Hey Folks, in this tutorial we are going to talk about an reconnaissance and information gathering tool called “Raccoon“. Raccoon tool made for reconnaissance and information gathering with an emphasis on simplicity. It will do everything from fetching DNS records, retrieving WHOIS information, obtaining TLS data, detecting WAF presence and up to threaded dir busting and subdomain enumeration. Every scan outputs to a corresponding file. For more info visit here.
Lets take a look 😛 !!
Installing Dependencies
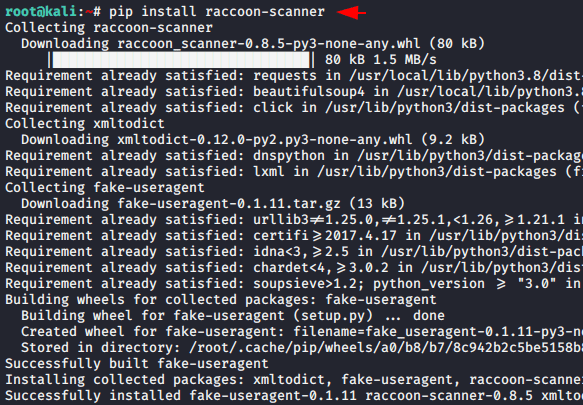
The tool requires Python3.5+ as well as pip tool which you can install by the using the “apt install python python3 python-pip python3-pip” command. After installing all the required dependencies we can easily install it without any error using the following command.
1 | pip install raccoon-scanner |
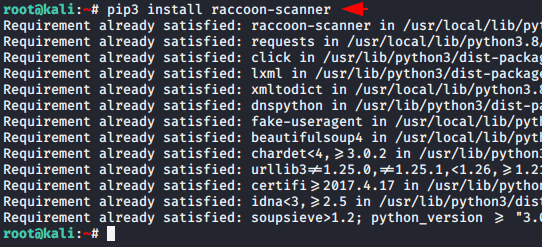
Also we have to install it with “pip3” tool, for which you can use the following command.
1 | pip3 install raccoon-scanner |
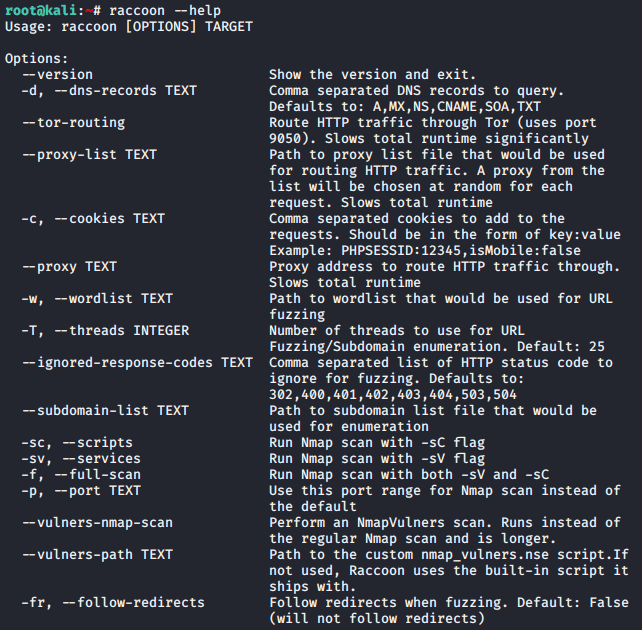
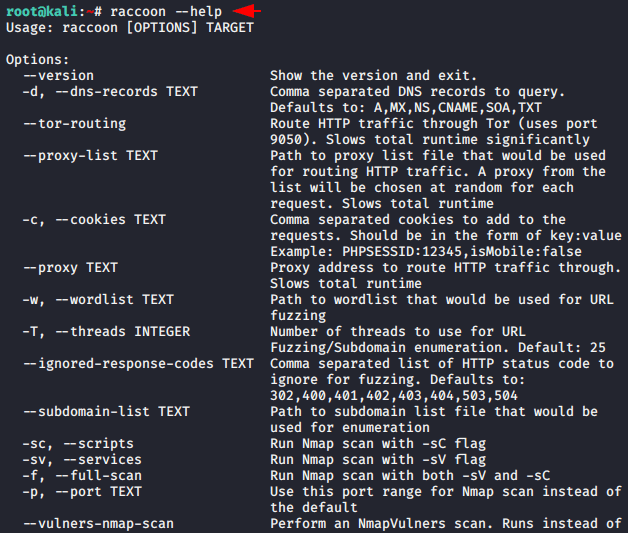
Done 🙂 !! Finally the tool has been fully configured in our system after which we can see all the available features in this tool using the help command.
