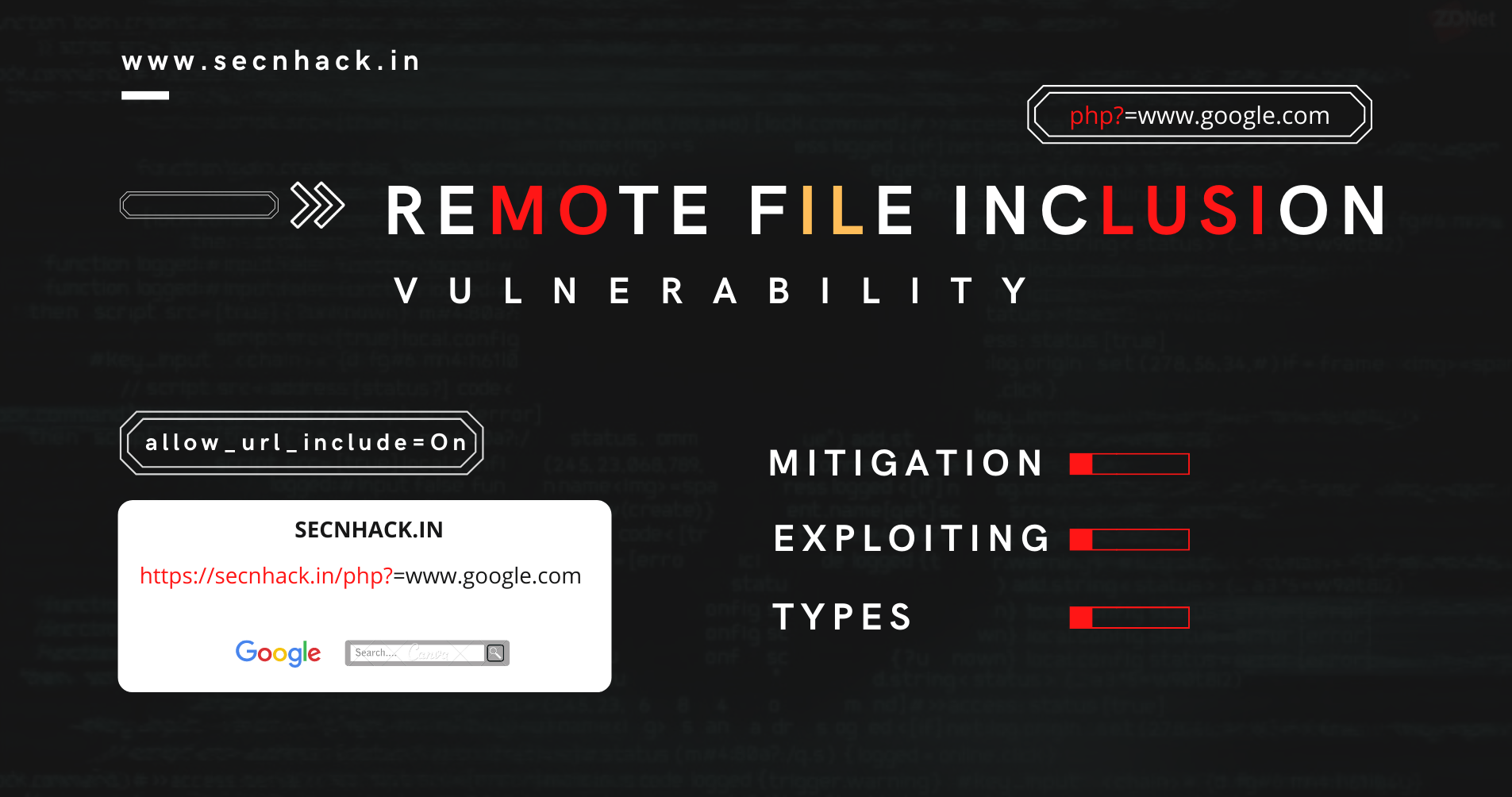
Remote File Inclusion (RFI) Vulnerability
Hey Folks, In this tutorial we are present here to move towards next vulnerability called “RFI ( Remote File Inclusion )”. We have already discussed about the “Local File Inclusion and Directory Traversal Vulnerability and we think you should go to our previous article to understand it better. RFI falls […]
Continue Reading