Hey Folks, in this tool tutorial we are going to present a profile based osint tool named “Profil3r“. Profil3r is an OSINT tool that allows you to find potential profiles of a person on social networks, as well as their email addresses. This program also alerts you to the presence of a data leak for the found emails.
Let’s take a look 🙂 !!
Requirements
During the installation of this tool we will need the python utility, so it should be in your system and if you have not then you can install it using the following command.
apt install python3 pythonProfil3r Tool Installation
Now is the right time to install this tool. We have given below three commands below which you have to execute simultaneously. After doing all this, you will be able to use this tool. If you find any error then you can contact us through the comment on the post.
git clone https://github.com/Rog3rSm1th/Profil3r.git
cd Profil3r/
python3 setup.py install
Done 🙂 !! As always, this tool also has a help command that you can use to learn about the use of command’s that is in this tool.
python3 profil3r.py -h
Example – OSINT
Only we need to leave the name of the target in the command and it will keep asking us everything step by step. As soon as we execute the command we get a selective based interface where first we need to select the format for the user.
Usage 🙂 !! python3 profil3r.py -p < name >
python3 profil3r.py -p secnhack
Now we have to select a specific service and you can choose accordingly. But in our case we want to check the domain of the given name and its social profiles.

Good 🙂 !! As you can see how easily all social media profiles related to the domain have been dumped.

OSINT ( User Profiles )
We will implement the same procedure to find the user profile.

OK 🙂 !! Just move your cursor down and choose the social option.
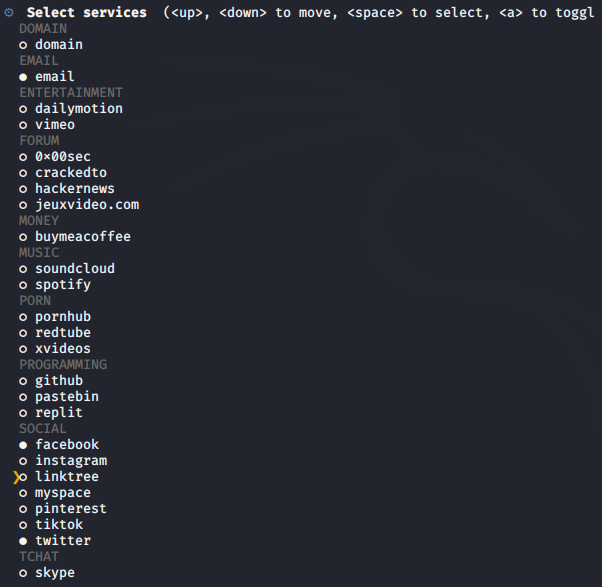
Great 🙂 !! Now we get many profiles with the same name that we gave, so now you can open it one by one and get the exact profile.