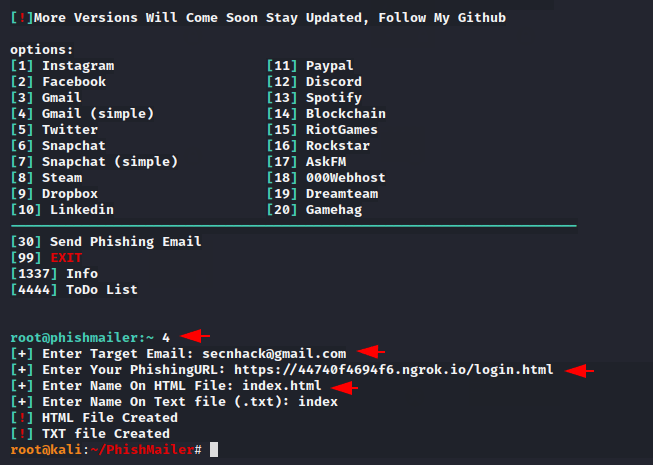
Hey folks, in this tutorial we are going to talk about a different type of phishing tool that can get some better results by coordinating with social engineering. This is an open source tool that is coded in python language named “PhishMailer“. Usually we get some error on multiple attempts of login or forgotten password and it creates the same alert phishing page to get some useful information which can lead to a phishing attack by placing malicious phishing URL on that phishing page. How it’s possible let’s see.
Let’s take a look 🙂 !!
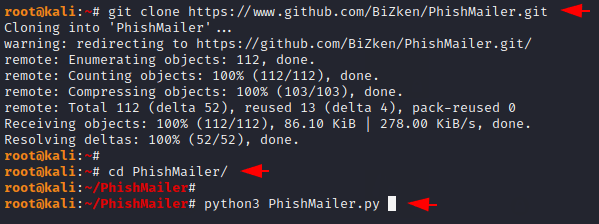
Installation
The installation of this tool is quite simple as we should have only one python tool and we can easily use this tool. Now we will donlwoad this tool from github then go to the directory and directly execute this tool.
1 2 3 | git clone https://www.github.com/BiZken/PhishMailer.git cd PhishMailer/ python3 PhishMailer.py |
Hmm 🙂 !! As you can see how many options you get in this tool.
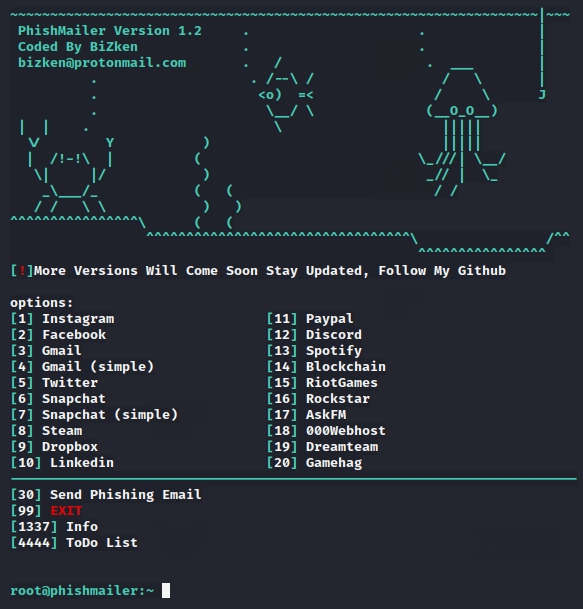
We will select option 5 for demonstration purposes. Make sure you have a victim account email address and a phishing link similar to a phishing page, meaning that if you have selected a google alert phishing template then you will have to create a google phishing page. Once the phishing template is created you can host it on your localhost server or online server.
Note : We have used advphishing tool to create google phishing page.
