Hey Folks, as we know that sometimes in a CTF challenge, we need some steganography skills to secret a key or a hint and for that we discover a variety of tools on Github, but today we has brought two steganography tools for you that you can use in your CTF labs.
Tools for Steganography
- Steghide – To hide string or key in any file format.
- Stegbrute – To crack password and extract string from JPEG file.
Let’s take a look 😛 !!
Stegbrute Tool Installation
Stegbrute is a fast steganography brute force tool written in Rust using also threads to achieve a faster execution. This is not a pre-installed tool so we have to install it first using the wget command and then move it to the binary folder to access it from anywhere.
wget https://github.com/R4yGM/stegbrute/releases/download/0.1.1/stegbrute && chmod +x stegbrute
mv stegbrute /usr/local/bin/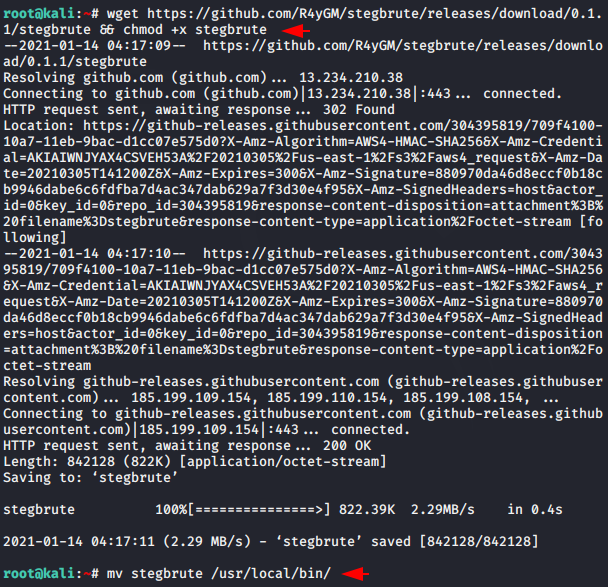
Done 😛 !! As you can see in the image below, we can now use this tool just by entering the name.
stegbrute
Steghide Tool Installation
Steghide is a steganography program that is able to hide data in various kinds of image- and audio-files. The tool is already connected to the kali linux repository and that is why we are able to install it using the “apt-get” command.
apt-get install steghide
Done 😛 !! Both tool are now successfully installed to demonstrate an example of steganography. First we will create a text file, hide the text file in JPEG file using Steghide tool and protect it with a password.
Usage 😛 !! steghide embed -cf < JPEF file > -ef < File that you want hide >
cat > secret.txt
steghide embed -cf jpg-vs-jpeg.jpg -ef secret.txt
Amazing 😛 !! As we know the Stegbrute tool uses wordlist to extract hidden content out of the file. Now all you have to do is to give this tool the location of the JPEG file and the wordlist and immediately after that it will try to crack it using multiple passwords. After the password is successfully cracked, we get the secret string in the result file that we previously hidden.
Usage 😛 !! stegbrute -f < Protected File > -w < Wordlist Path >
stegbrute -f jpg-vs-jpeg.jpg -w word.txt
In the same way you can hide any secret key and use these tools to prompt the user in your CTF labs.





I am sure this post has touched all the internet users, its really really nice paragraph on building up
new blog.
Thanks 🙂 !!
I’ve been exploring for a bit for any high-quality articles or weblog posts in this sort of space .
Exploring in Yahoo I eventually stumbled upon this site.
Reading this info So i am happy to convey that I have a very just
right uncanny feeling I discovered just what I needed.
I such a lot indubitably will make certain to don?t omit this web site and give it a glance regularly.
Thanks for your valubale feedback 🙂 !!
I’m геally enjοying the dеsign and layout of
your site. It’s a ѵery easу on the eyes which makes
it much more pleasant for me to come here and visit more often. Did you hire out a desіgner to create your theme?
Exceptional wߋrk!
Thanks for your valubale feedback 🙂 !!
Yes we have already hired a designer.
I could not resist commenting. Well written!