
Hey Folks, In this tutorial we will talk about several ways through which we can send or receive emails to bypass verification and send documents anonymously to someone else. At times we require an anonymous email address for many reasons and we take the help of paid service, but in this article we will tell you about all the free online services from which we can send any document without paying anything. As an ethical hacker we can use all these services for social engineering.
Lets take a look 🙂 !!
Now first of all we will tell you about the services through which we can send email anonymously to someone else.
Fake-Mailer – CLI Tool
It is an open source github project specifically designed to send documents or messages to someone else via the command line. Lets configure it 🙂 !! Now first of all we will download it from github page via git command and after downloading is done, we will go to the directory of this tool and execute the “setup” file to setup this tool. After doing all the process then we can start this tool using python tool.
git clone https://github.com/htr-tech/fake-mailer
cd fake-mailer
bash setup
python2 mailer.py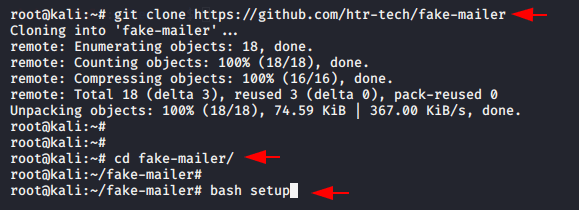
Finally it’s time to take a demo of this tool 🙂 ! It’s not difficult to understand the feature and we need to give us the email address and the content that we want to send messages anonymously.
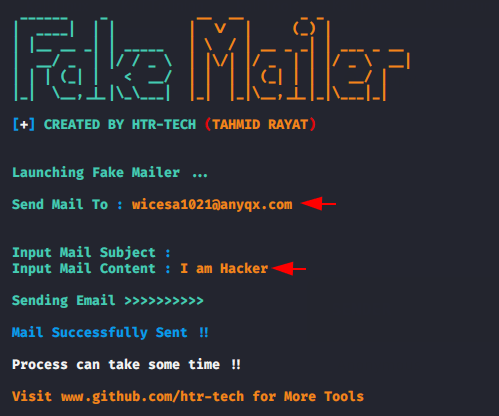
Get it 🙂 When we check email on online temporary services, we get the same message that we send through this tool. Just like that we can send email anonymously to anyone.
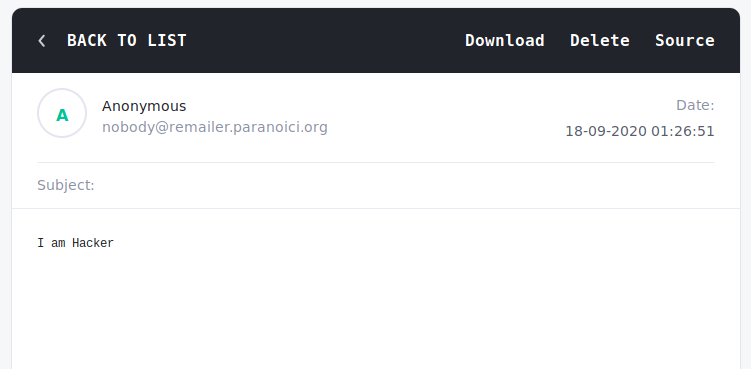
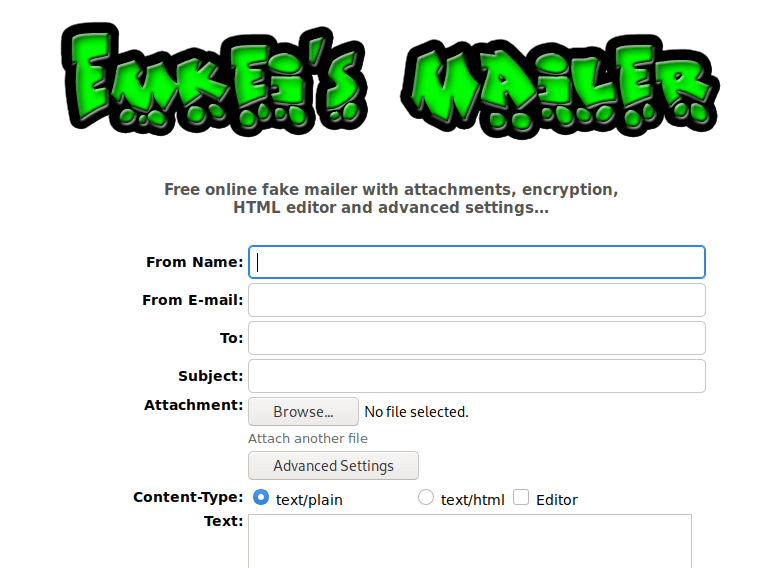
Emkei
It is an another email spoofing site, it sends the e-mails in the name of anyone you want, it sends it in “offline” mode, without a logged in sender. You can visit from here.
