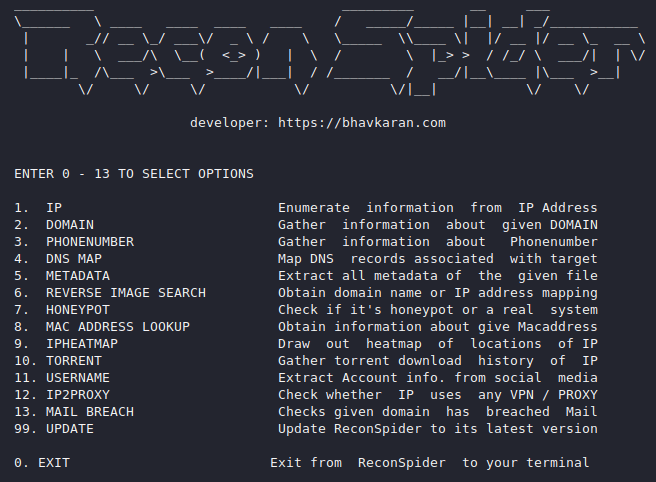
Hey guys, in this tutorial we are going to discuss about an interesting tool that can help those who learn ethical hacking. The tool name is “Recon Spider” that has included almost all the features which you will learn in ethical hacking. Reconnaissance is combination of techniques (Footprinting, Scanning & Enumeration) used to deep discover and collect information about a target system. You will benefit from this tool that you can understand and perform attacks with basic knowledge.
Lets take a look 🙂 !!
Installation
To successfully configure this tool we need to download it from github page whose command is given below. But we must meet some requirements of this tool before installation.
git clone https://github.com/bhavsec/reconspider.git
sudo apt install python3 python3-pip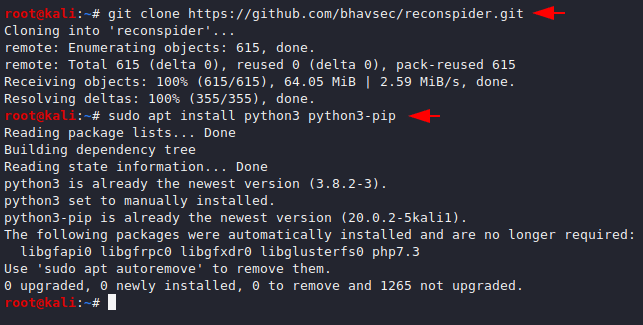
Now we go to the directory and execute the below command command to setup this tool.
cd reconspider
sudo python3 setup.py install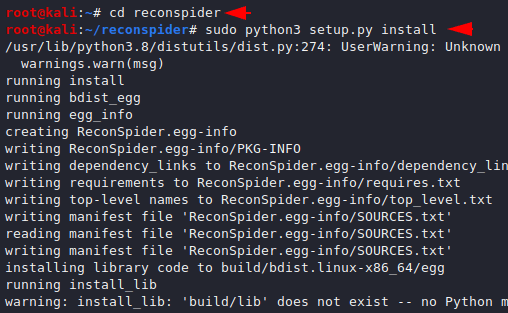
Done 🙂 we have done all the configuration and installation and now we can start this tool by using python tool.
python3 reconspider.py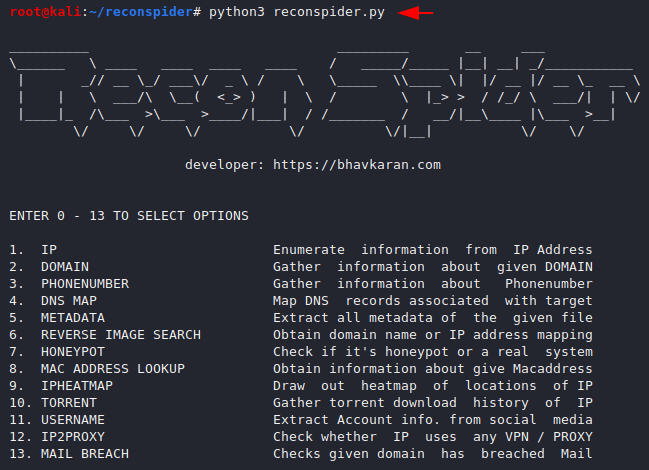
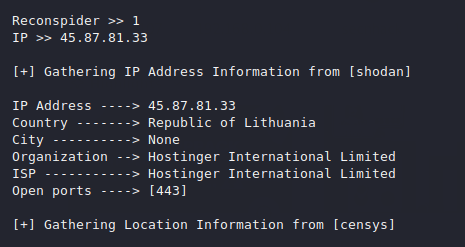
Enumerate IP Address
We think you might have understood how this tool is used, which means that we will not have to put a lot of effort as it will do all the work itself after giving numerical input. In our first example you can see below that it gives us all the details related to the IP address after inputting it.
