Hey Folks, in this tutorial we will show you how we can find vulnerable URLs through the dork scanner command line tool.
Dork Scanner – Github Tools
If you know about the google dork then you will easily understands. Dork scanning tool built in python and It scrapes web search engines with dorks you provide in order to find vulnerable urls. This is tool is especially designed to find security holes in the server configuration. It is a (CLI) based tool and google (GUI) based tool which is the main difference between the two.
Lets take a look 🙂 !!
Installation
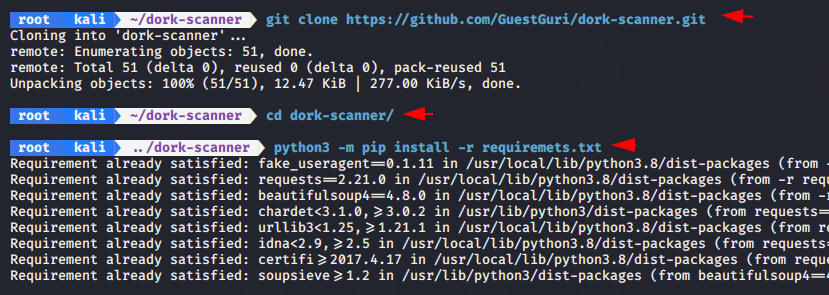
As you know, we have to download it first form the github page.
1 | git clone https://github.com/GuestGuri/dork-scanner.git |
After downloading, the directory will be created on the terminal that we need to access.
1 | cd dork-scanner |
Now we have to fulfill some requirements of this tool for which we will using python and pip tool.
1 | python3 -m pip install -r requiremets.txt |
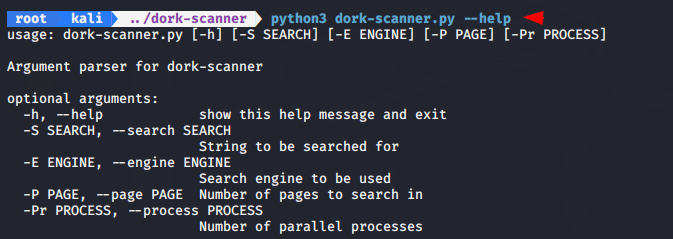
Now we can use this tool by execute the following command.
1 | python3 dork-scanner.py --help |
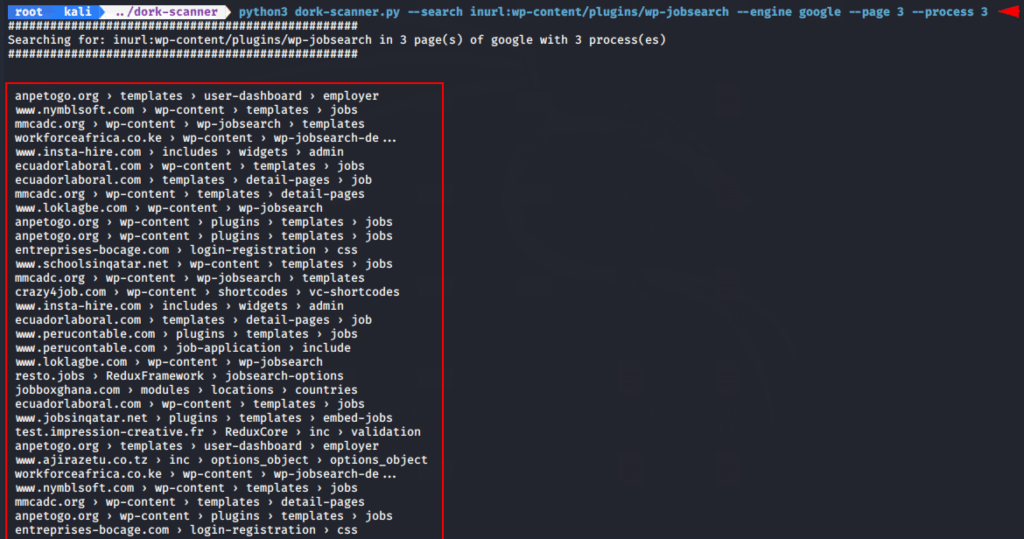
Example -1
In our first attempt, we will try to get websites that have this vulnerable plugin. Due to which we will not have to put more efforts and we will find the more vulnerable website in single search that is advantage of dork.