It provides us various features to customize the email address details. After filling the given requirements, we click on the advance option to see additional details.
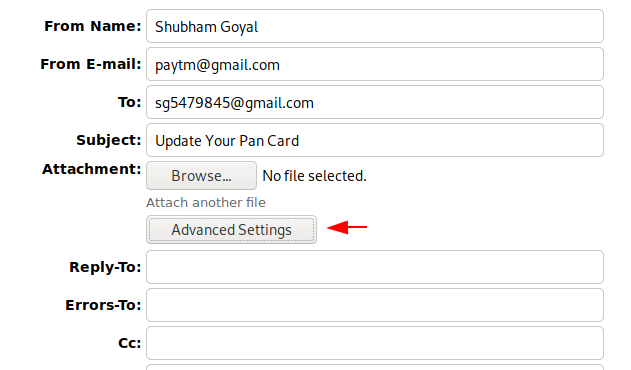
The SMTP server is the most important factor for sending and receiving email addresses, hence we have to give our smtp server and port number by going to advance settings to send the email address to the victim but you can use the same smtp server that we mentioned.
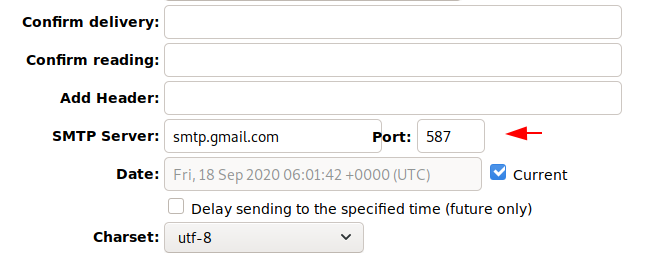
Several options are available for composing messages, but you can choose according to yourself.
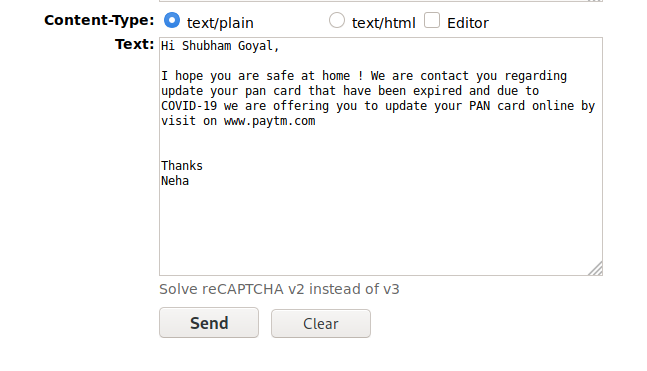
After click on sent button the email will be successfully sent to the victim.
