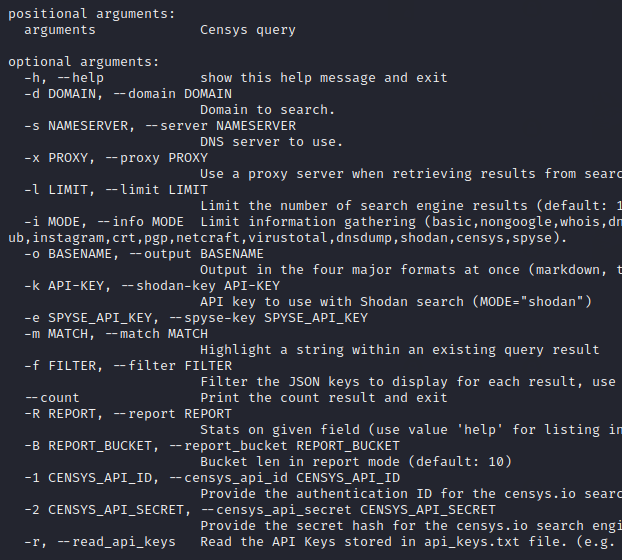
Hey Folks, in this tutorial we are going to talk about an all in one tool called “gasmask“. Originally the tool is designed to get different types of information against the target system or web application. It uses various other third-party tools to collect sensitive information against targets such as the dnsdumpster tool, whys, etc.
Let’s take a look 🙂 !!
Installation
We can easily configure this tool in our system by just following these steps. First of all we execute the git clone command to download this remote repository from the destination. After downloading is done then we go to the directory of this tool and install some dependencies by using the pip3 tool.
git clone https://github.com/twelvesec/gasmask.git
cd gasmask/
sudo pip3 install -r requirements.txt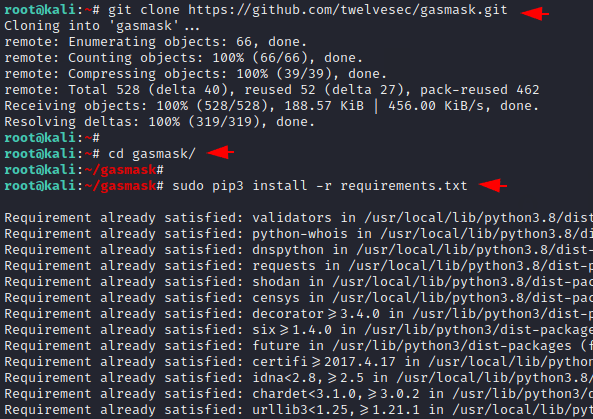
Done 🙂 !! After doing all the above things we can boot our tool using the below command.
python3 gasmask.py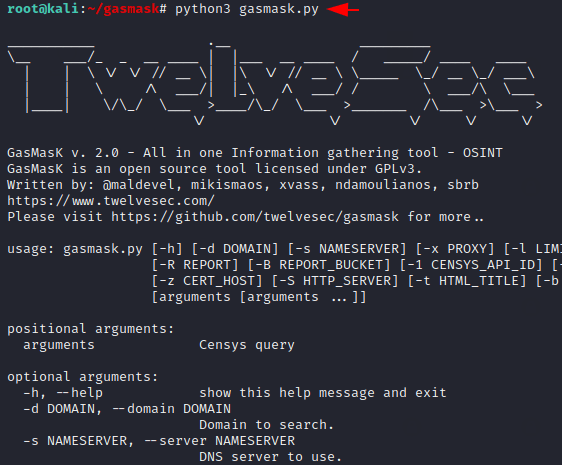
Basic Scan
This tool has basic features that anyone can easily use. If we want to perform a basic scan against the target then all we need to do is to set our target details along with the commands given below.
Usage 😛 !! python3 gasmask.py -d < domain name > -i basic
python3 gasmask.py -d testphp.vulnweb.com -i basic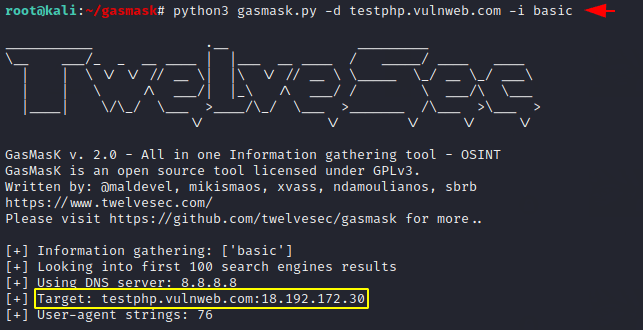
Emails
Boom 🙂 !! As you can see we have received email addresses on the target web application without much effort.