- —page = Number of pages to search in
- —process = Number of parallel processes
- —gddb = inurl:wp-content/plugins/wp-jobsearch
1 | python3 dork-scanner.py --search inurl:wp-content/plugins/wp-jobsearch --engine google --page 3 --process 3 |
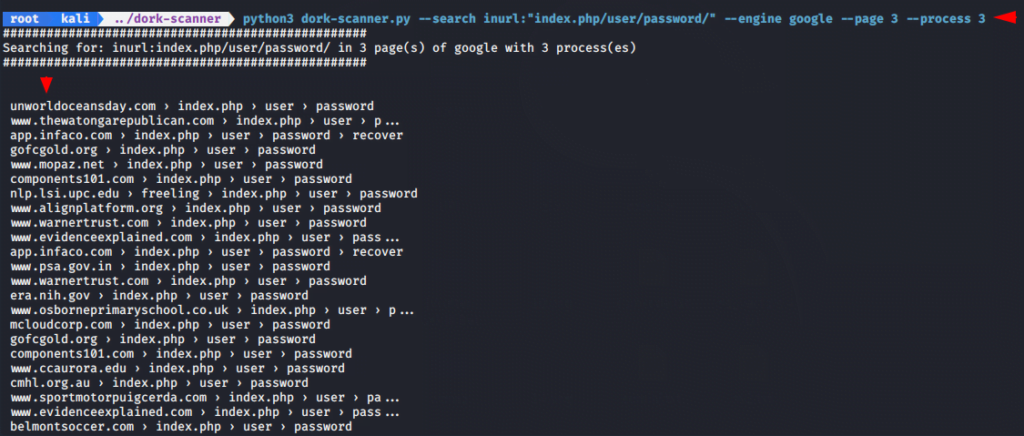
Example -2
In the second attempt we will try to get the hidden password directory from the websites which may be useful to the attacker and this vulnerability as a security checker.
- —gddb = inurl:”index.php/user/password/
1 | python3 dork-scanner.py --search inurl:"index.php/user/password/" --engine google --page 3 --process 3 |
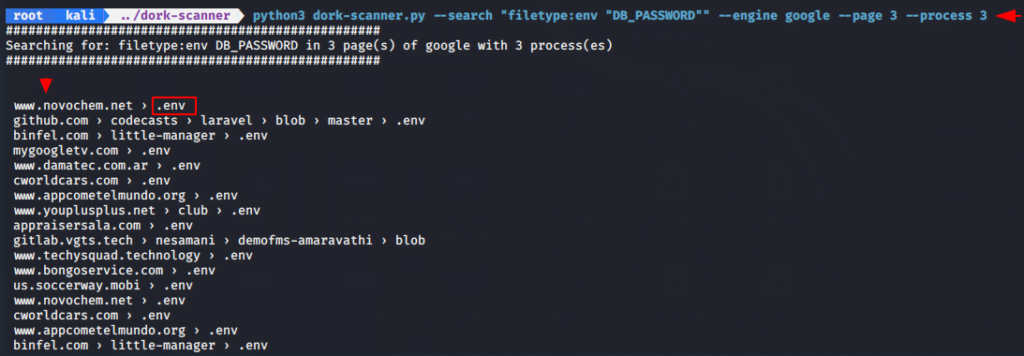
Example -3
We will take another and last example and try to obtain the “.env” file into the websites. As we know that env files allow to put the environment variables inside a file. If the file is accessible then the attacker can exploit that website.
- —gddb = filetype:env “DB_PASSWORD”
1 | python3 dork-scanner.py --search "filetype:env "DB_PASSWORD"" --engine google --page 3 --process 3 |
Therefore we uses Google dork to get valuable and accurate results.
Q = But the question is, where do we get Google dork?
A = For this you can use exploitdb website.




