Hey Folks, in this tutorial we are going to talk about an open source vulnerability scanner tool called “Striker“. Striker is an aggressive information and vulnerability scanner, specifically designed to grab some sensitive information about the domain name and at the same time we can get a description of vulnerable services running on the target web server.
Let’s take a look 🙂 !!
Installation
The time has come to configure this tool where we will first download this entire tool using git command and after that we will go into the directory and execute the “pip” command to establish the required dependencies.
|
1 2 3 4 |
git clone https://github.com/s0md3v/Striker cd Striker/ pip install -r requirements.txt pip3 install -r requirements.txt |
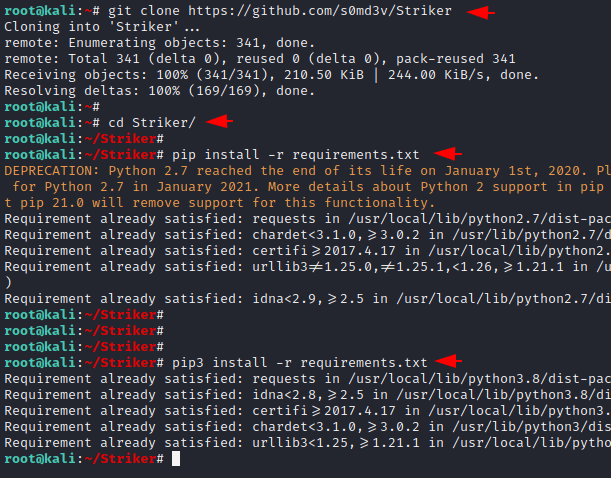
Done 🙂 !! The device has been successfully configured but we need another tool called “python” to use this tool. You can install it yourself by using the “apt install python3” command.
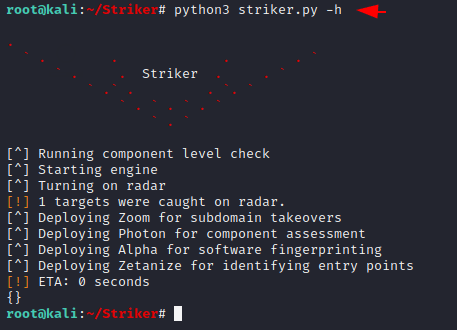
Example
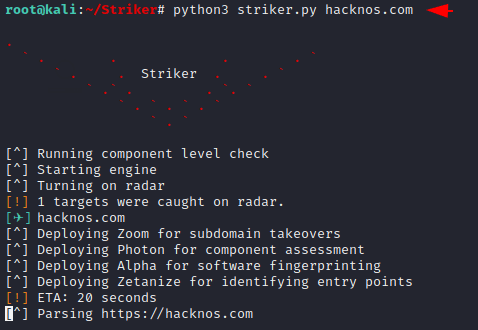
This tool is very easy to use because we can start collecting information by supplying only the domain name. You need to provide the domain name with no (https / http) and it will extract all the details automatically.
|
1 |
python3 striker.py < host name | domain > |
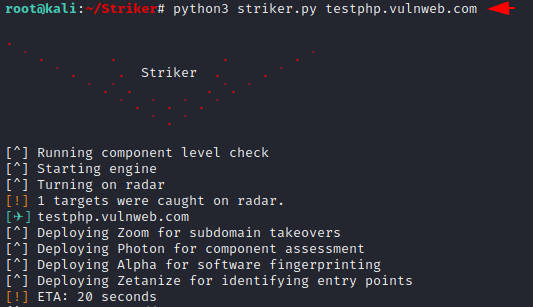
Results
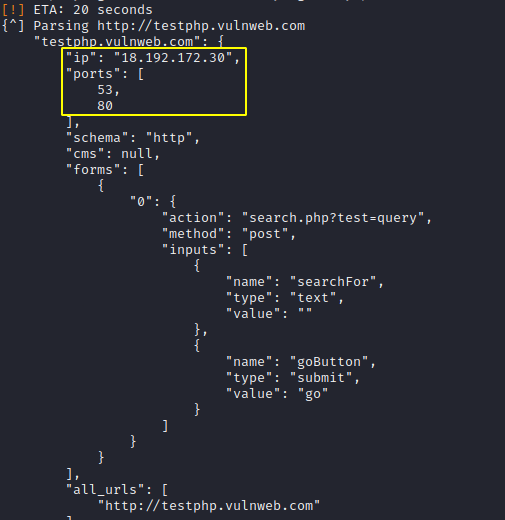
As you can see we came to know about the active services on the target web server.
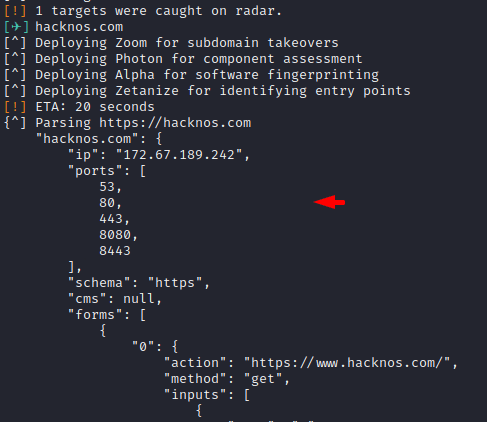
Let us take another example and in this effort we will give this tool a description of different domains.
Great 🙂 !! We get more information about the domain name such as public IP address, open ports, hidden files etc but we are not able to show you because of some security reasons.

A keen learner and passionate IT student. He has done Web designing, CCNA, RedHat, Ethical hacking, Network & web penetration testing. Currently, he is completing his graduation and learning about Red teaming, CTF challenges & Blue teaming.




