Hey Folks, in this tutorial we have an interesting tool for beginners whose named “sifter“. Sifter is a osint, recon & vulnerability scanner. It combines a plethara of tools within different module sets in order to quickly perform recon tasks, check network firewalling, enumerate remote and local hosts, and scan for the ‘blue’ vulnerabilities within microsft and if unpatched, exploit them. It uses tools like black widow and konan for webdir enumeration and attack surface mapping rapidly using ASM.
Let’s take a look 🙂 !!
Installation
It is possible that it does not work on any other operating system instead of kali linux, but you can try it once. We will simply download this project from github and go to the directory of this tool and execute the bash command to successfully configure it.
git clone https://github.com/s1l3nt78/sifter.git
cd sifter
bash install.sh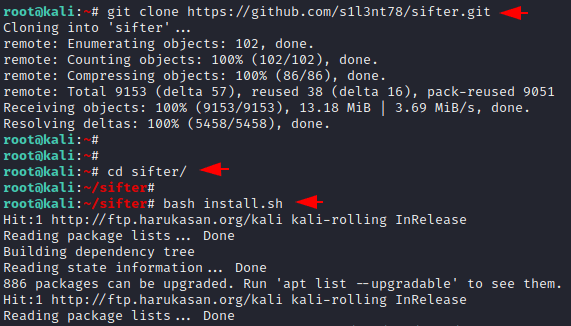
Done 🙂 !! Once the installation is done we can boot this tool using the following command.
bash sifter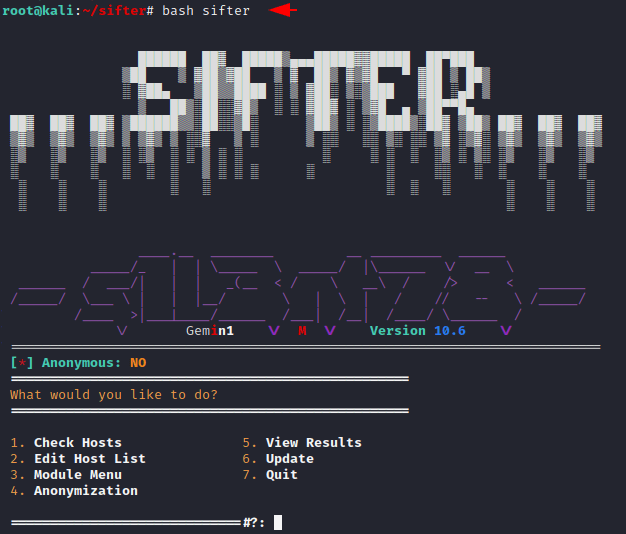
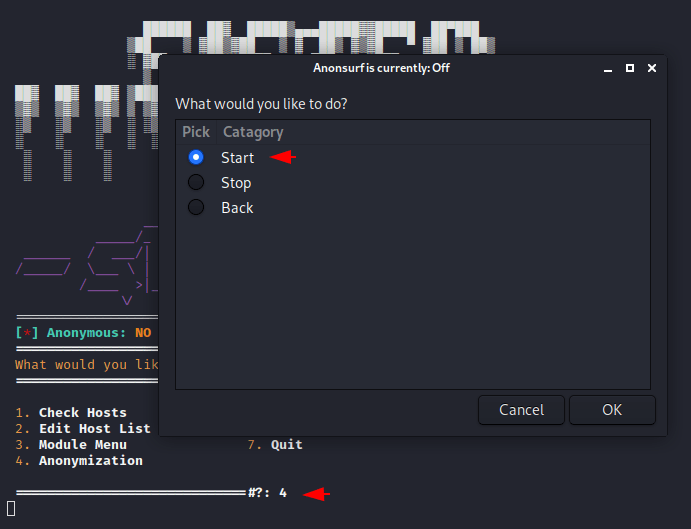
Enable Anonymity
As you have seen, the fourth option is given to anonymize yourself. After selecting the option a prompt pops up with the option to enable and disable anonymity.
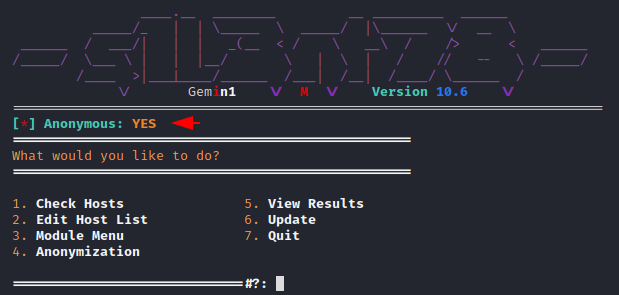
As you can see the anonymous features are fully enabled after clicking on the start.