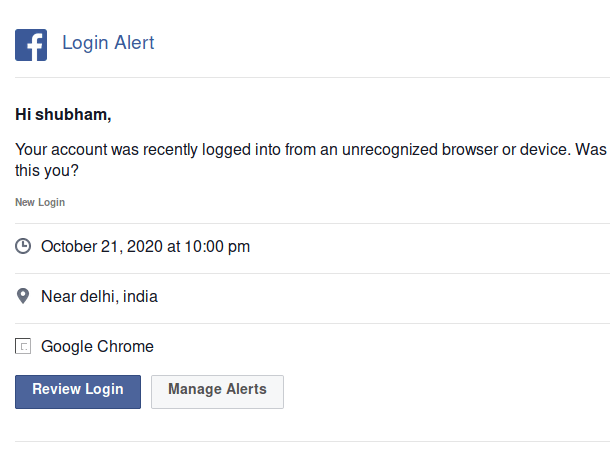
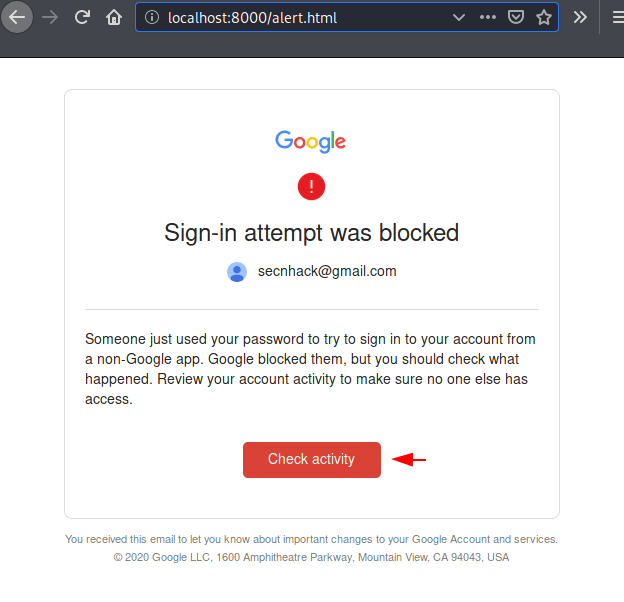
Great 🙂 !! As you can see what the alert phishing template will look like after opening by the victim. As you know we inserted the phishing link while creating the alert phishing template, so when the victim clicks the activity button they will redirect to our phishing page.
Good 🙂 !! As you can see the victim has successfully redirected to our phishing page.
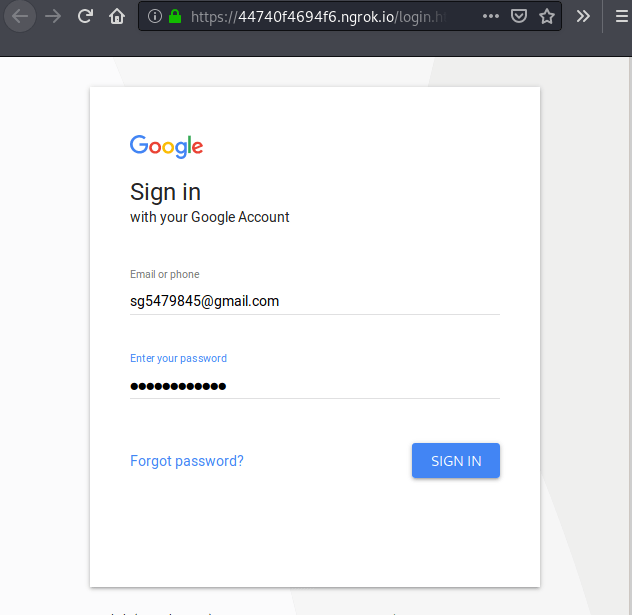
Boom 🙂 !! The victim immediately enter his credentials on phishing page after seeing several login alerts to secure his account. But unfortunately they again fall into the attacker’s trap.
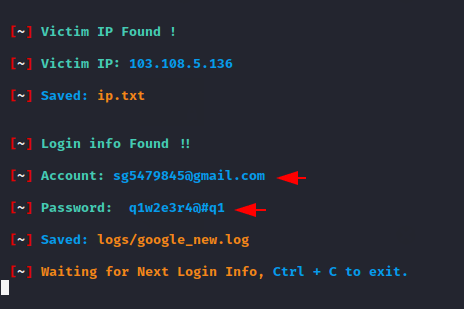
Done 🙂 !! Likewise, you can create a variety of phishing pages and take your social engineering skills to an advance level.