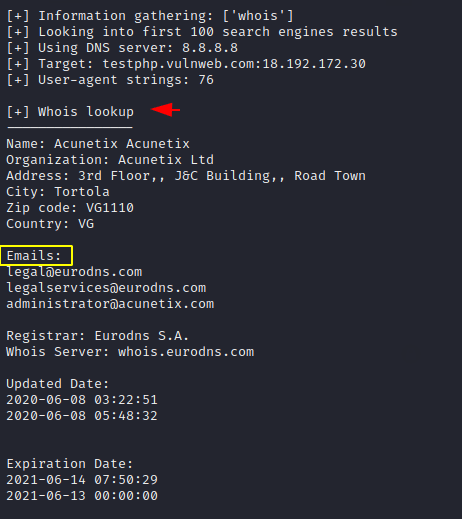
Whois Lookup
Similarly, we can also see when a web application has been registered and when will the domain expire.
python3 gasmask.py -d testphp.vulnweb.com -i whois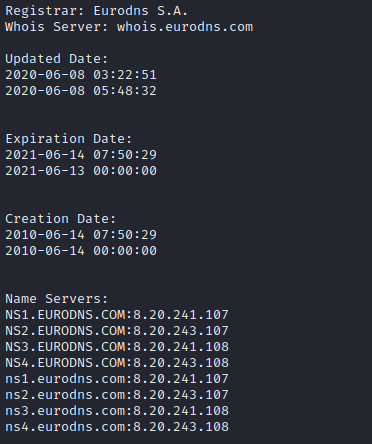
DNS Details
In some cases we need to find the DNS details of the target website for which we use various third-party tools or online service but through this tool we can easily find it.
python3 gasmask.py -d testphp.vulnweb.com -i dns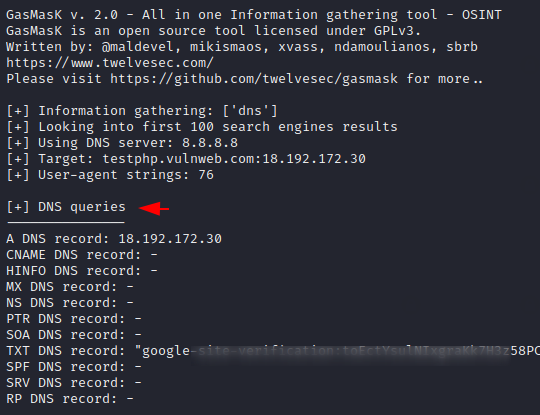
All in one option
Similarly, you can get all the above information at the same time by adding all the arguments by commas.
python3 gasmask.py -d testphp.vulnweb.com -i whois,dns,revdns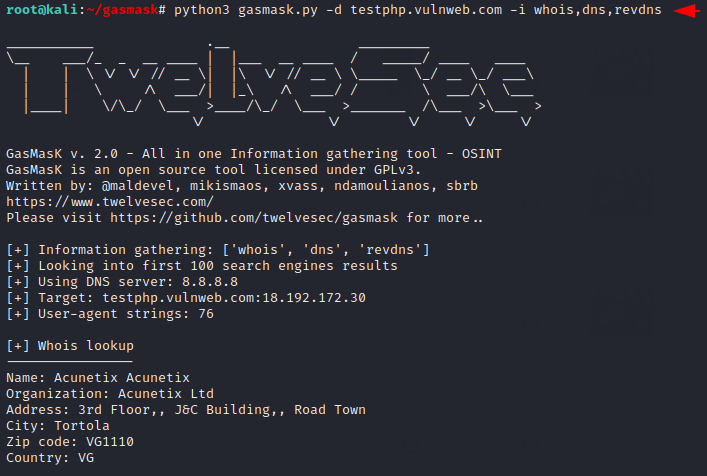
Done 🙂 !! Thus you can take help of this tool and get more information about the target easily.