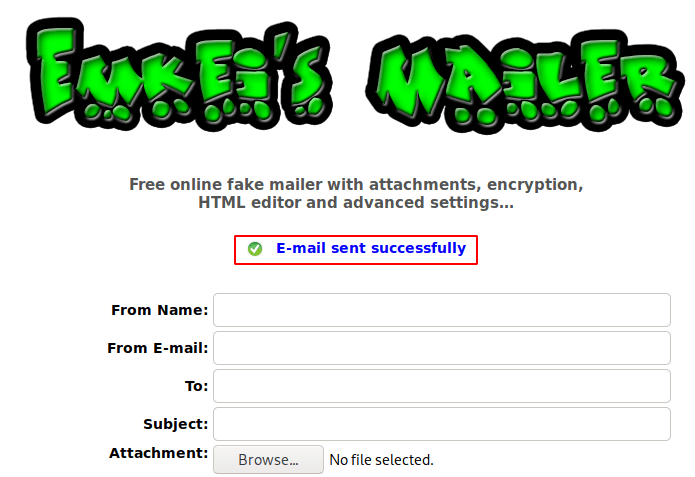
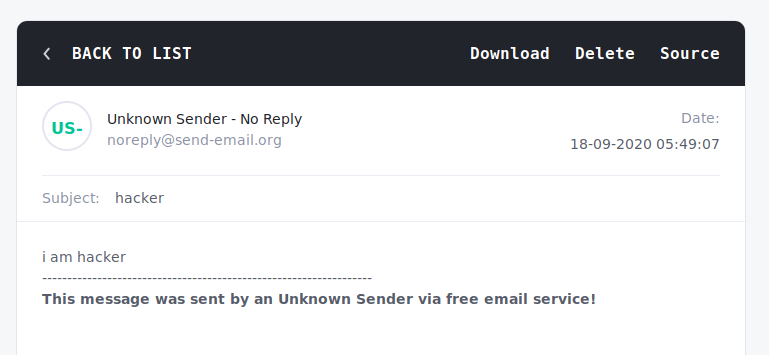
Ncie 🙂 !! Here you can see that the exact same message has been arrived that we had sent through the online service to themselves.
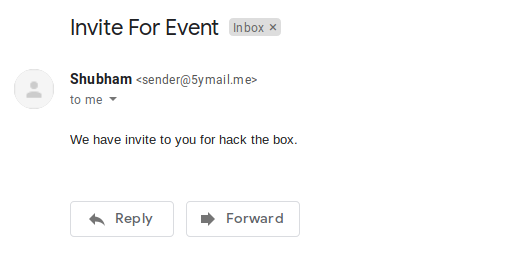
Anonymous Email – 5ymail
This will be our third method, through which we can email anyone anonymously. This is another online service that you can use from here and take advantage of it.
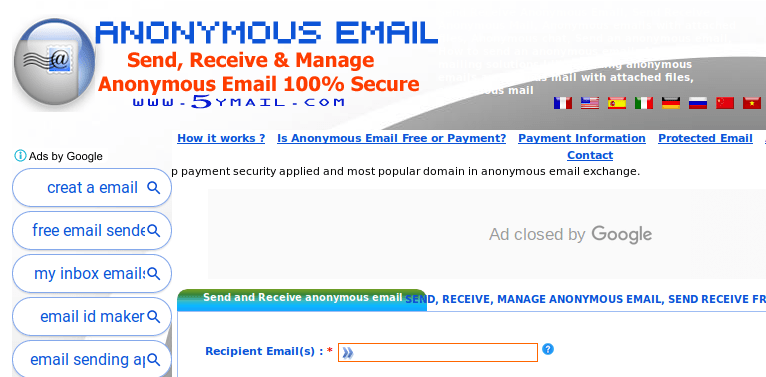
Like every time, this time we will also add the details and name that you want to send email anonymously.

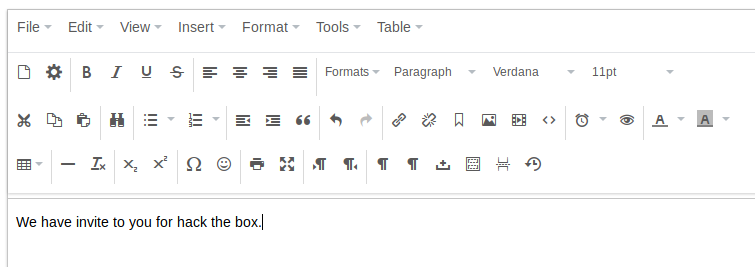
Write the message you want to send to the victim 🙂 !!
