Hey Folks, in this tutorial we are going to add another web application security scanner tool to our bug bounty tools list called “Sitadel”. Sitadel is basically an update for WAScan making it compatible for python >= 3.4 It allows more flexibility for you to write new modules and implement new features .
Features
- Content Delivery Network detection
- Define Risk Level to allow for scans
- Plugin system
- Docker image available to build and run
Excited so let’s get started 😛 !!
Installation of Sitadel
So this time we are going to follow the easiest way to install this tool. See 🙂 !! Git utility comes pre-installed in every debian system so we can download any tool using “git clone” command. After downloading the project from github we have to install another utility in our system called “pip“. Now until the utility is downloaded, we can give our mind some rest 😛 !!
git clone https://github.com/shenril/Sitadel.git
cd Sitadel
apt install pip
pip install .
pip3 install .
Great 😛 !! That’s all and now we can operate this tool very snugly even without any issues. Let us start to explore the goodies of this tool by using its features one by one.
python sitadel.py --help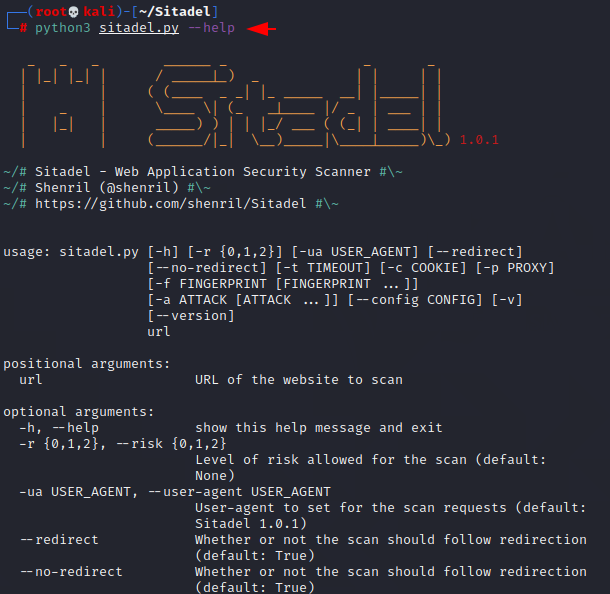
Missing Security Headers
In simple words only you need to enter the name of the domain which you want to get the information and it will show you all the details on the terminal. As you can see for example in the image below that when we provide a domain and it first gives us that number of security headers which are not available on the web application.
python3 sitadel.py https://secnhack.in
CMS and WAF Detection
We try many different tools just to see these things but this has dumped both useful stuff in just a second.

Increase Risk Level
Basically the risk level feature given by this tool is only being used for detecting the more useful stuff from the web application.
python3 sitadel.py https://secnhack.in --risk 2
Custom User Agent
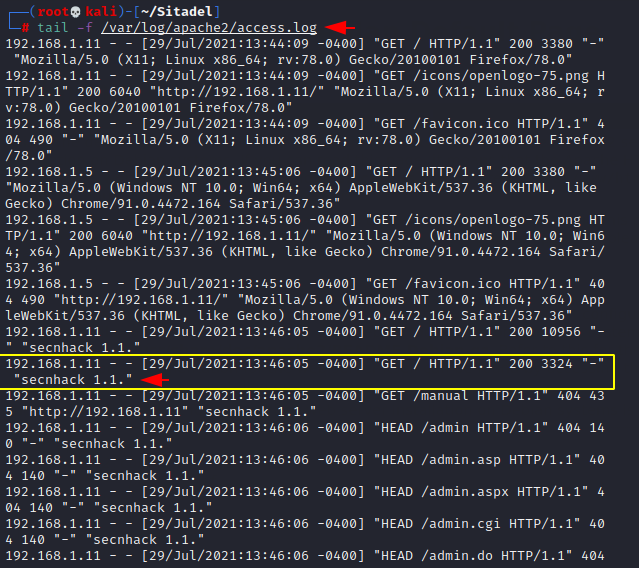
This is very useful for every penetration tester to make themselves completely secure and these same features come together to hide their true identity. As you can see we have entered fake user agent details so that each request is recorded on the victim web server log as “secnhack .1.1“.
python3 sitadel.py http://192.168.1.11 -ua "secnhack 1.1."
BOOOOM 😛 !! We did it and as you can see each log is coming with the same user agent we set up on the attacking terminal.