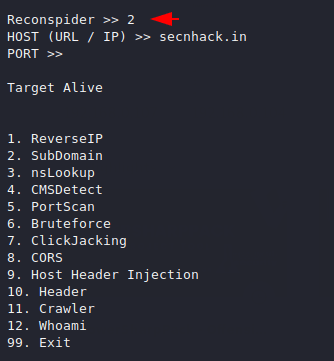
Domain Enumeration
Now we will try to find the details about the particular website. To do this we will enter “two” and after that it will provide us all the facilities that we can use.
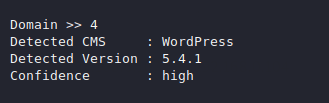
CMS Detection
Through this technique we can identify which platform the website is built on and if a component and version is vulnerable then we can exploit that vulnerability.
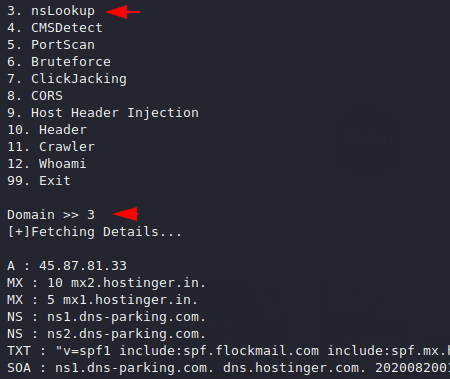
Nslookup
This features allow an attacker to obtain domain name or IP address mapping, or other DNS records by giving the name of the website.
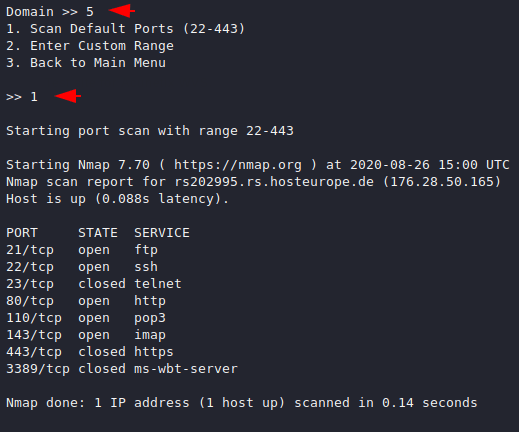
PortScan
This tool has port scanning features that can be helpful for beginners to do port scanning against the live website.
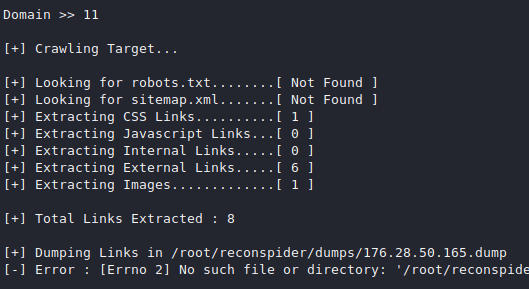
Crawling
Crawling is the discovery process in which search engines send out a team of robots to find new and updated content.
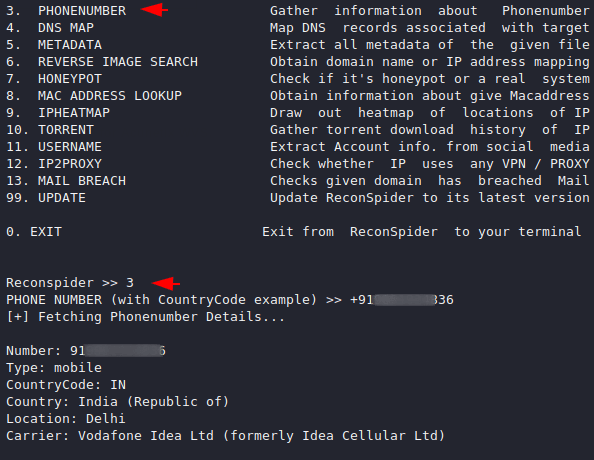
Phone number Enumeration
Phone number information gathering is technique from which we can obtain information through the phone number such as : Countrycode, Types, Location etc.
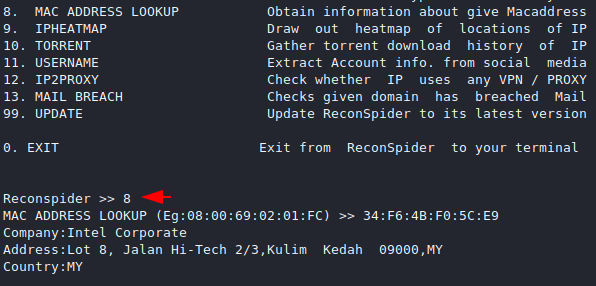
MAC Address
Here you can see that we have successfully detected the MAC address of the target machine.
This is not enough so you can use all the features yourself and get more information about the target.




Reconspider >> 3
PHONE NUMBER (with CountryCode example) >> +******************
[+] Fetching Phonenumber Details…
Your monthly usage limit has been reached <==== ??????????????????????