
Hey folks, if you are a CTF player or bug bounty hunter, then this article can be useful for you, because in this tutorial we will present you a tool, with the help of which we can find the latest exploits with the command line. As we know that most of the time we try to find exploits on Google, which takes time, but it will make our work easier and we can also find direct links to the exploits.
Lets do it 🙂 !!
Installation
Like every time, this time also we will download this tool from the github page by using the git command.
git clone https://github.com/1N3/Findsploit.gitNow we will going into the directory by cd command.
cd FindsploitTo start this, we will give some permission.
chmod +x *Tool is ready for installation we need execute the given command.
./install.sh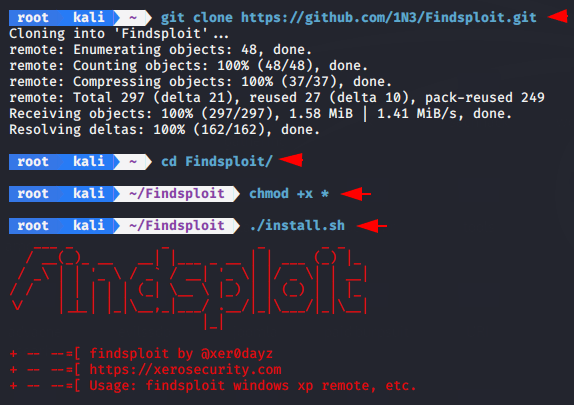
After doing all this we can start this tool by executing “findploit” on the terminal.
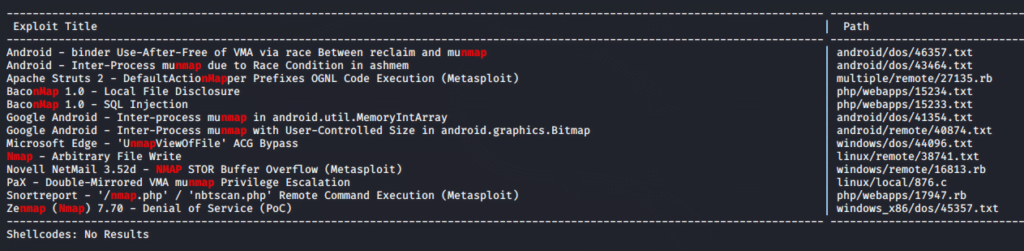
NMAP Scripts
In our first attempt we will try to find all nmap scripts by using the following command.
findsploit nmap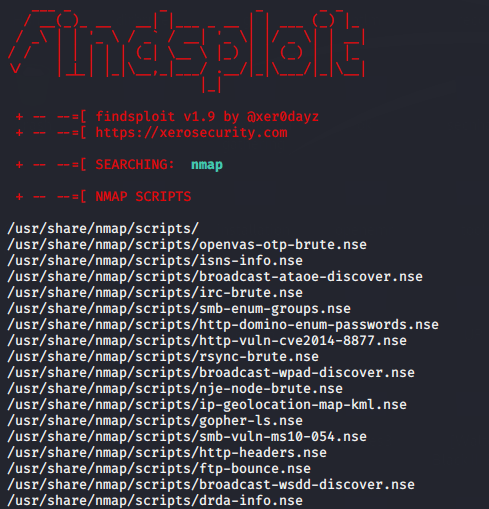
Its also provide the nmap exploits 🙂
Metasploit Auxiliary Modules
As we know that auxiliary modules is used to get information about victim. Now we will examine how many auxiliary modules are in Metasploit.
findsploit auxiliary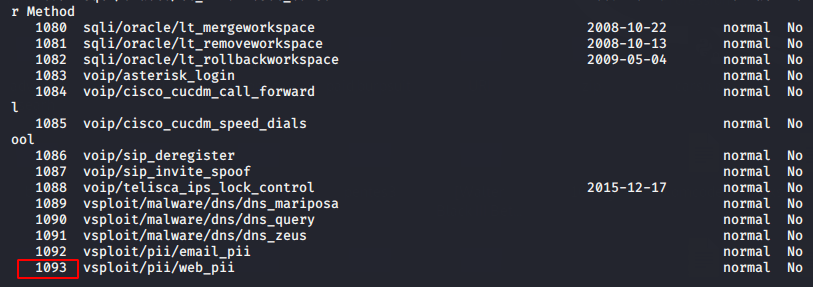
Payloads
This tool can also be useful to find the total number of payloads. Although we can find almost all metaspaloit modules with the help of this tool.
