
Hey Folks, this tutorial will be for beginners who want to hunt for bugs in web application but don’t have much skill yet. Actually before you don’t have good knowledge of bug hunting, you cannot opt for manual method so you have to take help of such automated tools which help you to detect bugs automatically. So let us discuss an automated bug hunter tool.
Let’s start 🙂 !!
Pre-Installed
Skipfish is an active web application security reconnaissance tool that comes pre-installed in kali linux operating system. t prepares an interactive sitemap for the targeted site by carrying out a recursive crawl and dictionary-based probes. e resulting map is then annotated with the output from a number of active (but hopefully
non-disruptive) security checks. The final report generated by the tool is meant to serve as a foundation for professional web application security assessments. You can activate this tool by execute the command below.
skipfish -h
Let’s Pentest
All you need to do is provide the location of the “output” and the URL of that website on whichever website you want to hunt for the bug. Once the command is executed it will show some details of the attack which we can skip by pressing enter.
skipfish -o test http://testphp.vulnweb.com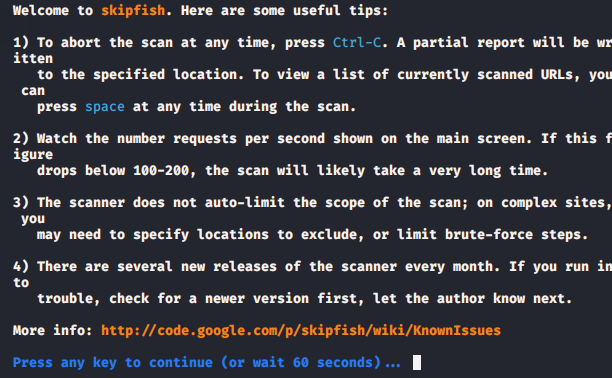
Details
Now here we can see all the details about the ongoing attack such as scan time, HTTP requests, reqs pending, issues etc.

Done 😛 !! Once the scan is complete it will automatically create a file named “index.html” inside the output folder which we can open on the browser and analyze the results.
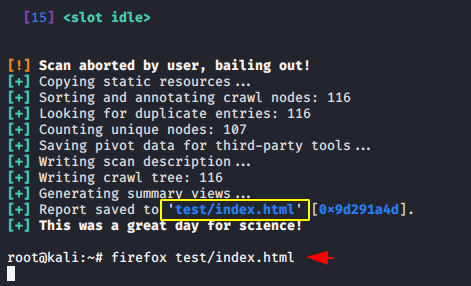
Hmm 🙂 !! The result will appear as the image shown below where we can check the details in deep by expanding the document.

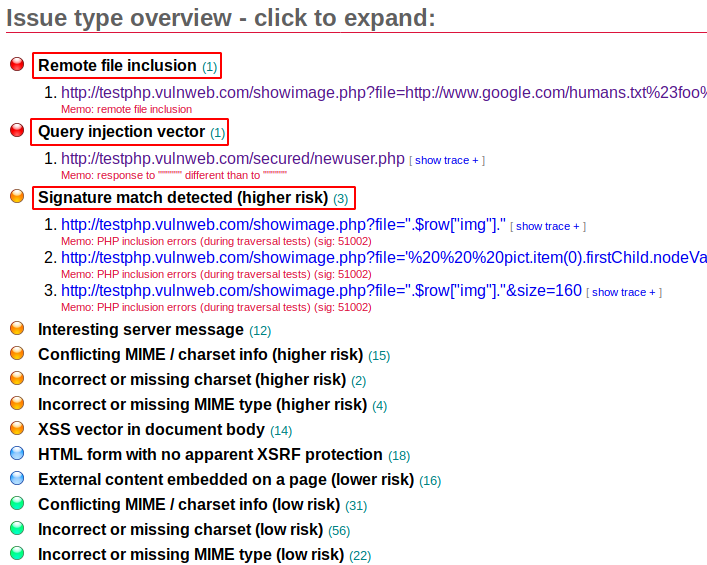
Categorize
As you can see it categorizes all the vulnerabilities according to the impact with the colors. As we know how important the “Remote Code Execution” vulnerability is and according to it it has classified this vulnerability at the top. Looks perfect 🙂 !!

Expand Documents
It shows vulnerabilities with payload so that we can directly exploit.
XSS
You can easily identify cross site scripting vulnerabilities in web applications even without finding any endpoints.

Triggered 😛 !! You can see a complete proof of concept such that whatever payload it gives us actually works perfectly.

Good 🙂 !! This was just a small demo of this tool as there are many more features in this tool but we have already covered the main features of this tool so that you will get an idea and after that you can operate it yourself. Enjoy !!





