
This is the first part of footprinting series, In this article we will discuss first 3 types of footprinting.
As we know that there is lot of cyber crimes taking place now a days and we call these persons as hacker. In such a situation, some people are saved and some fall prey to it. This happens because we are not familiar about it. Therefore, we will understand first step of this process with the help of this article i.e. Footprinting.
Whenever cybercirme is take place then we gain the information about him. Ex : suppose one people has fall prey of cybercime by spam email. Then after that he will collect information about him like – who was he, is on which social media platform , what is ip address, mac address etc. thats is called footprinting and footprinting also knows as information gathering.
Ways to do Footprinting
- through Search Engine
- through Social Engineering
- Competitive Intelligence
- through Social Networking Sites
- Whois Footprinting
- Website Footprinting
- through advanced google hacking techniques
- Email Footprinting
- Network Footprinting
- Dns Footprinting
Footprinting through Search Engine
To do footprinting through search engine is easy. Now a days, most of the people are active on social media plateform or have their own website and This cause some profiles to rank on search engines. So search engine is advantage for you to grab the information about them. There are many popular search engines where you can find anything :
- www.wolframalpha.com
- www.google.com
- www.shodan.io
- www.duckduckgo.com
- www.bing.com
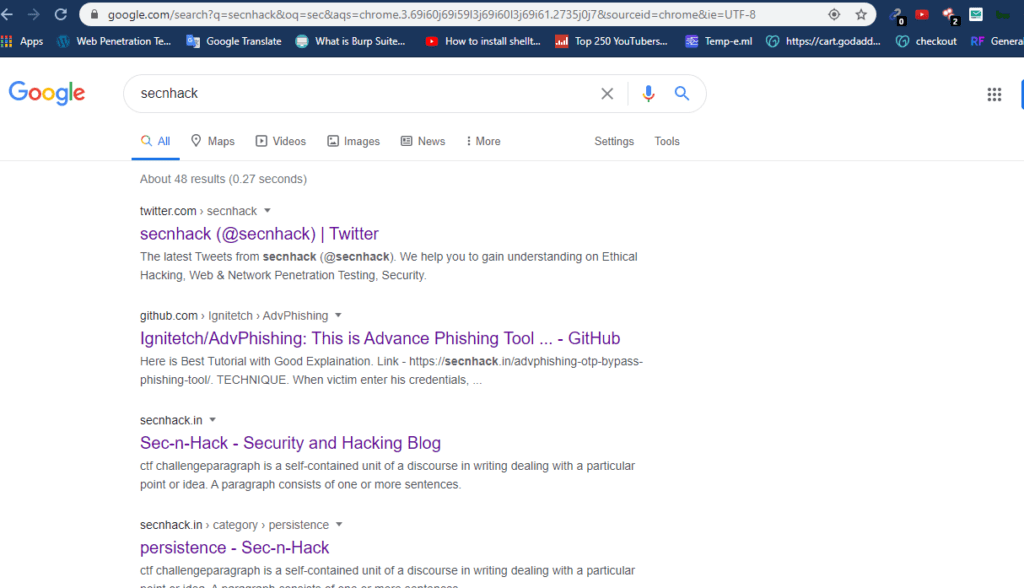
Now take the example of google.com. If I search “secnhack” on Google, then i have received all profiles of secnhack in which include social media profiles.