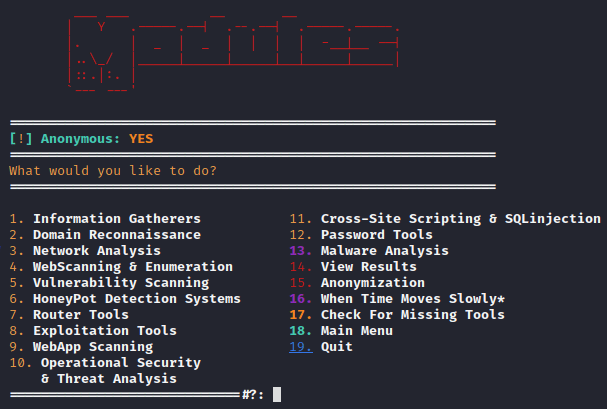
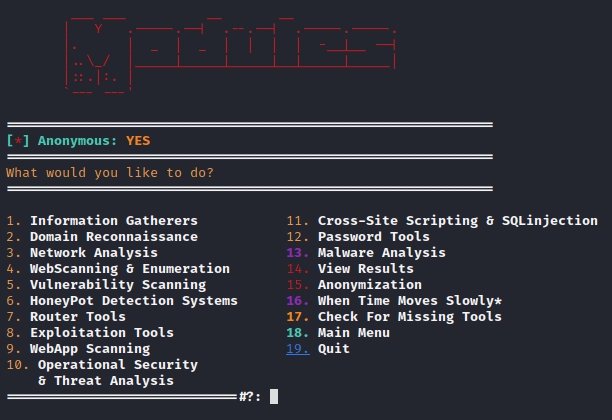
Modules
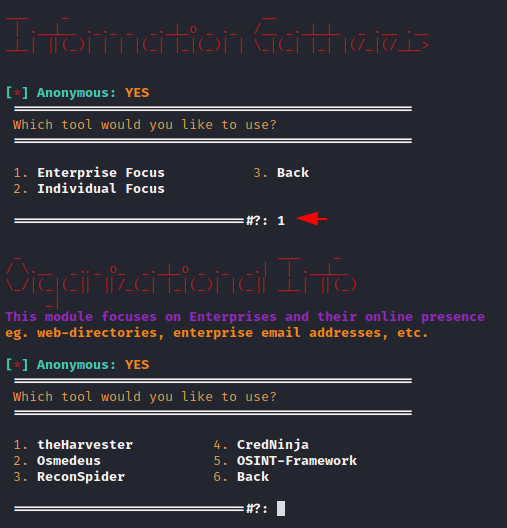
We can see all the available module by choose the option “3″. As you can see there are different types of categories available to collect information about the target. Now we will select option first to see all available tools in information gathering option.
As you can see it gives us two more options “Enterprise or Individual” and out of both we choose the first option. But due to more tools we cannot show all the features at the same time, that is why we will show only the main features.
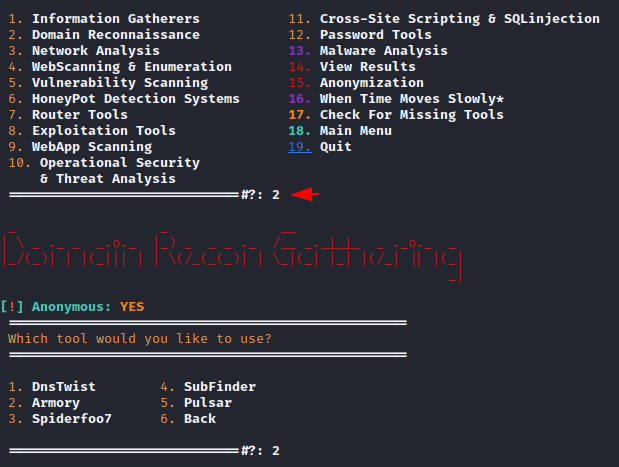
Domain Reconnaissance
It’s some pieces of information that can be discovered include DNS servers, IP addresses, mail servers, SPF information, open ports, and more. You can see
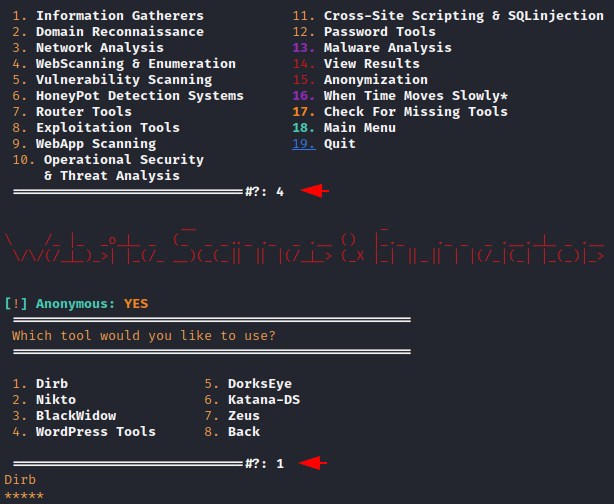
WebsScanning and Enumeration
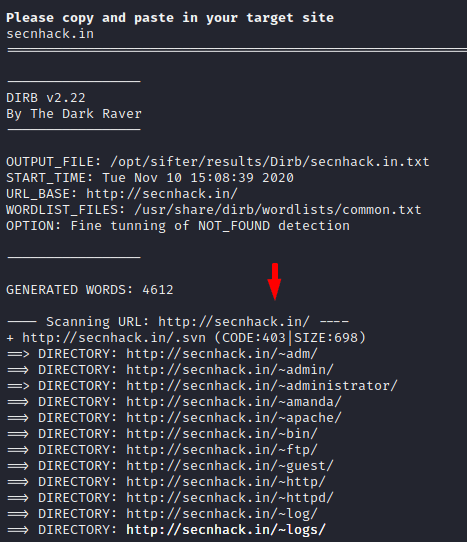
As you can see the top leading tools are given to find hidden directory or crawling objectives.
Nice 🙂 !! It has successfully dumped all the sensitive directories available in the web application.
Similarly, you can use all the features one by one and collect useful information related to the target.