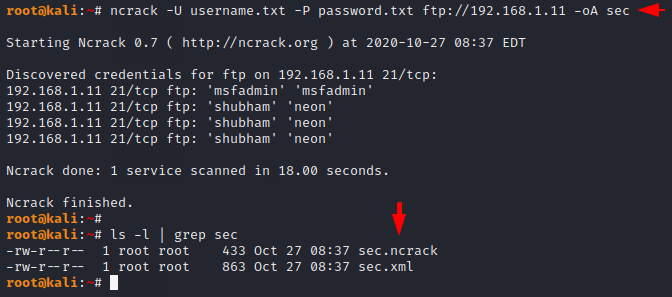
Stop on Success
Often the tools continues to crack the login even after obtaining the correct credentials, hence to avoid this we use the following feature to stop on first success.
ncrack -U username.txt -P password.txt 192.168.1.11:21 -f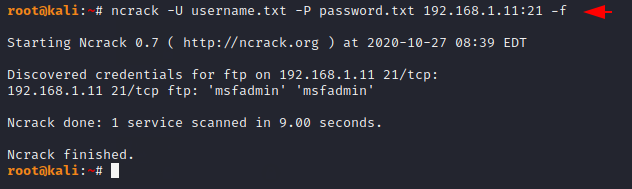
Multiple Hosts
If you want to perform brute force attack on multiple hosts at the same time then you can use “-iL” option.
ncrack -U username.txt -P password.txt -iL host.txt -p21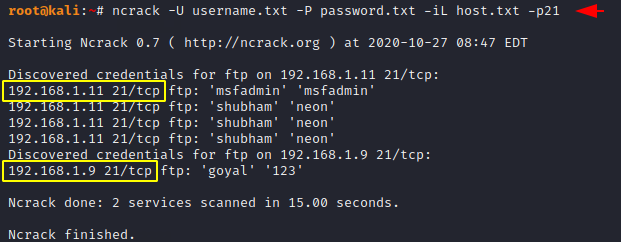




Excellent post. I was checking constantly this blog and I’m
impressed! Extremely helpful information particularly
the last part 🙂 I care for such information a lot.
I was looking for this particular information for a very long time.
Thank you and good luck.
Thanks for your valuable time 🙂 !!