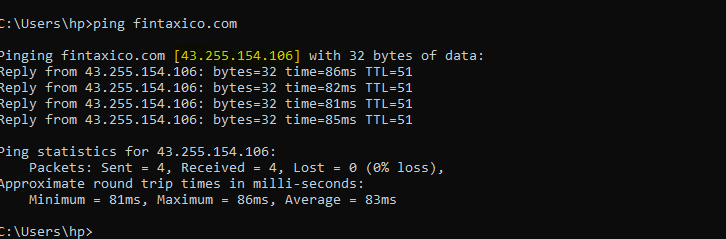
If we have webpage url or domain name of victim so we can find ip address and broadband service provide of vicitm. To know IP address of any website just ping the website as shown below :
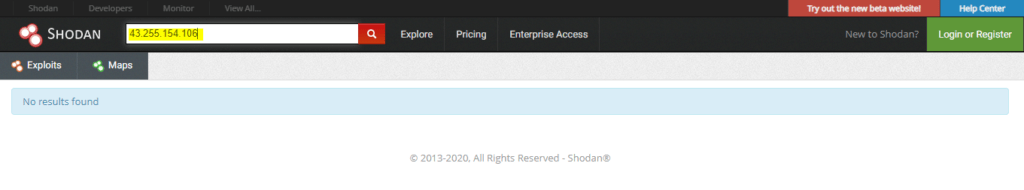
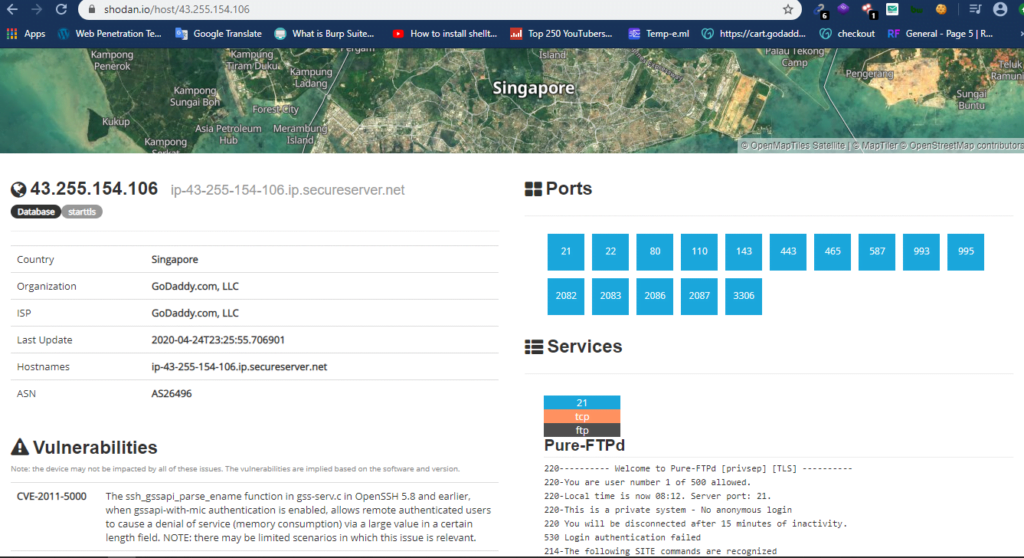
Shodan is the another search engine tool, it help to find :
- Ip address
- Ports
- Vulnerable IP’s
Open shodan.io in your browser and search this ip address.
You can see that shodan has successfully find domain details, vulnerability and much more information.
Just like that you can gather information in various search engine platfomes.
Footprinting through Social Engineering
social engineering is an art in which we can gather exact information of victim.
About Social Engineering
social engineering is one of basic attack in which we can execute our plan with minimum efforts. social engineering as one of the simplest methods to gather information about a target through the process of exploiting human weakness that is inherit to every organization. with the help of social engineering you can collect sensitive information.