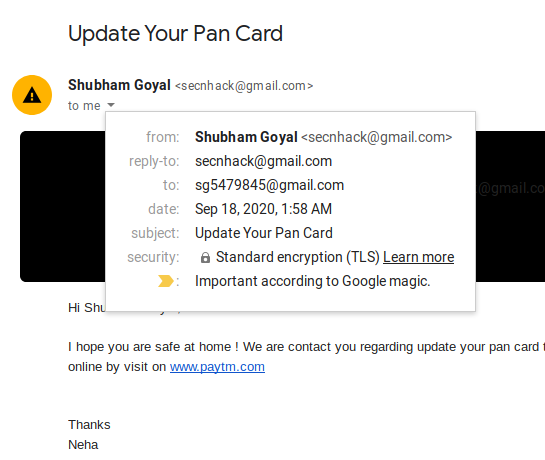
For confirmation, in the final it will show us all the details that we had filled ourselves and after the email has been successfully sent it will give us the credentials on our gmail address, through which we check the status of the email address.
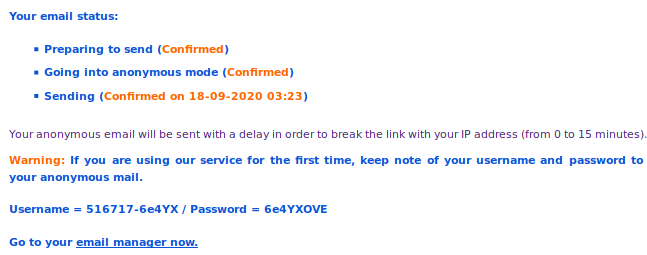
Done:) !! After returning to the gmail address we received the same message that we sent to ourselves through online services.
But sometimes we find temporary email services for the verification that called disposable email addresses. This kind of services also known as DEA or dark mail that allows to receive email at a temporary address.
Tmpmail – CLI
If you are familiar with CLI tools then we would recommend you to go with it. Configuration can be very difficult for you but it is one of the best temporary tools for generating or receiving email address.To configure each tool we have to install some requirements. Similarly, first we have to install some dependencies for this tool.
apt install jq w3m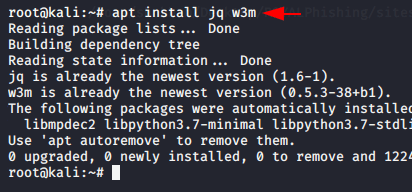
The Wget tool is used to download resources from the Internet and we are going to use this tool to download this service directly to our terminal. After downloading is done we will give the executable permission of the downloaded file.
wget https://raw.githubusercontent.com/sdushantha/tmpmail/master/tmpmail
chmod +x tmpmail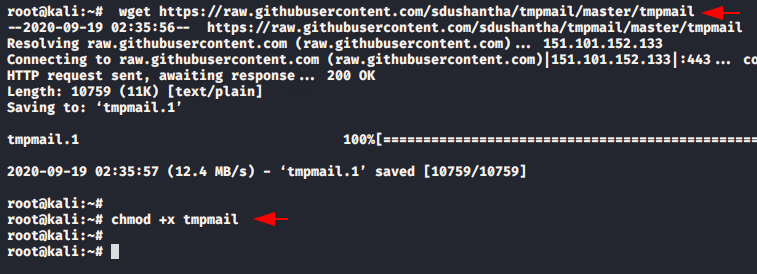
Done:) After doing the general configuration, our tool is ready to boot and through the below command we can identify the features of this tool.
bash tmpmail --help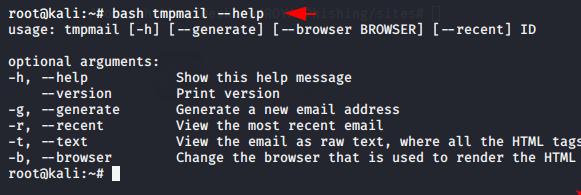
We don’t have to do anything, just execute the given command and it will automatically generate a temporary email address which we can use to bypass security and several reasons.
bash tmpmail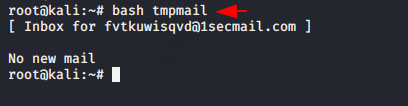
Great 🙂 !! As you can see that after sending the mail to the address given by this tool, we have successfully received the same mail on terminal after executing the below command.
bash tmpmail --recent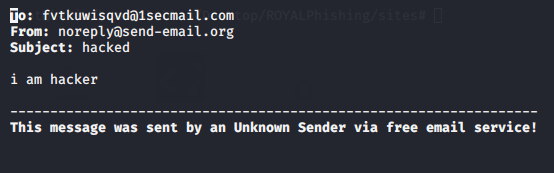
Note : You have to execute the above command to check recent mails.