1 | raccoon --help |
Example
Just take a web application on which you want to perform reconnaissance and place the web application URL in the given command as we have done below.
Usage 🙂 !! raccoon < target >
1 | raccoon http://testphp.vulnweb.com |
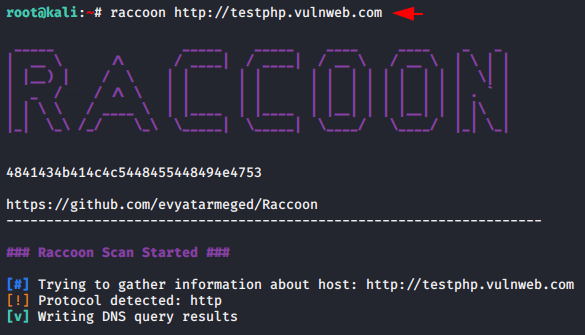
Sever Details
If the web application is hosted on a server with a vulnerable version then we can easily identify and exploit the vulnerability.
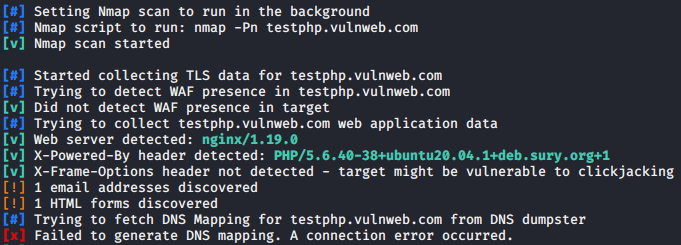
Ports
It is very easy to detect all available, open, closed, filtered ports running on a web application server.
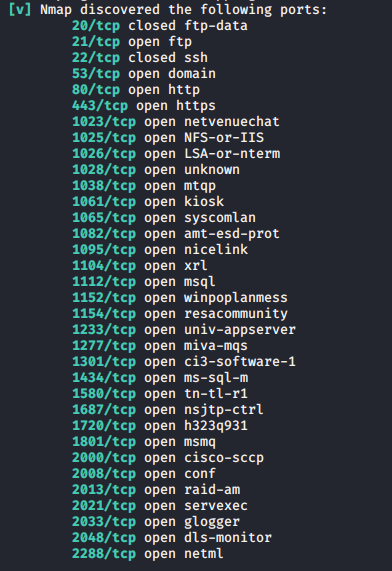
Crawling
Also it automatically crawls all the sensitive files or location from the web application.
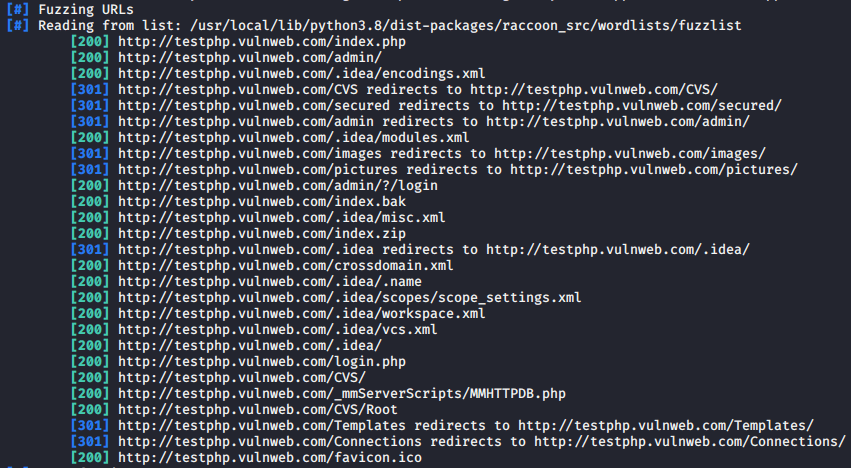
Results
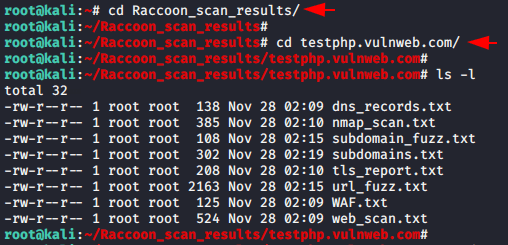
After the scanning of the web application is completed, then all the results in the folder of this tool will be saved automatically.
Done 😛 !! As you know we cannot show all the features of a particular tool at the same time so you can try all the features yourself and get more information about the targeted web application.
1 | raccoon --help |