Lets take a new example
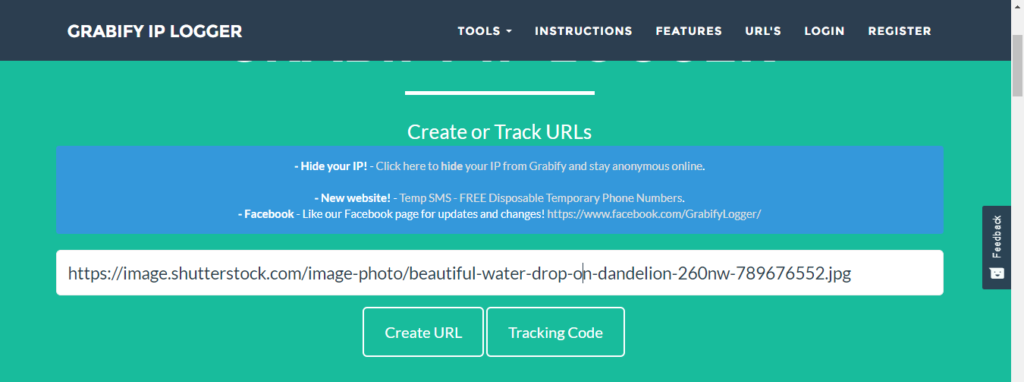
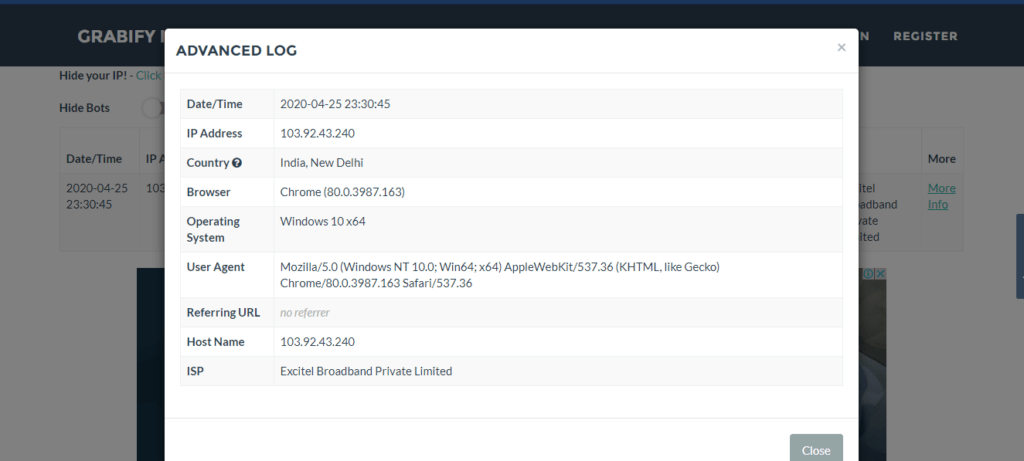
Ex : i want to check what device is he using. what we do should
Step-1 Create a fake number using these application on mobile and you can find tutorial on youtube aslo.
- Textnow
- 2ndLine
Step-2 After that go your chrome browser and copy any image url.
Step-3 After paste this url click on create url button and wait for result
Step-4 You will see two links from which to send the new link to Victim by fake number through whatsapp as you wish.
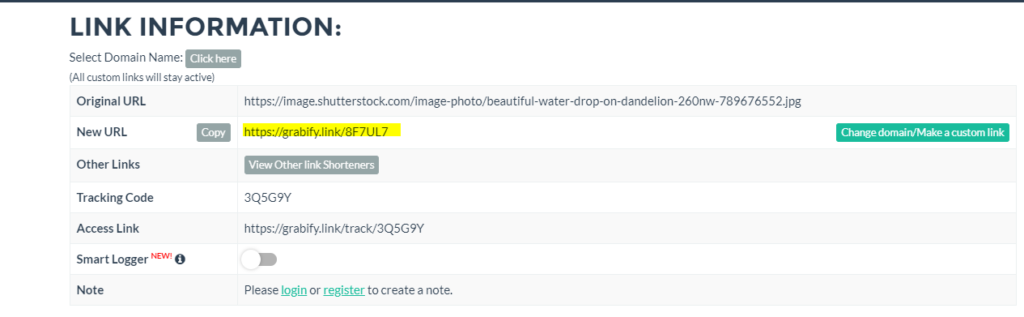
Good Job ! You can see that after clicking this link by victim we have all details about of his.
Footprinting through Jobs Sites
Similarly, if you want to gahter information about the company’s, employees, hardware information, software information, salary, his profile, so you can try these sites :
- www.indeed.com
- www.dice.com
- www.usajobs.gov
- www.dice.com
- www.monster.com
- www.linkedin.com
- https://my.naukri.com
- www.ziprecruiter.com



Like!! I blog frequently and I really thank you for your content. The article has truly peaked my interest.
thanks
Nice weblog right here! Additionally your
website a lot up very fast! What host are you using? Can I am getting your associate
hyperlink in your host? I wish my site loaded up as quickly as yours lol
I seriously love your website.. Great colors & theme. Did you create this website yourself? Please reply back as I’m looking to create my own personal website and want to know where you got this from or exactly what the theme is named. Kudos!