Hey Folks, this article may be more helpful for bug bounty hunters who usually hunt for bugs in different web applications. In this tutorial we will tell you a tool that will help you bypass the forbidden directories called “DirDar“. You can read below what you can do with the help of the tool.
Let’s take a look 😛 !!
Golang Installation
This tool is compatible with all kind of operating systems but you should have GO compiler installed.
apt install golang -y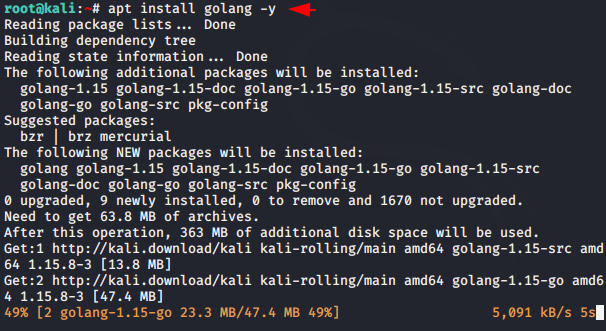
Once the Go compiler is installed and configured, execute the following commands.
go get -u github.com/m4dm0e/dirdar
Done 😛 !! Now you can use the following command to boot this tool.
dirdar -h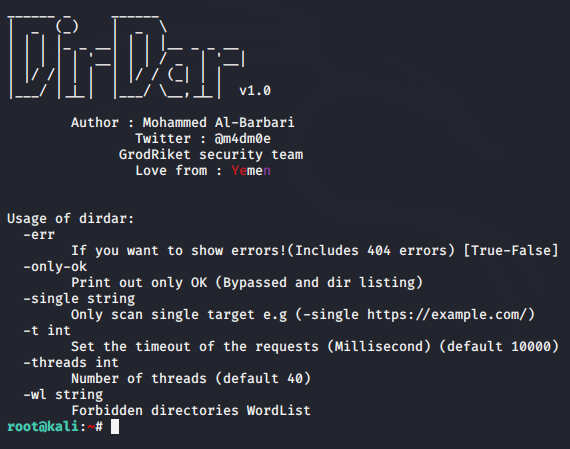
Bypassing Forbidden Directories
Bypassing 403 Forbidden Errors indicates that the client was able to communicate with the server, but the server won’t let the client access what was requested. Although the tool uses several combinations to resolve this error. Let us give you an example. As you can see we have found a location that the client is unable to access.
dirdar -single https://secnhack.in -wl word.txt
Even you can see that once we open the location, we get a 403 error which shows that the server does not want to give access.

Wait 😛 !! Once the 403 error code is found at any location by this tool, it will try to circumvent it by adding several payloads.
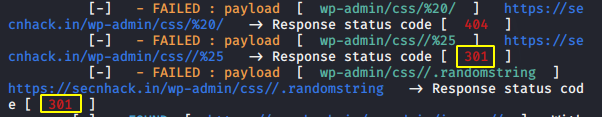
Good 😛 !! Once sidelined you will be able to access it.

Similarly, you can check the listed directory using the below command.
dirdar -single http://testphp.vulnweb.com
Likewise, you can use all the features of this tool one by one and take your bug hunting art to the moon : P !!






can your share your payload
Appreciate writing this. I love the online world because you can study something new every day. I’ll share this with my friends, thank you!
Highly descriptive blog, I loved that bit. Will there be a part 2?