findsploit payloads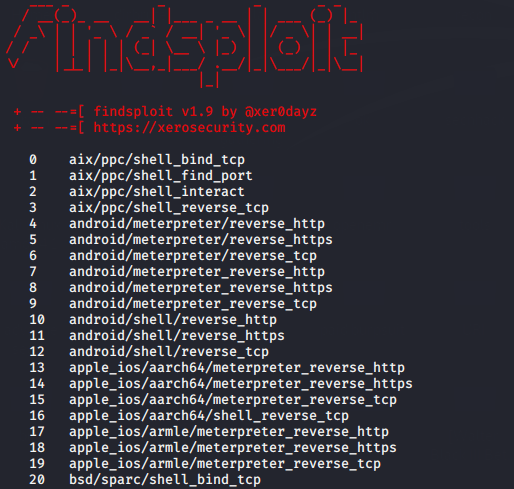
Filters
To get the best results we can add filters like the one below.
findsploit payloads | grep windows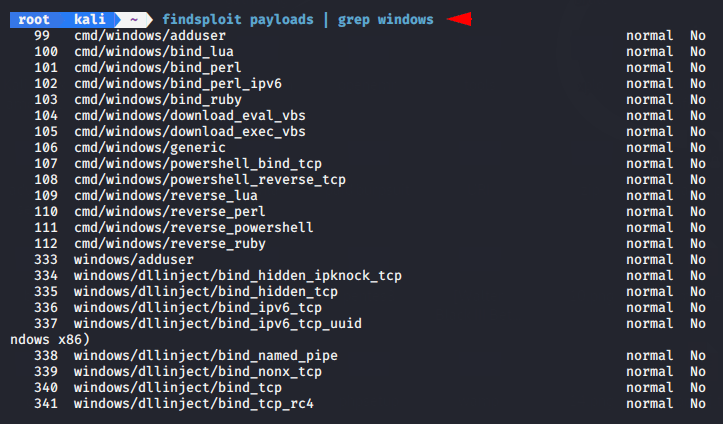
Exploits
In this effort, we will look for exploits with names.
findsploit Multi Scheduler 1.0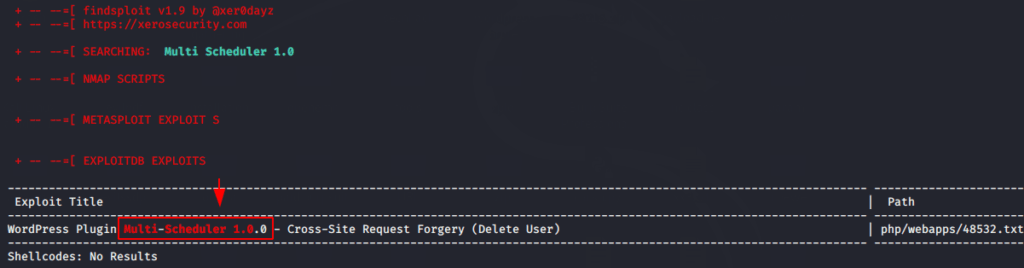
Lets take a another example and try to find some cms exploits.
findsploit gila cms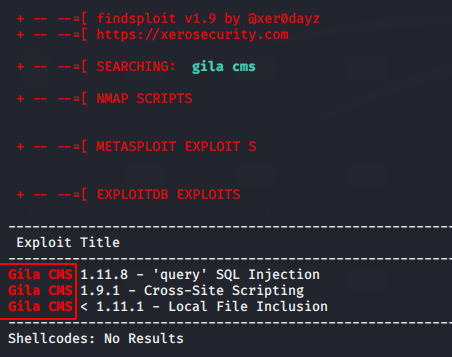
In fact it can be a helpful tool for a CTF player after seeing shocking results 🙂 !!