TEMPMAIL
Similarly, you can take help of some online websites which provide us temporary services, through which we can get email or bypass verification. There has multiple services are available such as : tempmail, 10minutemail, throwaway email, fake-mail or trash-mail. You can visit here to use this tempmail service.
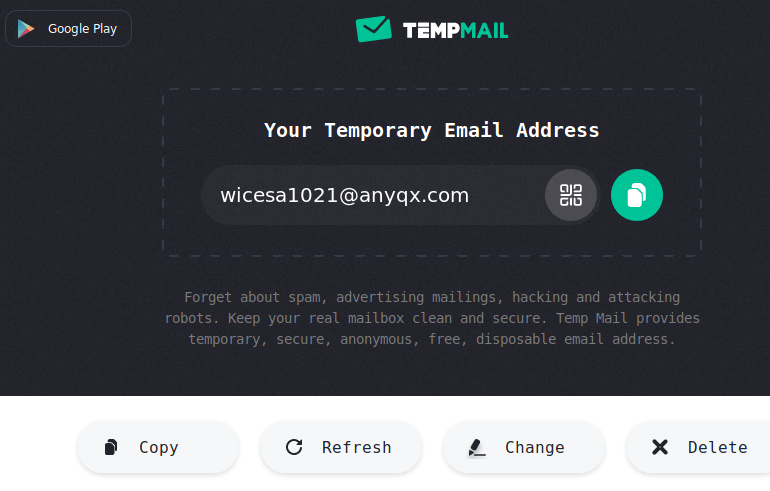
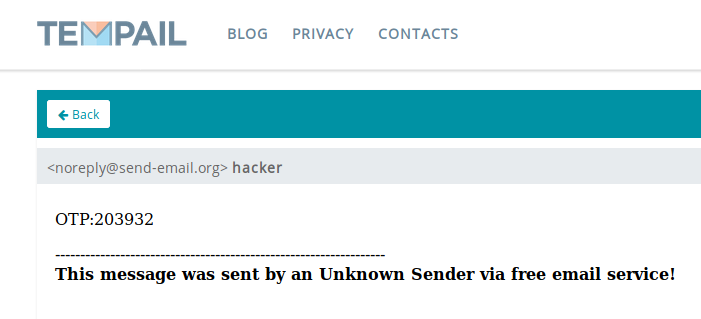
Hmm 🙂 !! Here you can see that we have got the attacker’s message.
TEMPAIL
We would recommend you to use both services to complete registration or verification.
https://tempail.com/en/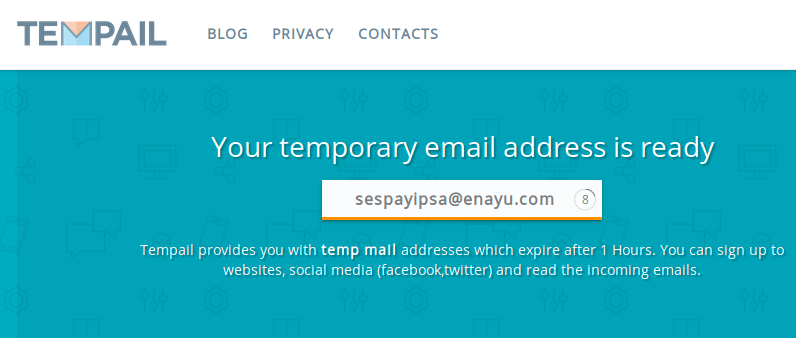
Done 🙂 !! Similarly, we can take help of many such online websites for creating accounts or completing any kind of verification.





What’s up to all, the contents existing at this web site are actually amazing for people experience, well, keep up the good work fellows.
Ahaa, its nice discussion about this post at this place at this
webpage, I have read all that, so at this time me
also commenting here.