Hey Folks, in this tutorial we are going to talk about an interesting tool called “r3con1z3r“. We know that it very difficult to pronounce this name 😛 !! but through this tool footprinting can be conducted quickly and thoroughly. R3con1z3r is a lightweight Web information gathering tool with an intuitive features written in python. Footprinting is the first phase of ethical hacking, its the collection of every possible information regarding the target. R3con1z3r is a passive reconnaissance tool with built-in functionalities which includes: HTTP header flag, Traceroute, Whois Footprinting, DNS information, Site on same server, Nmap port scanner, Reverse Target and hyperlinks on a webpage.
Let’s take a look 😛 !!
Installation
r3con1z3r depends only on the sys and the requests python modules as well as it supports Python 2 and Python 3. But to install this tool, another important thing that we need to install is pypi.
apt install pip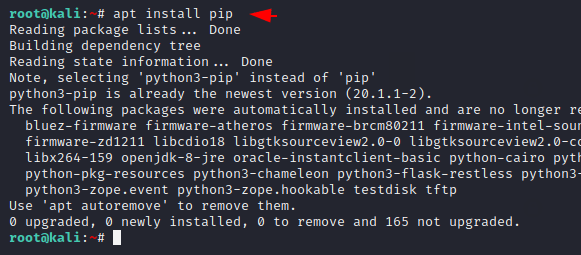
Now the tool can be installed using the pip tool.
pip install r3con1z3r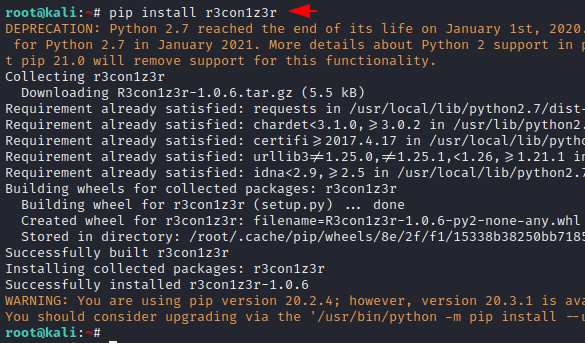
Done 🙂 !! You can see how little time we have installed this tool. Now we can use it from anywhere by entering the name of this tool on the terminal.
r3con1z3r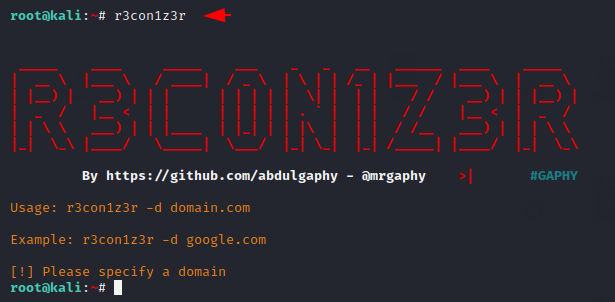
Usage
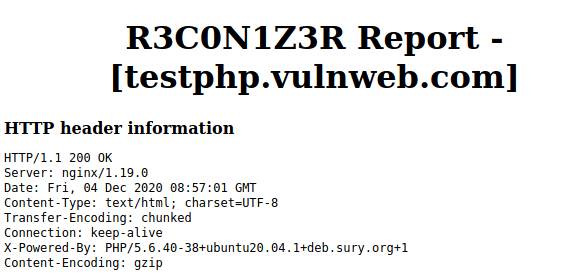
Just we have to name the target web application after the “-d” parameter and it will generate the output in HTML format that we have already highlighted in yellow colors.

Results – Header Information
We need to paste the output to its appropriate location after which we can open it on any available browser due to the HTML extension. We can clearly see all the important details regarding the server.
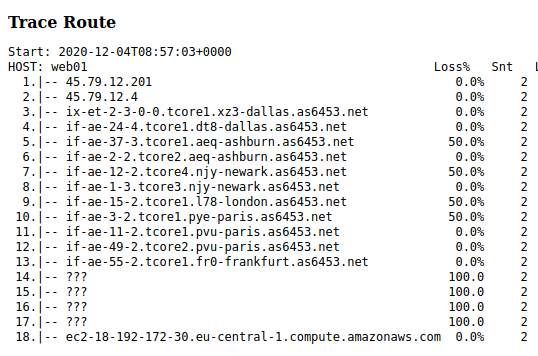
Trace Route
Basically traceroute is a computer network command that is used to measure the transit delay of packets in an Internet protocol network.
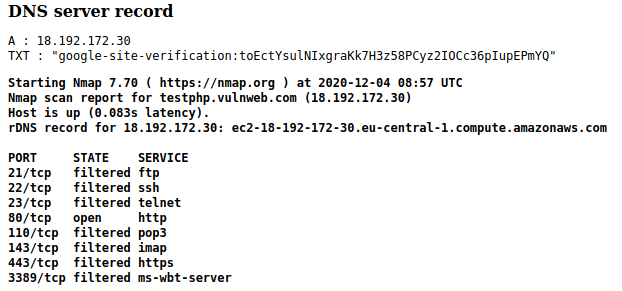
DNS Server Records & Ports
We can see domain name system records as well as open and running services on target web application.
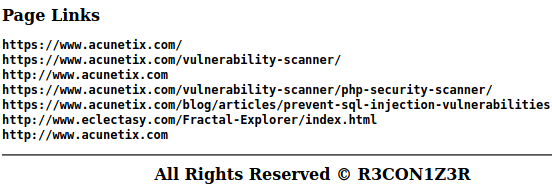
Crawling
It also crawl some hidden locations, files or link from target web application.